Google Warns: Hackers Exploit Gemini AI in Leveraging Stages
Google’s Gemini API is now being leveraged by threat actors to dynamically generate C# code. This new approach enables the creation of multi-stage malware capable of evading traditional...
Google’s Gemini API is now being leveraged by threat actors to dynamically generate C# code. This new approach enables the creation of multi-stage malware capable of evading traditional detection methods.
The Google Threat Intelligence Group (GTIG) detailed this in its February 2026 AI Threat Tracker report, spotlighting the HONESTCUE framework first observed in September 2025.
HONESTCUE operates as a downloader and launcher that queries Gemini’s API with hard-coded prompts to fetch self-contained C# source code. This code implements stage-two functionality, such as downloading payloads from URLs hosted on CDNs like Discord, without leaving disk artifacts.
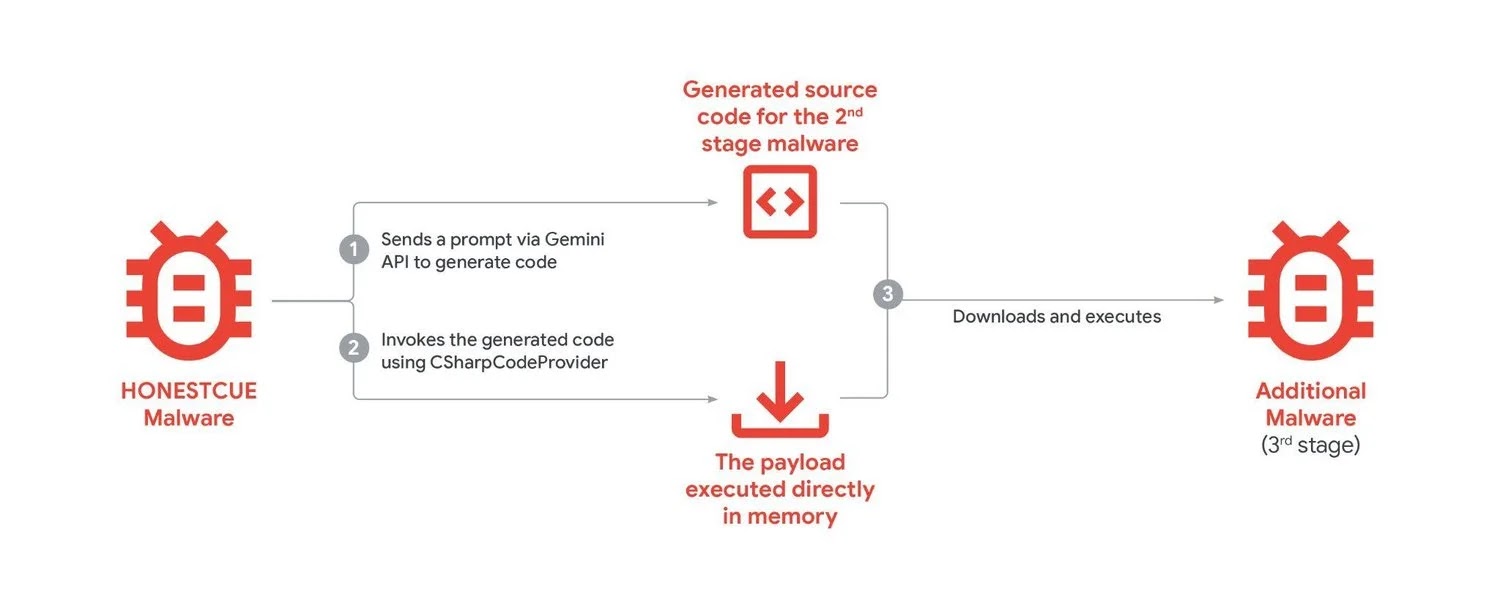
The malware then employs the legitimate .NET CSharpCodeProvider to compile and execute the received code directly in memory, complicating static analysis and behavioral detection.
Developers iteratively refined samples, submitting them to VirusTotal via a single account, suggesting a small team in proof-of-concept testing.
Prompts appear benign out of context, for instance, one requests a simple “AITask” class printing “Hello from AI-generated C#!”, while others specify “Stage2” classes using WebClient for URL downloads, temp file writes, or in-memory Assembly.
Threat Actors Leverage Gemini
The process unfolds in layers:
- API Call: Malware sends a static prompt to Gemini, receiving compilable C#.
- Dynamic Compilation: CSharpCodeProvider processes the response into an executable assembly.
- Payload Delivery: Stage two fetches bytes from attacker-controlled URLs, often via Discord CDN, then launches via Process. Start or reflection.
- Fileless Persistence: No binaries hit disk, undermining endpoint forensics.
This mirrors prior “just-in-time” techniques like PROMPTFLUX, but outsources generation externally. GTIG notes the prompts evade Gemini’s safeguards since they lack explicit malice, blending into legitimate dev queries.
