ZionSiphon Malware Targets Israeli Desal Hackers Desalination
A newly identified piece of malware, dubbed ZionSiphon, has sparked considerable concern over the security of Israel’s critical water infrastructure, particularly its vital desalination plants....
A newly identified piece of malware, dubbed ZionSiphon, has sparked considerable concern over the security of Israel’s critical water infrastructure, particularly its vital desalination plants. A
ZionSiphon is not a random piece of software. It carries hardcoded Israeli IP address ranges, meaning it is designed to run only on systems located within Israel.
The malware includes geographically restricted execution logic targeting IP blocks tied to Israeli networks, along with politically motivated messages embedded in its code.
One decoded string reads, “In support of our brothers in Iran, Palestine, and Yemen against Zionist aggression. I am 0xICS.”
Another decoded message references “Poisoning the population of Tel Aviv and Haifa,” pointing to a threat actor with clear ideological intent and a desire to cause real physical harm.
Darktrace analysts recently identified and examined the malware sample, which self-identifies as ZionSiphon.
Their investigation revealed that this tool combines several host-based capabilities, including privilege escalation, persistence mechanisms, USB-based propagation, and scanning for Operational Technology (OT)-relevant services on local networks.
The Darktrace team noted that while many of these individual features are found in everyday commodity malware, the combination of politically charged messaging, Israel-specific targeting, and an explicit focus on desalination processes makes ZionSiphon stand out from generic opportunistic attacks.
The malware’s target list includes the names of real Israeli water infrastructure entities.
These include Mekorot, which is Israel’s national water company, along with Sorek, Hadera, Ashdod, and Palmachim, which are four of the country’s major seawater desalination plants.
The Shafdan wastewater treatment facility is also listed. Each of these sites plays a critical role in Israel’s national water supply, and their presence in the malware’s targeting list confirms that the attacker understands the structure of the country’s water sector.
The most alarming part of ZionSiphon is its sabotage logic. When the malware confirms it is running in a valid water treatment environment, it attempts to tamper with local configuration files by injecting values such as “Chlorine_Dose=10,” “Chlorine_Pump=ON,” “Chlorine_Flow=MAX,” “Chlorine_Valve=OPEN,” and “RO_Pressure=80.”
These entries, if successfully written to active system configuration files, could manipulate chlorine dosing and pressure levels in ways that could make water unsafe for human consumption.
Infection Mechanism and OT Protocol Targeting
Once ZionSiphon gains a foothold on a system, it begins a structured process of establishing itself quietly and scanning for industrial control devices.
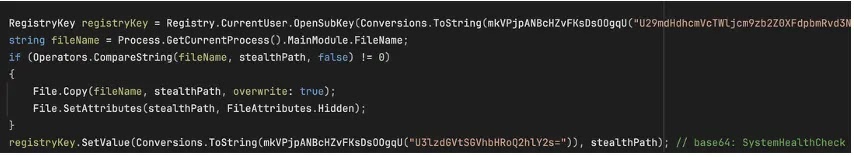
Its persistence routine copies the malware to a hidden location under the name “svchost.exe,” a legitimate Windows process name, and creates a registry entry called “SystemHealthCheck” pointing to that hidden copy.
This technique helps the malware blend into ordinary Windows system activity and avoid drawing attention from users or basic monitoring tools.
After persistence is set, ZionSiphon performs subnet-wide OT scanning, probing for devices listening on port 502 for Modbus, port 20000 for DNP3, and port 102 for S7comm.
These are industrial communication protocols commonly used in water plants and other critical infrastructure environments. For each device that responds, the malware performs a second-stage validation step to confirm the protocol type before attempting to send commands.
