Hackers Exploit Next.js React2Shell Flaw to Steal Credentials From
A critical security flaw, dubbed React2Shell, is under active exploitation by attackers targeting web applications built on the widely used Next.js framework. This cyberattack campaign is rapidly...
A critical security flaw, dubbed React2Shell, is under active exploitation by attackers targeting web applications built on the widely used Next.js framework. This cyberattack campaign is rapidly impacting websites across the internet.
In just 24 hours, attackers broke into 766 servers and walked away with massive amounts of sensitive data, including passwords, cloud keys, and database credentials.
The vulnerability at the center of this attack is CVE-2025-55182, widely known as React2Shell. Rated a maximum severity score of 10.0 on the CVSS scale, the flaw exists in the React Server Components (RSC) Flight protocol, specifically in how a React server processes HTTP requests to Server Function endpoints.
A single crafted HTTP request is enough for an attacker to execute code on the server with no authentication required. Next.js also received a separate tracking number, CVE-2025-66478, given its significant downstream exposure to this flaw.
Cisco Talos researchers identified this automated operation and tied it to a threat cluster they are now tracking as UAT-10608.
The campaign is both systematic and indiscriminate, with attackers using scanning services such as Shodan or Censys to sweep the internet for publicly reachable Next.js deployments running vulnerable versions of React Server Components.
Once a target is located, the entire attack runs on its own, requiring no manual interaction after the initial exploit fires.
The scale of damage is significant. Across multiple geographic regions and cloud providers including AWS, Google Cloud, and Microsoft Azure, at least 766 hosts were confirmed breached within a single 24-hour window.
Stolen material included database connection strings, SSH private keys, cloud access tokens, GitHub tokens, Stripe live secret keys, Kubernetes service account credentials, environment variables, and shell command histories.
More than 10,120 files in total were collected from the compromised systems. The reach of this campaign extends well beyond immediate account takeover.
Several breached hosts exposed package registry authentication files, including npm and pip configuration files that carried registry credentials.
If attackers use these tokens to push malicious versions of trusted software packages, the harm can reach any organization that installs those packages, turning this into a genuine supply chain threat.
The NEXUS Listener: How Stolen Data Is Controlled at Scale
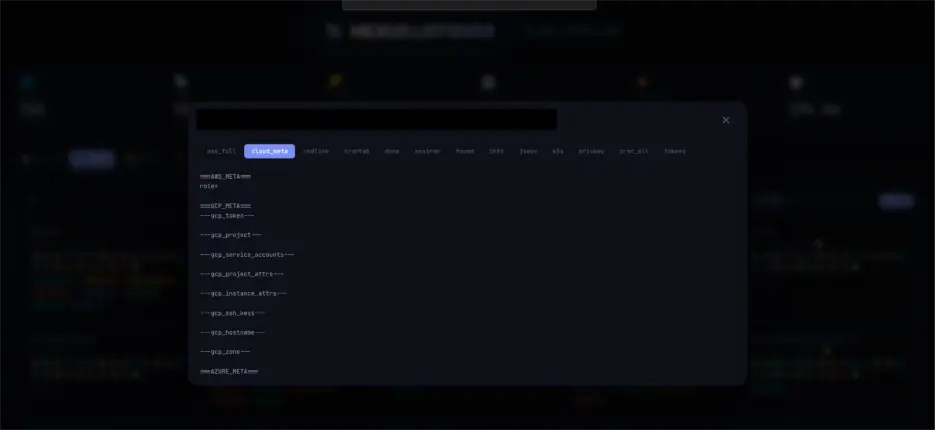
To manage the flood of stolen information pouring in from hundreds of servers, UAT-10608 deployed a custom command-and-control framework called NEXUS Listener.
This web-based platform, currently at version 3, provides operators with a graphical dashboard where they can browse compromised hosts, sort stolen credentials by category, review harvesting statistics, and check how many credentials were successfully extracted in each attack phase.

The attack begins when a vulnerable endpoint is identified and a single malicious HTTP request is sent to the RSC Server Function endpoint.
The server deserializes the crafted payload and runs arbitrary code, dropping a lightweight shell script into a temp directory under a randomized file name to stay hidden.
That dropper then retrieves a multi-phase credential harvesting script from the attacker’s infrastructure.

Each phase collects a different type of data, from SSH keys and cloud tokens to database passwords, and reports back to the NEXUS Listener C2 server on port 8080, including the victim’s hostname and a phase identifier.
No further human interaction is needed, which is how UAT-10608 breached hundreds of systems so quickly.
Organizations running Next.js with App Router or any implementation of React Server Components should apply patches to the latest available version without delay.
All secrets in potentially affected environments, including AWS keys, database passwords, SSH keys, API tokens, and GitHub tokens, must be rotated immediately.
Teams should audit containers for overly permissive roles, enforce IMDSv2 on cloud instances, and stop reusing SSH key pairs across different systems.
Monitoring outbound HTTP traffic from application containers, especially unexpected connections to unknown IPs on port 8080, is a practical and important step toward catching an active breach early.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.








No Comment! Be the first one.