Lazarus Graphalgo Fake Recruiter Spreads Malware via
North Korean state-sponsored hackers, the Lazarus Group, have initiated a sophisticated fake recruiter campaign, dubbed ‘graphalgo,’ directly targeting cryptocurrency developers. Active...
North Korean state-sponsored hackers, the Lazarus Group, have initiated a sophisticated fake recruiter campaign, dubbed ‘graphalgo,’ directly targeting cryptocurrency developers.
Active since May 2025, this coordinated attack uses fraudulent job offers to distribute remote access trojans to unsuspecting developers working with blockchain and cryptocurrency technologies.
The campaign exploits trusted open-source package repositories including GitHub, npm, and PyPI, turning legitimate development workflows into infection vectors.
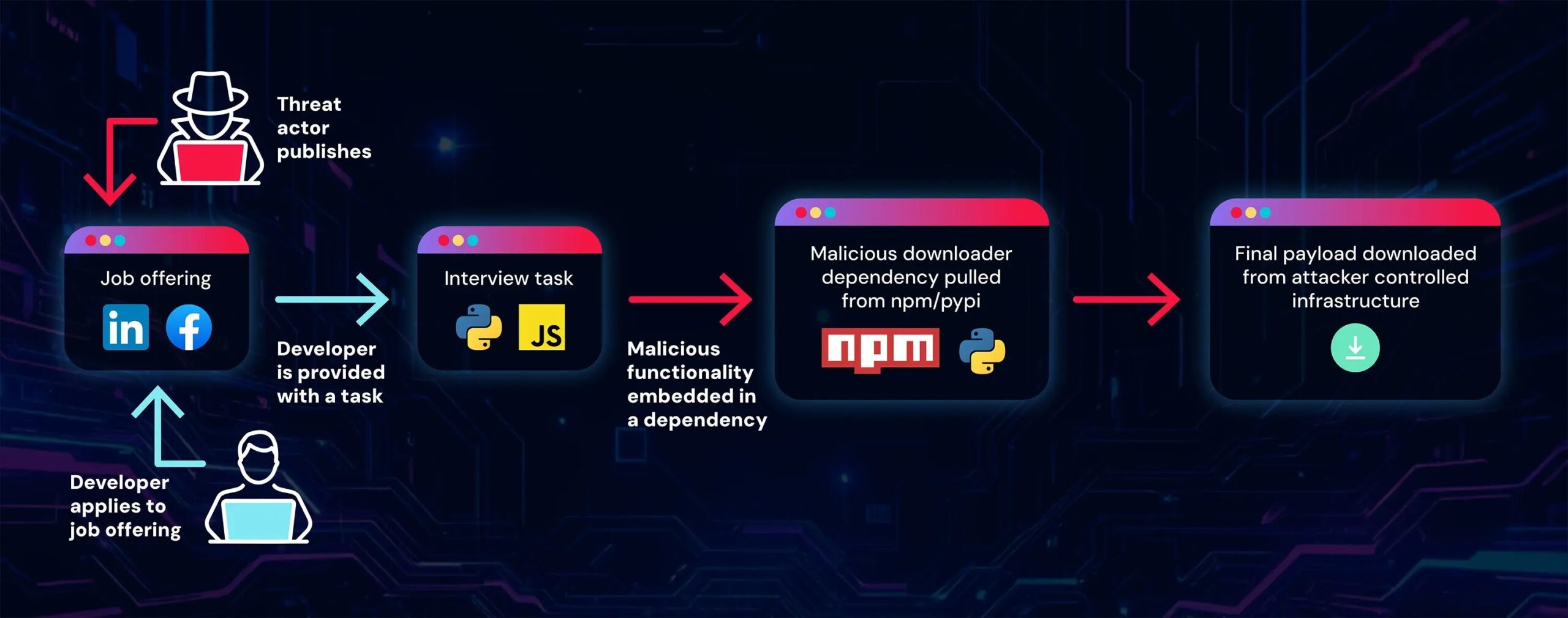
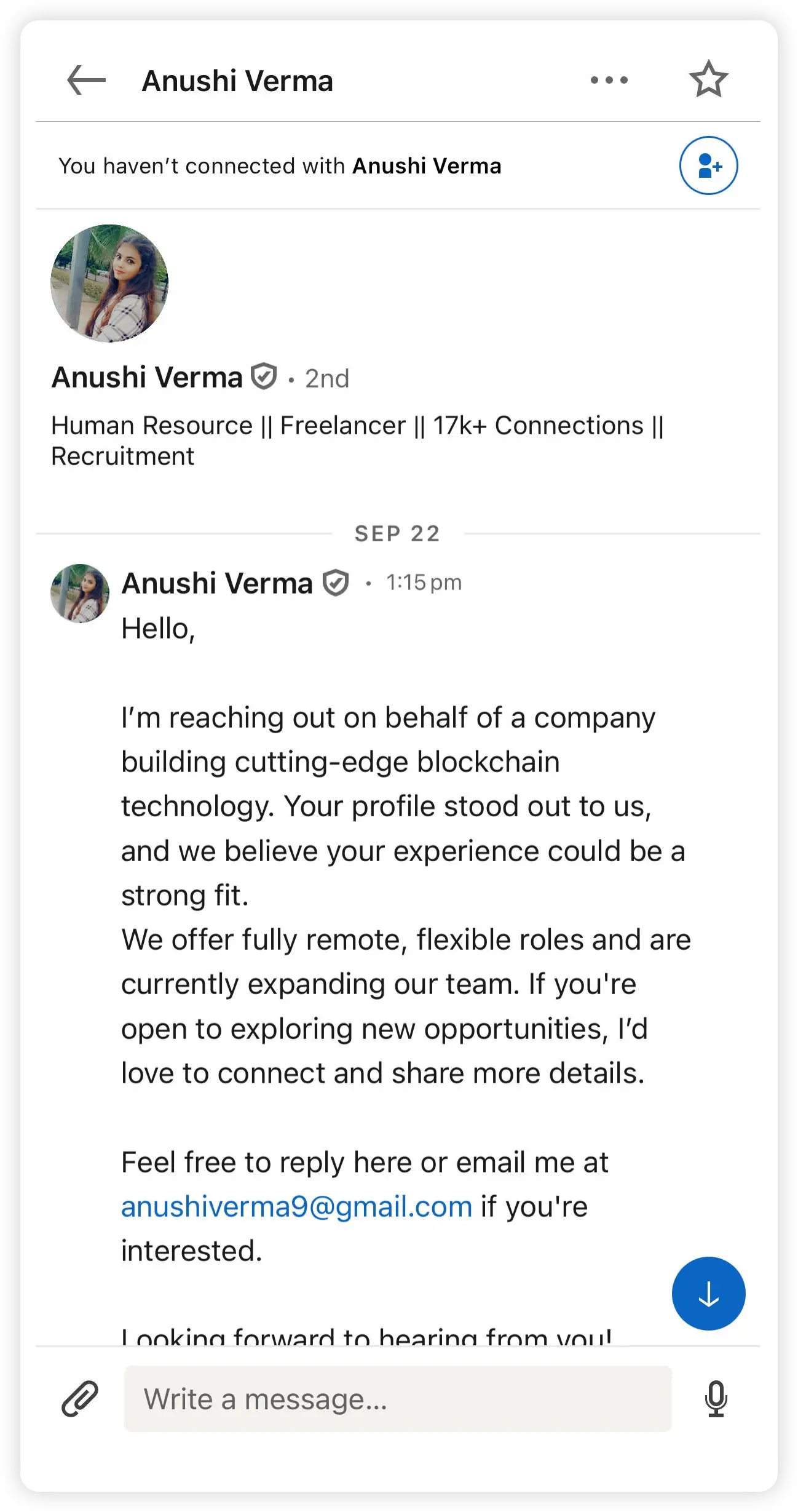
Attackers approach potential victims through professional networking platforms like LinkedIn and Facebook, or by posting job advertisements on developer forums such as Reddit.
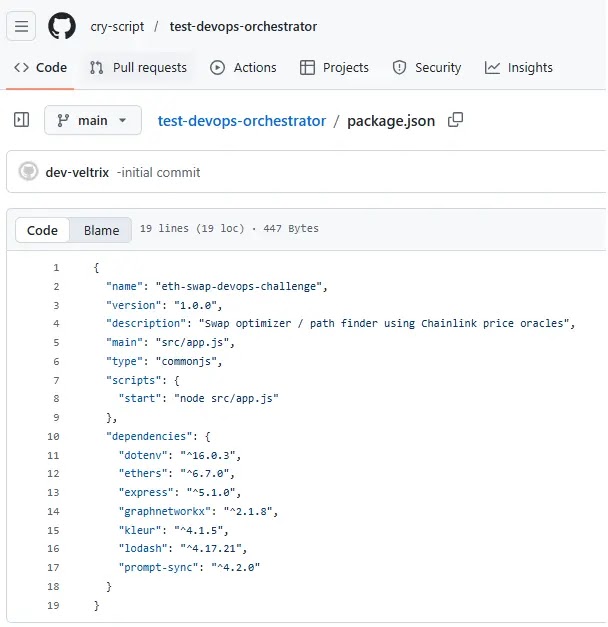
The social engineering scheme revolves around employment opportunities at fake companies involved in blockchain and cryptocurrency exchanges, most notably “Veltrix Capital.”
Victims receive coding test assignments that appear legitimate but contain hidden malicious dependencies designed to compromise their systems upon execution.
What makes this campaign particularly dangerous is its modular architecture, which allows threat actors to maintain operations even when portions are exposed.
This new branch of the fake recruiter campaign has been identified by ReversingLabs researchers and named it after the first malicious package discovered in the npm repository.
Their analysis revealed that the npm package “bigmathutils” accumulated over 10,000 downloads before a weaponized version was released, demonstrating patience characteristic of state-sponsored operations.
Infection Mechanism and Multi-Stage Payload Delivery
The infection process begins when developers receive job interview tasks through GitHub repositories controlled by the fake companies.
These repositories contain coding assignments for DevOps or blockchain positions. However, embedded within project files are dependencies pointing to compromised packages hosted on npm and PyPI repositories.
When victims run or debug the interview code, package managers automatically install these malicious dependencies.
The packages include multiple obfuscation layers and encrypted payloads that download second-stage malware from command-and-control servers.
The final payload is a fully functional RAT capable of executing arbitrary commands, uploading files, listing processes, and checking for the MetaMask browser extension—indicating interest in stealing cryptocurrency funds.
Three versions of the RAT have been identified, written in JavaScript, Python, and Visual Basic Script. The malware communicates with C2 servers using token-protected authentication, preventing security researchers from analyzing server responses.
This token mechanism has been observed in other North Korean campaigns, strengthening attribution to Lazarus Group.
The presence of GMT+9 timezone timestamps in git commits and cryptocurrency-focused social engineering align with established North Korean threat actor patterns.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.