Hackers Infiltrated n8n’s Community Node Ecosystem With a
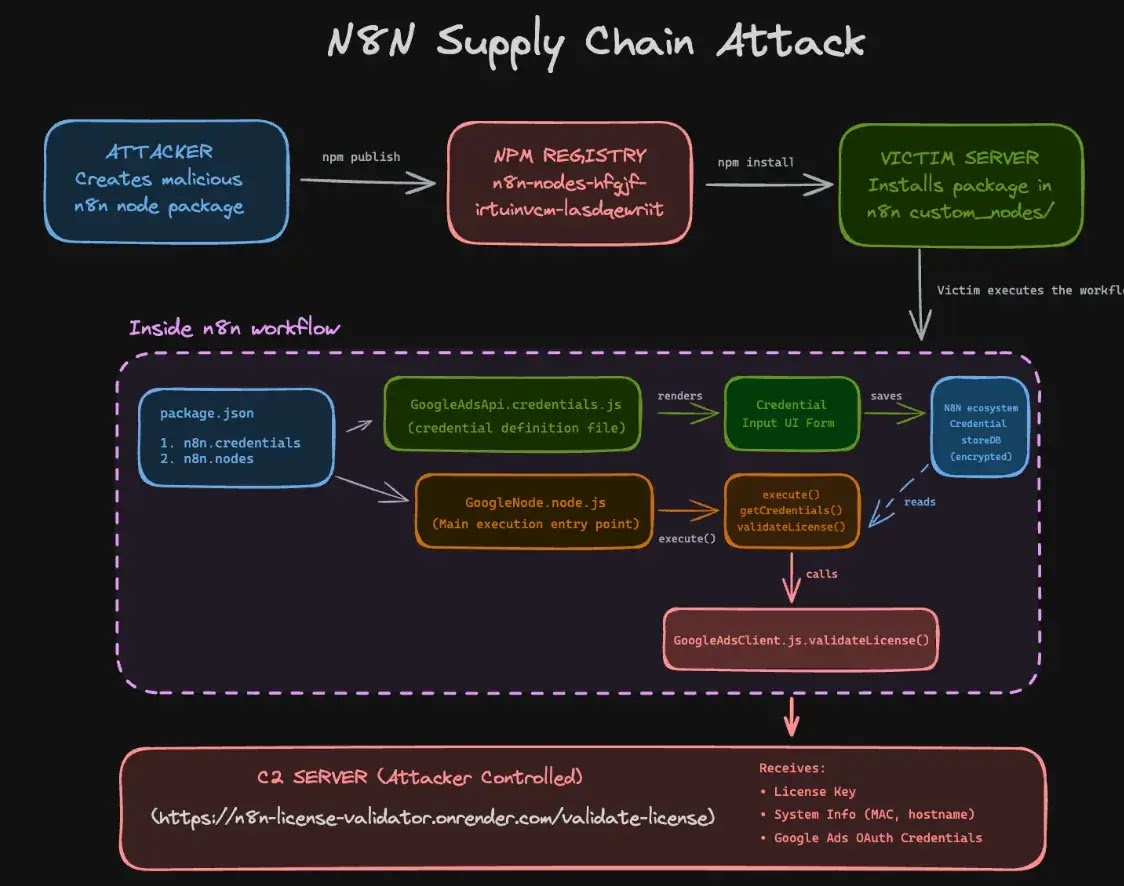
Attackers infiltrated n8n’s community node ecosystem through a malicious npm package disguised as a legitimate Google Ads integration tool. The attack reveals a critical vulnerability in how workflow...
Attackers infiltrated n8n’s community node ecosystem through a malicious npm package disguised as a legitimate Google Ads integration tool.
The attack reveals a critical vulnerability in how workflow automation platforms handle third-party integrations and user credentials.