Threat actors integrate Gemini across phases, from reconnaissance to tooling. GTIG tracked misuse by DPRK, Iranian (APT42), PRC (APT31, UNC795, APT41), and Russian groups for phishing, vulnerability research, and C2 scripting.
For example, APT31 role-played a “security researcher” to probe RCE and WAF bypasses. While no APTs achieved paradigm-shifting breakthroughs, productivity gains accelerate operations.
HONESTCUE’s design avoids detection by traditional signature-based antivirus software and network filters by varying the code it generates with each execution. Evidence suggests that the actors behind this have only modest skills.
Tests conducted with Discord bots and repeated uploads to VirusTotal indicate that they possess limited resources, especially when compared to the sophistication typically seen in advanced persistent threats (APTs), according to the Google Threat Intelligence Group (GTIG).
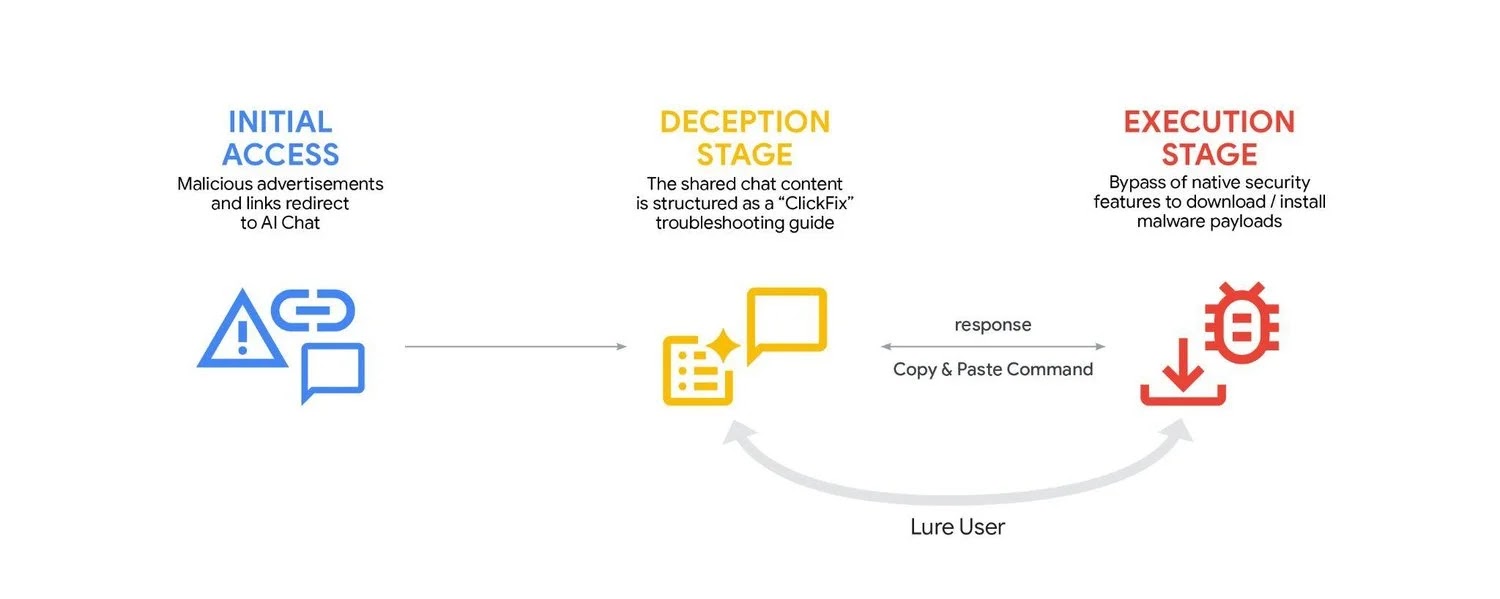
Additionally, a broader trend includes Xanthorox, which is an underground “custom AI” that proxies jailbroken Gemini through MCP servers.
| Phase | Key Evasion Tactic | Detection Hurdle |
|---|---|---|
| Stage 1 | Gemini API query | Legit traffic to googleapis.com |
| Stage 2 | In-memory compile | No disk IO |
| Stage 3 | CDN payload | Trusted domains like Discord |
Google disrupted via account disables, model hardening, and real-time classifiers. Gemini now refuses policy-violating requests, informed by these incidents. Defenders should monitor API anomalies (high-volume code-gen queries), block anomalous Gemini traffic, and inspect in-memory .NET loads.
Behavioral rules for CSharpCodeProvider usage or Discord CDN fetches from malware IOCs help. GTIG shares IOCs in GTI Collections for hunters. As AI tooling proliferates, hybrid defenses blending network telemetry and runtime inspection grow essential.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.