InvisibleJS Hides ES Modules in Files via Zero Tool Executable
InvisibleJS, a new open-source tool designed to conceal JavaScript code using invisible zero-width Unicode characters, is raising alarms about its potential for misuse in malware campaigns....
InvisibleJS, a new open-source tool designed to conceal JavaScript code using invisible zero-width Unicode characters, is raising alarms about its potential for misuse in malware campaigns.
InvisibleJS, hosted on GitHub by developer With alias oscarmine, employs steganography to embed source code into seemingly blank files. The process converts JavaScript into binary strings, mapping 0s to Zero Width Space (U+200B) and 1s to Zero Width Non-Joiner (U+200C).
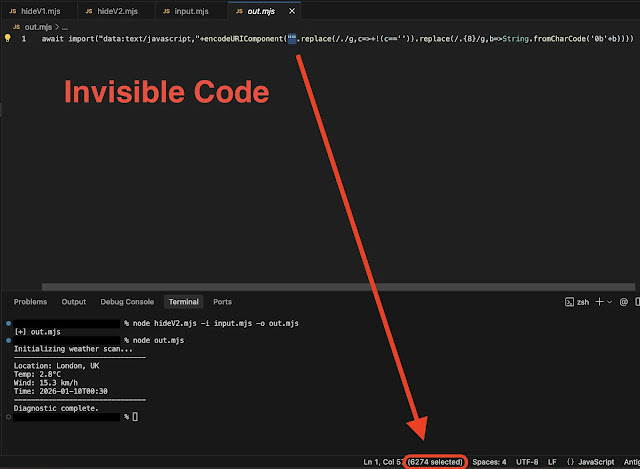
A small bootstrap loader then decodes and runs the hidden payload at runtime, making the code invisible to the naked eye in editors like VS Code.
Two Versions for Different Environments
The repository offers Version 1 (Classic with eval), ideal for CommonJS and legacy Node.js setups, supporting require and module.exports natively.
Version 2 (Modern with import) targets ES Modules, using dynamic await import() for top-level await and exports, though it requires .mjs files or “type”: module configuration.
Hiding code is straightforward via CLI:
- Version 1: node hideV1.mjs -i input.js -o hidden.js
- Version 2: node hideV2.mjs -i input.js -o hidden.js
Execution follows with node hidden.js, producing normal output despite the blank appearance.
| Feature | Version 1 (eval) | Version 2 (import) |
|---|---|---|
| Invisibility | 100% | 100% |
| CommonJS Support | Native | Limited |
| ESM Support | No | Full |
| Top-Level Await | No | Yes |
| Execution | Synchronous | Asynchronous |
| Decoder Length | Short | Long |
This technique echoes prior zero-width JS proofs-of-concept dating back to 2018, now weaponized in phishing attacks. Attackers have abused similar Unicode obfuscation using Hangul characters for binary to hide payloads in scripts, evading scanners with anti-debug checks.
InvisibleJS could amplify such threats, enabling stealthy malware loaders in Node.js environments or web apps, complicating threat detection.
As obfuscation tools proliferate, security teams must enhance Unicode-aware scanning and behavioral analysis. While pitched experimentally, InvisibleJS underscores the dual-use nature of coding innovations in cybersecurity.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.