Black Cat Hackers Use Fake Notepad++ Sites Group Install
The notorious Black Cat cybercriminal group has aggressively resurfaced, launching a sophisticated malware campaign that leverages advanced search engine optimization techniques to distribute...
The notorious Black Cat cybercriminal group has aggressively resurfaced, launching a sophisticated malware campaign that leverages advanced search engine optimization techniques to distribute counterfeit versions of popular open-source software.
By manipulating search engine algorithms, the gang successfully positions meticulously crafted phishing websites for tools like Notepad++ at the very top of keyword search results.
This strategic placement ruthlessly exploits user trust in familiar platforms, leading unsuspecting victims to download malicious installers that are secretly bundled with dangerous remote control backdoors capable of stealing sensitive host data.
When users navigate to these fraudulent domains, they encounter a highly realistic interface that mirrors legitimate software repositories, often featuring numerous tutorial articles to artificially enhance credibility.

The deceptive download process deliberately involves multiple redirects, eventually guiding the user to a fake page styled to resemble GitHub.
This layering of legitimacy is designed to lower victim suspicion effectively before delivering the compromised software payload to the host system.
Weixin analysts noted that this rampant campaign successfully compromised approximately 277,800 servers effectively between early and late December 2025.
The malware’s primary objective remains the covert exfiltration of highly sensitive information, including browser user data, real-time keystroke logs, and clipboard contents.
This extensive data theft poses severe and immediate security risks to both individual users and larger organizational infrastructures exposed to the threat.
Infection and Execution Mechanism
The malware’s infection process is technically intricate. Upon initial execution, the installer creates a deceptive shortcut on the victim’s desktop, which points directly to the backdoor’s entry point instead of the actual application.
The malware cleverly employs a white and black execution strategy, utilizing a benign executable to load a malicious DLL component.
This DLL is specifically tasked with locating and decrypting a concealed encrypted file named M9OLUM4P.1CCE. While the malicious DLL file decrypts and executes encrypted file.
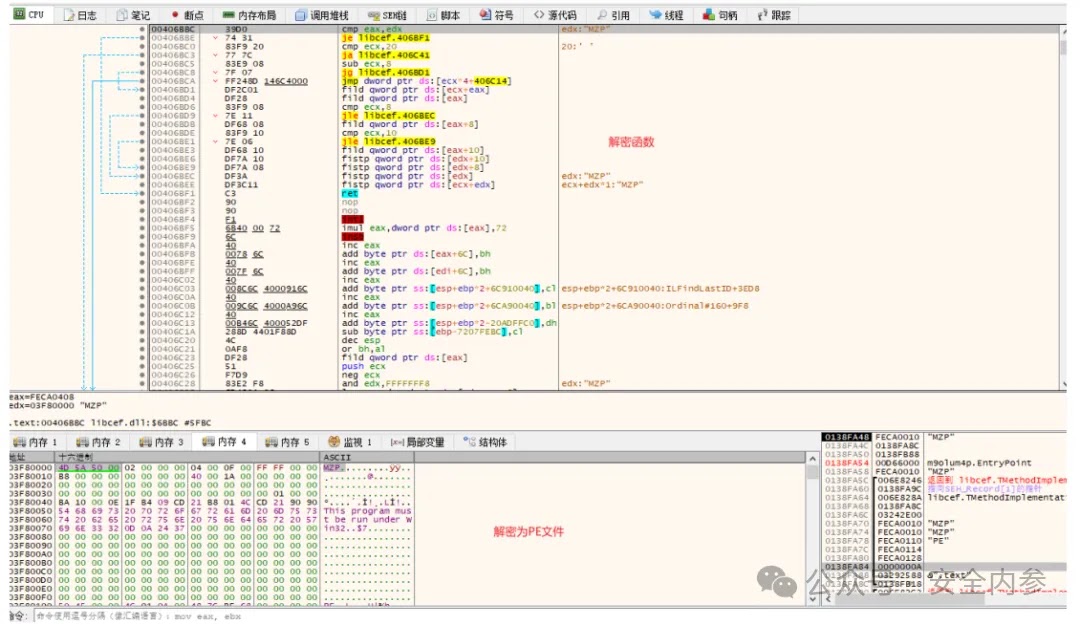
Following the successful decryption process, the malicious PE file is loaded directly into the system’s memory via reflection, a tactic that helps bypass standard disk-based detection mechanisms.
The malware ensures its longevity by creating specific registry startup items and immediately initiates communication with its command-and-control server, hardcoded as sbido.com:2869.
This persistent connection facilitates the continuous transmission of stolen data, while the domain’s resolution IP is frequently updated by the attackers to evade static network-based blocking measures.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.