PNB MetLife Payment Gateway Steals Details Beware Your
PNB MetLife insurance customers are currently the target of a sophisticated phishing campaign. This scheme employs fake payment gateway pages, designed to steal personal information and redirect...
PNB MetLife insurance customers are currently the target of a sophisticated phishing campaign. This scheme employs fake payment gateway pages, designed to steal personal information and redirect individuals to fraudulent UPI transactions.
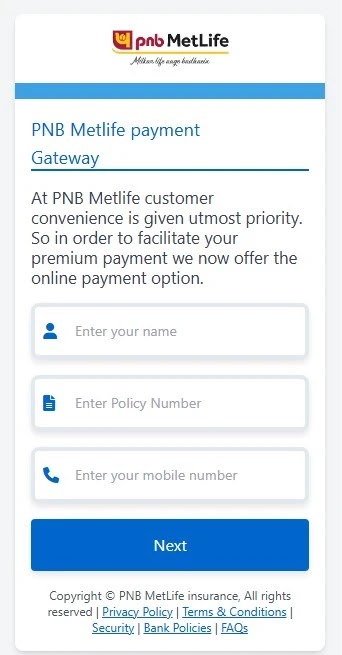
The scam exploits the trusted reputation of PNB MetLife by creating convincing mobile-optimized payment portals that mimic legitimate premium payment services.
These malicious pages accept policy numbers and customer details without any validation, immediately forwarding captured data to attackers through automated channels.
The phishing operation spreads primarily through SMS messages, though email and social media platforms may also serve as distribution channels.
When victims land on these fake payment gateways, they encounter professionally designed interfaces requesting basic information such as name, policy number, and mobile number.
The pages deliberately avoid backend verification, accepting arbitrary values to maintain the illusion of legitimacy while keeping victims engaged in the fraudulent payment flow.
Security researcher Anurag Gawande identified multiple variants of this phishing scheme while conducting threat-hunting activities. His investigation revealed that attackers deployed these pages across free hosting platforms, particularly EdgeOne Pages, enabling rapid deployment and rotation of malicious sites.
The campaign demonstrates a clear evolution in financial fraud tactics, moving beyond simple credential theft to multi-stage operations that combine data exfiltration with direct payment manipulation.
The attack begins innocuously but quickly escalates as victims progress through seemingly legitimate payment steps. Once initial details are captured, the phishing page transitions to a payment amount collection stage before introducing UPI-based payment mechanisms.
This gradual progression builds false confidence while systematically harvesting different layers of information from unsuspecting customers.
What makes this threat particularly dangerous is its use of real payment applications to complete fraudulent transactions.
Rather than relying solely on fake payment processors, the scheme leverages legitimate UPI apps like PhonePe, Paytm, and Google Pay, significantly reducing victim suspicion while increasing the likelihood of successful financial theft.
Stealthy Data Theft Through Telegram Infrastructure
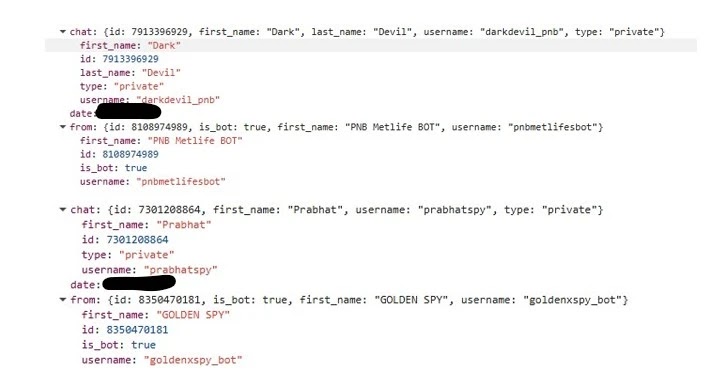
Behind the polished interface lies a sophisticated data exfiltration mechanism powered by Telegram Bot API.
When victims submit their information, the phishing page silently transmits captured details directly to attacker-controlled Telegram channels instead of any legitimate payment backend.
This real-time data theft occurs invisibly, with hardcoded bot tokens and chat IDs embedded within the page’s JavaScript code.
Investigation into the phishing infrastructure uncovered multiple Telegram bots and operator accounts coordinating the fraud.
Bots named “pnbmetlifesbot” and “goldenxspy_bot” collect victim submissions, while accounts such as “darkdevil_pnb” and “prabhatspy” monitor and receive stolen information.
The stolen data includes names, policy numbers, and mobile numbers, all transmitted instantly as victims complete each form field.
After initial data capture, the page requests payment amounts without performing any policy validation, accepting any value entered before forwarding this information to the same Telegram channels.
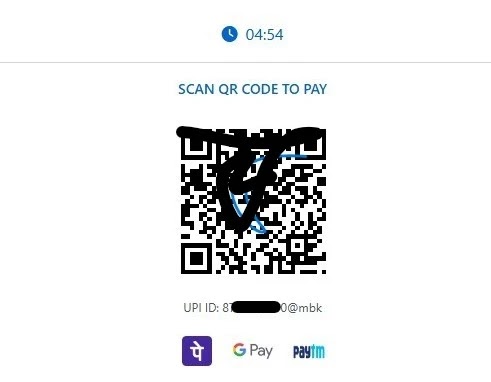
The phishing flow then introduces urgency through countdown timers and QR code displays, pressuring victims to complete UPI payments quickly.
The JavaScript generates UPI payment URIs dynamically, rendering them as scannable QR codes that direct funds to attacker-controlled accounts.
More concerning is the clipboard abuse technique employed when victims select payment app buttons.
Clicking PhonePe or Paytm buttons silently copies the fraudulent UPI ID to the device clipboard before redirecting to the legitimate payment app, ensuring the attacker’s payment details are ready to paste even if victims ignore the QR code.
Advanced variants of this phishing campaign escalate beyond simple payment fraud into comprehensive banking credential harvesting.
These sophisticated templates offer multiple options including “Update Amount,” “Refund Your Amount,” and “Add AutoDebit System,” creating the illusion of legitimate policy servicing.
When victims select these options, they eventually encounter pages requesting complete bank account details and debit card information, including card numbers, expiry dates, and CVV codes.
All submitted financial credentials are exfiltrated through the same Telegram infrastructure, transforming the operation from payment fraud into full-scale identity and financial data theft.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.