ZAP Releases OWASP PenTest Kit Extension Browser Application
The Zed Attack Proxy (ZAP) team has released version 0.2.0 alpha of its OWASP PTK add-on. This new extension integrates the OWASP Penetration Testing Kit (PTK) browser extension directly into...
The Zed Attack Proxy (ZAP) team has released version 0.2.0 alpha of its OWASP PTK add-on. This new extension integrates the OWASP Penetration Testing Kit (PTK) browser extension directly into browsers launched through ZAP.
This streamlines application security testing by embedding DAST, IAST, SAST, SCA, and specialized tools like JWT and cookie editors without manual setup. Available via the ZAP Marketplace, the add-on pre-installs PTK in Chrome, Edge, and Firefox sessions proxied through ZAP.
Users install the OWASP PTK add-on from ZAP’s Marketplace, then launch a supported browser via ZAP’s feature. The PTK icon appears immediately, allowing login to targets and initiation of scans. ZAP handles traffic capture, site tree, history, and session management, while PTK provides browser-native testing tools.
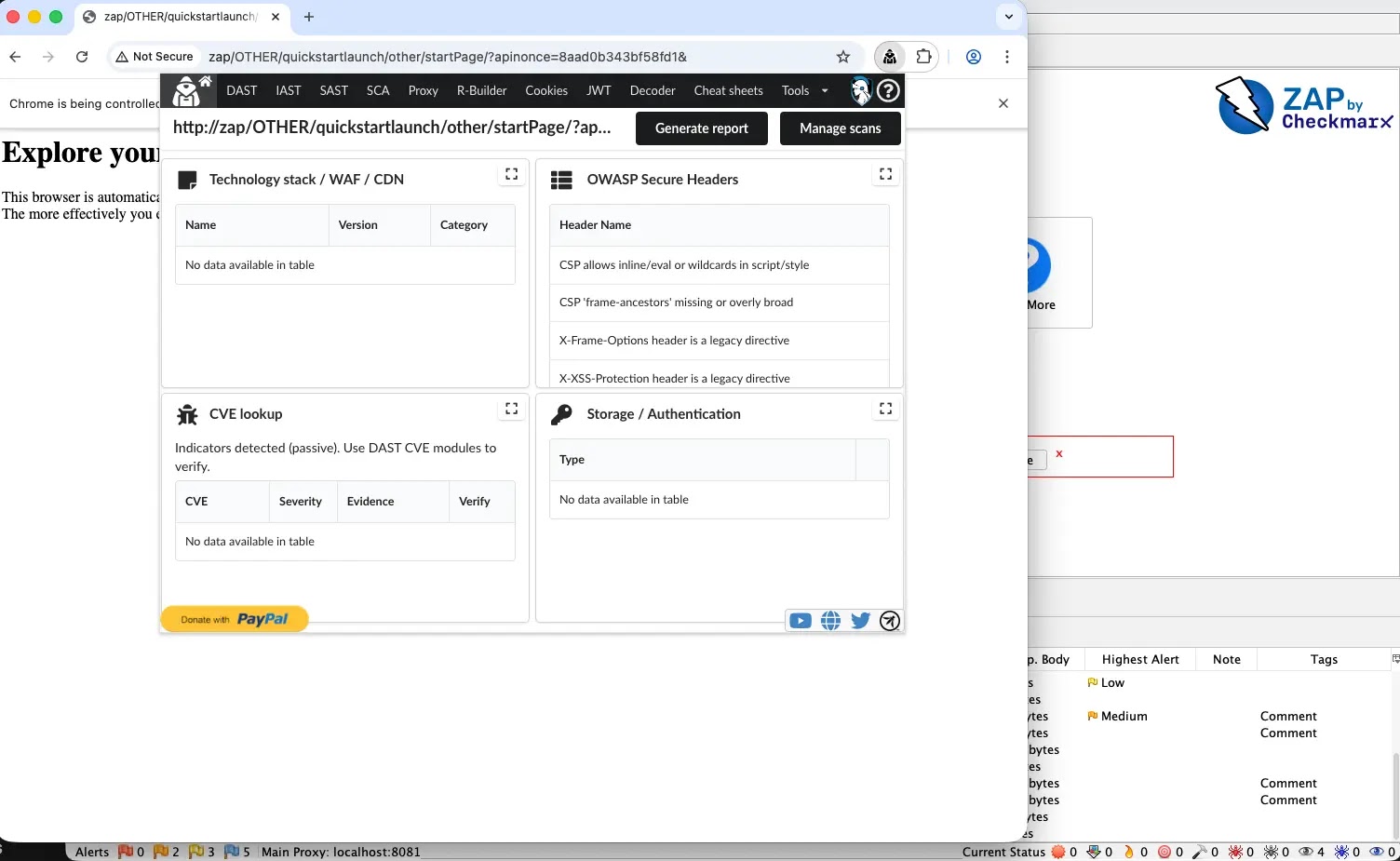
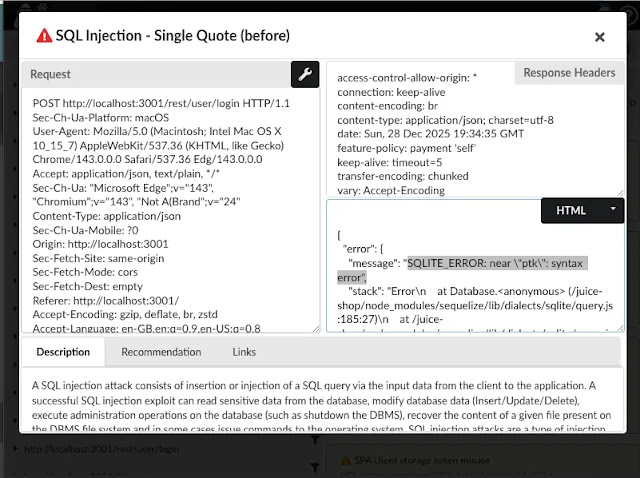
PTK’s DAST enables runtime scans during normal browsing: start scan, navigate key flows like forms and admin pages, stop, and review findings.
Ideal for SPAs reliant on user interactions, it recommends tuning requests per second and concurrency for production stability, with tight domain scoping to minimize noise. Findings integrate with ZAP for re-testing via request tools.
IAST monitors browser runtime behavior, injecting agents during scans for signals beyond response analysis. Start monitoring, browse authenticated routes, then triage DOM mutations and client-side rendering issues.
This excels in UI-state dependent apps, offering quick context for pen testers staying within the browser workflow.
SAST analyzes inline and external scripts loaded in production, spotting sinks and patterns without repo access. Run on current pages, pivot findings to DAST/IAST for validation, especially useful for third-party scripts in SPAs. SCA reveals dependency risks from running apps, reviewing packages with ZAP context for loading behaviors.
Request Builder facilitates rapid iteration: edit traffic from ZAP history, replay attacks, clone as cURL, or manipulate headers. JWT tools decode tokens, alter claims/algorithms, and test enforcement like exp or weak HMAC, replaying via ZAP for response diffs. Cookie tools enable editing, blocking, or exporting for session reproducibility.
A practical routine starts with ZAP-proxied browser login, followed by PTK DAST/IAST during flows, SAST/SCA for static signals, and JWT/cookie validation.
This combo leverages ZAP as the proxy hub and PTK for targeted browser testing, enhancing coverage on modern web apps. Emphasize permission-based active scans and conservative settings.
The release, announced January 19, 2026, marks a milestone in ZAP-PTK synergy, developed with contributions from Denis Podgurskii. Pen testers gain efficient, context-aware testing for authenticated, dynamic applications.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.