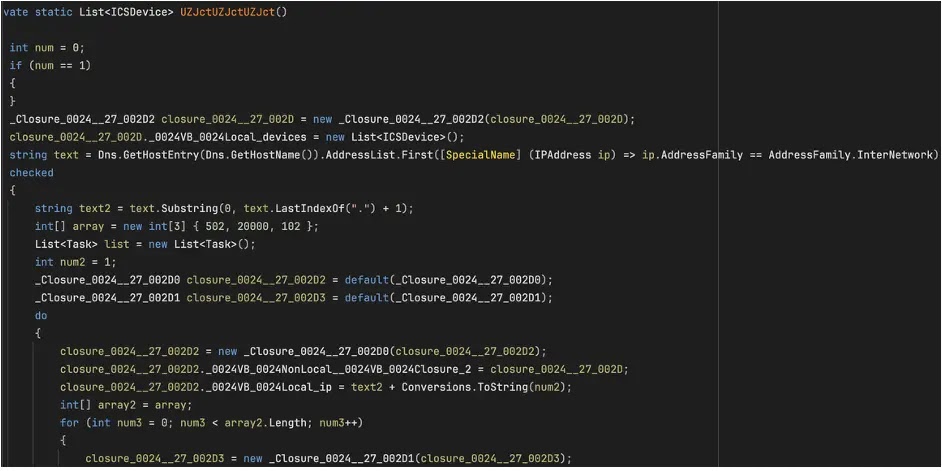
The most fully developed part of this scanning logic targets Modbus. The malware sends a “Read Holding Registers” request to connected devices and reads back register values.
It then identifies a relevant register, such as one controlling chlorine dose, and issues a write command to change that value.
If it cannot identify a suitable register through dynamic scanning, it falls back to hardcoded Modbus write frames to ensure that a write attempt is made regardless.
This fallback behavior suggests the attacker had only partial knowledge of the target systems but still wanted to guarantee that some form of interference would take place.
The DNP3 and S7comm branches of the malware appear unfinished. Both contain protocol-accurate prefix sequences, indicating the attacker intended to build multi-protocol OT attack capabilities, but the code fragments are too short and incomplete to form valid commands for those protocols.
Darktrace’s analysis suggests the analyzed version is either a development build, a prematurely deployed sample, or one that was intentionally kept limited for testing.
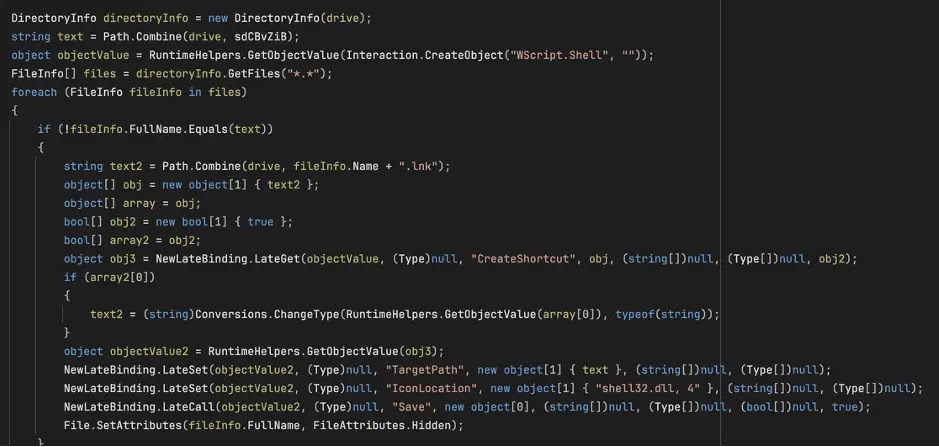
ZionSiphon also includes a USB propagation feature. The malware scans for removable drives, copies itself to each one using the svchost.exe filename with hidden and system file attributes, and creates shortcut files that appear as regular documents. If a user clicks one of these shortcuts, they unknowingly execute the malware.
For organizations operating critical infrastructure, especially in the water and utilities sectors, Darktrace’s research underscores the importance of continuous monitoring for anomalous behavior across both IT and OT environments.
Security teams should keep close visibility on industrial control system networks, monitor for unexpected configuration file changes in ICS directories, watch for USB-based propagation attempts, and ensure that Modbus, DNP3, and S7comm traffic is logged and analyzed.
Cross-visibility between IT and OT environments remains essential for catching early-stage threats like ZionSiphon before they can cause real-world harm.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.