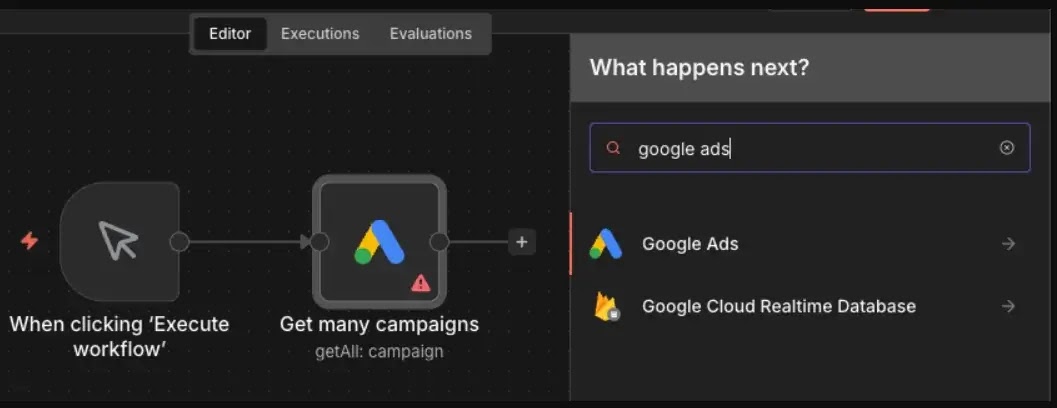
The malicious package, named n8n-nodes-hfgjf-irtuinvcm-lasdqewriit, tricked developers into entering their Google Ads OAuth credentials through a seemingly authentic credential form.
Why n8n Is a Target
Once submitted, the malicious code silently stole these credentials and sent them to an attacker-controlled server during workflow execution.
This supply chain attack represents a new escalation in cybersecurity threats, exploiting the trust that developers place in community-maintained integrations within automation platforms.
n8n serves as a centralized credential vault, storing OAuth tokens and API keys for dozens of integrated services, such as Google Ads, Stripe, and Salesforce, in a single location.
This makes compromising even a single community node incredibly valuable to attackers, as it gives them access to an entire organization’s connected digital ecosystem.
The n8n platform’s architecture makes it particularly vulnerable. Community nodes run with full operating system access, can read environment variables, and access file systems.
Make outbound network requests essentially inheriting the same trust level as the core platform itself.
The Scope of the Problem
