Hackers Exploited Routing & Misconfigurations to Spoof Or
Phishing actors are exploiting complex routing scenarios and misconfigured security protections to send fake emails that appear to originate from within targeted organizations. These emails look like...
Phishing actors are exploiting complex routing scenarios and misconfigured security protections to send fake emails that appear to originate from within targeted organizations.
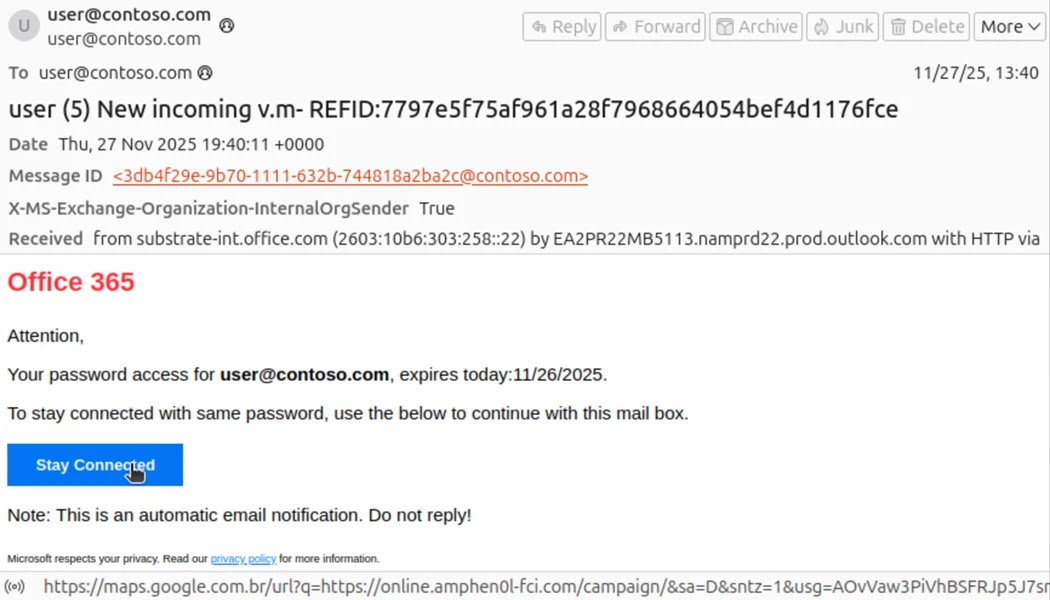
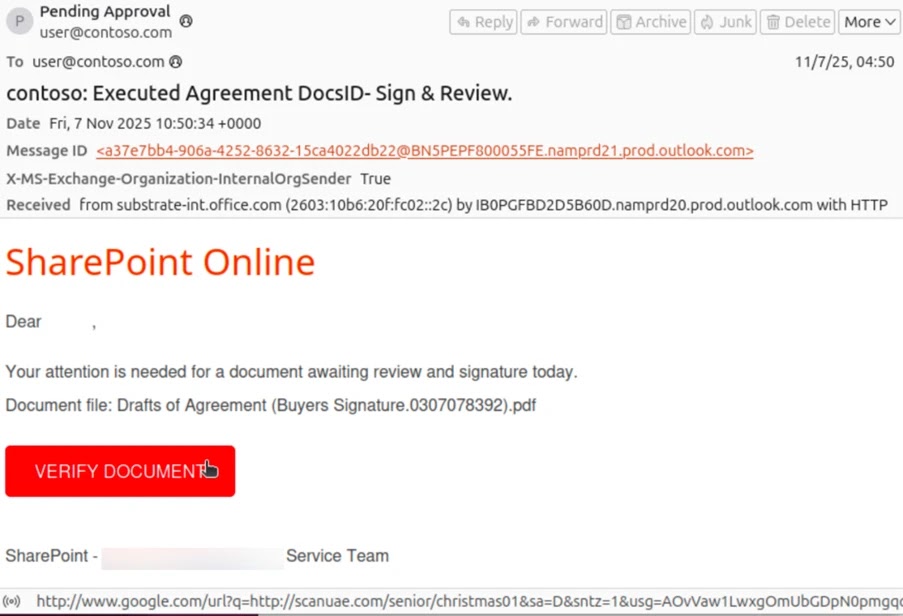
These emails look like they were sent internally, making them harder to detect. Threat actors have used this method to deliver various phishing messages through platforms like Tycoon2FA.
The emails use common tricks, including voicemail alerts, shared documents, human resources communications, and password reset notices to steal login credentials.
This attack method has been around for a while but became more visible and widely used since May 2025. The phishing campaigns using this technique are not targeted at specific organizations but are sent widely across many industries.
Researchers also found campaigns using this method to trick companies into paying fake invoices. These attacks work differently from regular phishing because they abuse complex email routing and poorly configured security settings.
Organizations whose Microsoft Exchange mail exchanger records point directly to Office 365 are protected by built-in security features and are not affected by this attack vector.
Phishing emails sent this way can be more successful because they look like internal messages. Microsoft Threat Intelligence researchers noted that successful attacks can lead to stolen data or business email compromise attacks against the affected organization or its partners.
These incidents may require significant cleanup efforts and can cause financial losses in the case of invoice scams.
While Microsoft detects most of these phishing attempts, organizations can reduce their risk by properly setting up security protections and configuring third-party email connectors to prevent fake emails from reaching employee inboxes.
Technical Breakdown of Email Authentication Failures
The attacks take advantage of situations where organizations have set up complex email routing scenarios with mail exchanger records that do not point directly to Office 365.
When organizations have not configured strict security protections, threat actors can send fake phishing emails that appear to come from the organization’s own domain.
Email headers reveal important information about these spoofed messages, such as external IP addresses used by attackers to start the phishing attack.
Based on how the email system is configured, security checks like SPF will show soft or hard fail, DMARC will fail, and DKIM will equal none because both the sender and recipient appear to be in the same domain.
The X-MS-Exchange-Organization-InternalOrgSender header will be set to True, but X-MS-Exchange-Organization-MessageDirectionality will be set to Incoming and X-MS-Exchange-Organization-ASDirectionalityType will have a value of “1”, showing that the message came from outside the organization.
The combination of an internal organization sender marker and incoming direction indicates a message faked to look like internal communication.
The X-MS-Exchange-Organization-AuthAs header will be set to Anonymous, confirming that the message came from an external source.
Setting strict Domain-based Message Authentication, Reporting, and Conformance reject policies and SPF hard fail policies instead of soft fail, along with properly configuring third-party connectors, will prevent phishing attacks that try to fake organization domains.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.