Hackers Hijack Snap Domains to Poison Linux Software
Attackers are continuing to distribute malicious software through the Canonical Snap Store, leveraging critical security vulnerabilities within the popular Linux package repository. Scammers are...
Attackers are continuing to distribute malicious software through the Canonical Snap Store, leveraging critical security vulnerabilities within the popular Linux package repository.
Scammers are deploying fraudulent cryptocurrency wallet applications that steal digital assets from unsuspecting users.
The campaign involves sophisticated tactics designed to evade detection systems and manipulate trust signals that users rely on when installing software.
The attack targets desktop and server environments where snap packages offer convenient installation methods.
Users downloading these compromised packages believe they are installing legitimate applications, only to discover later that their cryptocurrency wallets have been drained.
The threat extends beyond individual users to organizations managing fleets of Linux systems, where such malware could compromise security infrastructure across multiple machines.
Attackers have refined their approach over time, moving from basic deception to increasingly advanced methods.
Their arsenal now includes applications that mimic genuine cryptocurrency platforms like Exodus and Ledger Live.
When launched, these fake applications collect wallet recovery phrases from users, transmitting credentials to criminal servers in real time.
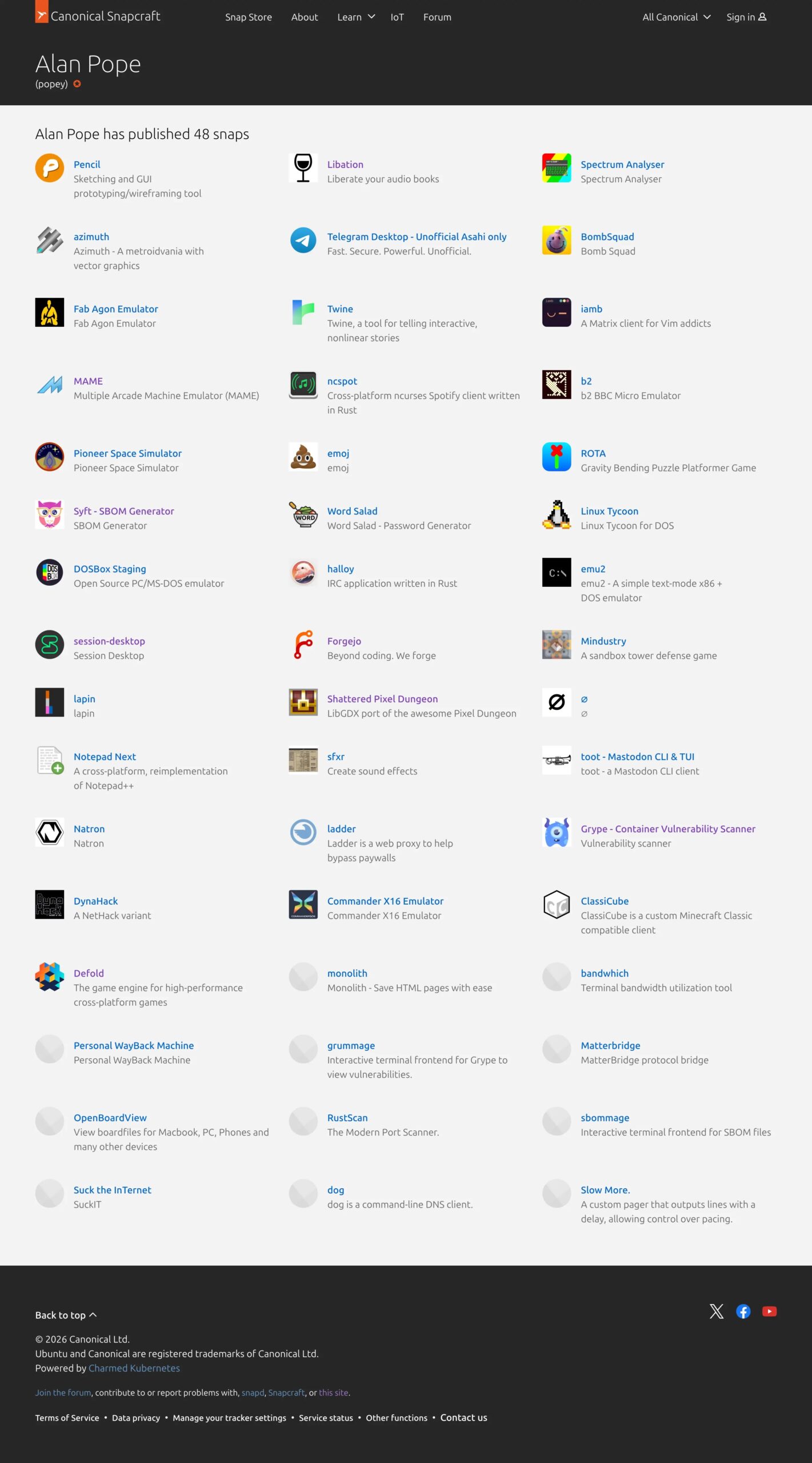
Security analyst Alan Pope identified this escalating threat pattern after investigating suspicious packages within the Snap Store ecosystem.
His research uncovered a coordinated campaign originating from regions near Croatia, revealing the systematic nature of the attack infrastructure.
The Domain Hijacking Mechanism
The most alarming development involves attackers monitoring the Snap Store for abandoned publisher accounts.
When domain registrations expire for legitimate snap publishers, criminals purchase these lapsed domains and exploit the password reset mechanism to take control of established accounts.
This technique proves devastatingly effective because existing applications retain their publisher history and user trust signals.
Rather than creating new accounts that might face scrutiny, attackers push malicious updates to previously trustworthy applications. Users installing updates to snaps they downloaded years ago now face genuine danger.
The attacker simply needs to trigger a password reset using the newly registered domain, gaining complete account access within minutes.
Two identified compromised domains include storewise.tech and vagueentertainment.com, though security professionals suspect additional cases remain undiscovered.
This escalation fundamentally changes the threat landscape. Users previously exercised caution with freshly published applications from new publishers.
Now, that protective behavior provides false security. An application installed three years ago suddenly becomes a delivery mechanism for wallet-stealing malware when its publisher domain expires and attackers claim ownership.
The integrity of the Snap Store depends on immediate action from Canonical to implement domain monitoring, enforce two-factor authentication, and verify account changes originating from dormant publishers.
Until these protections exist, Linux users face genuine risk when installing cryptocurrency applications from any repository.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.