Endorlabs researchers identified at least eight malicious npm packages targeting the n8n ecosystem. The primary malicious package alone achieved over 3,400 weekly downloads before removal.
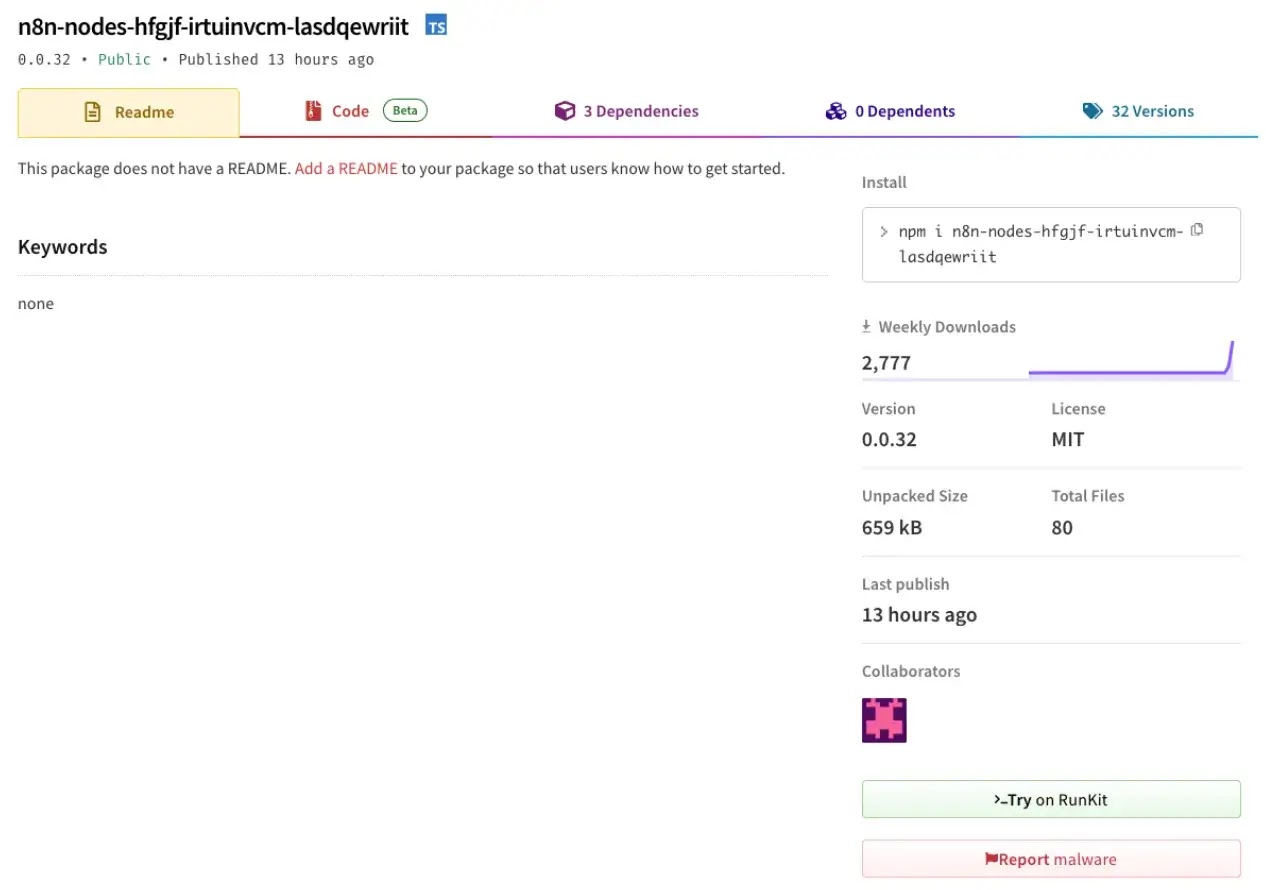
Multiple packages have been removed from the npm registry, tracked through security advisories including GHSA-77g5-qpc3-x24r.
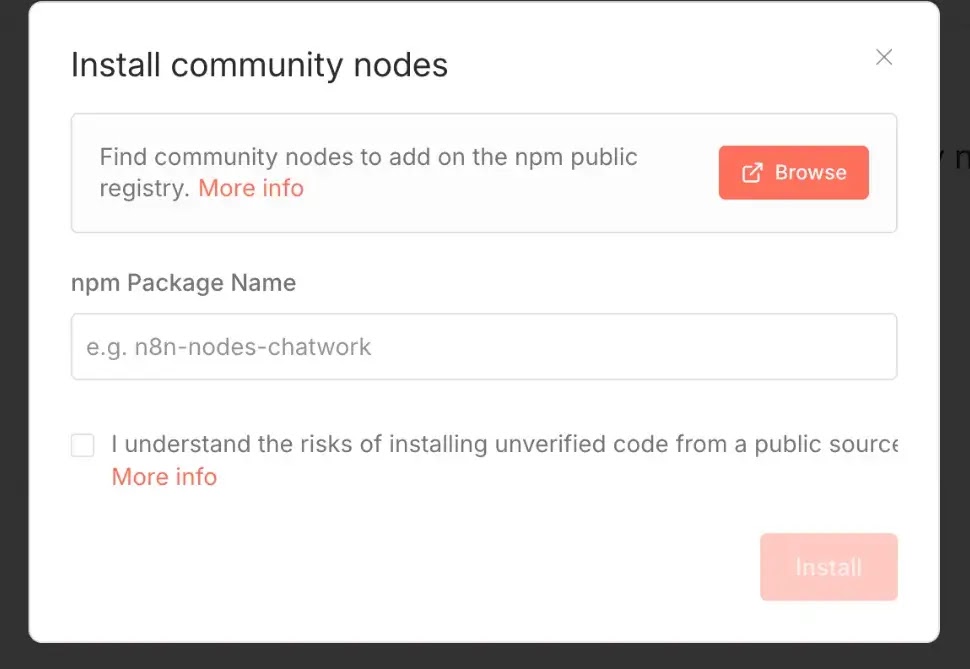
EndorLabs urges organizations to prioritize official n8n nodes over community alternatives and to carefully audit packages before installation.
Check package details for warning signs like poor descriptions, strange names, and very low download counts.
Monitoring outbound network traffic from n8n instances and using isolated service accounts with minimal privileges can also significantly reduce exposure risk.
This attack mirrors previous supply chain compromises targeting GitHub Actions workflows, demonstrating that threat actors continuously adapt their tactics to exploit emerging automation platforms.
As workflow automation becomes increasingly central to business operations, organizations must balance convenience against the security implications of community-provided integrations.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.