Critical Microsoft Exchange Server Flaw Actively Exploited
Microsoft issued an urgent security alert regarding a newly discovered vulnerability in Exchange Server that is currently being exploited in the wild. Tracked as CVE-2026-42897, this critical...
Microsoft issued an urgent security alert regarding a newly discovered vulnerability in Exchange Server that is currently being exploited in the wild.
Tracked as CVE-2026-42897, this critical spoofing flaw carries a high CVSS 3.1 severity score of 8.1 and directly impacts on-premises email infrastructure.
Threat actors are actively exploiting this network-based weakness to compromise organizational systems before a permanent patch is finalized.
Cybersecurity analysts have confirmed that the vulnerability specifically targets the Microsoft Exchange Outlook Web Access service.
Because the flaw is already being utilized in active campaigns, system administrators are urged to apply temporary defensive measures immediately.
The security risk is entirely focused on on-premises deployments, meaning organizations using cloud-based Microsoft Exchange Online remain completely unaffected by this threat vector.
Microsoft Exchange Server Flaw Exploited
The technical foundation of this cyberattack relies on improper input neutralization during web page generation, which is commonly classified as a cross-site scripting weakness.
An unauthorized attacker can exploit this issue by sending a specially crafted email directly to a targeted user.
If the recipient opens the malicious message in Outlook Web Access and meets certain interaction conditions, the payload allows arbitrary JavaScript to execute seamlessly in the user’s browser.
Security researchers note that this execution path effectively enables network-level spoofing without requiring prior administrative privileges.
The vulnerability impacts several major iterations of the platform, specifically affecting Exchange Server 2016, Exchange Server 2019, and the Exchange Server Subscription Edition across all update levels.
The low attack complexity combined with a network-based execution model makes this a highly effective tool for threat actors attempting to hijack user sessions or manipulate local browser data.
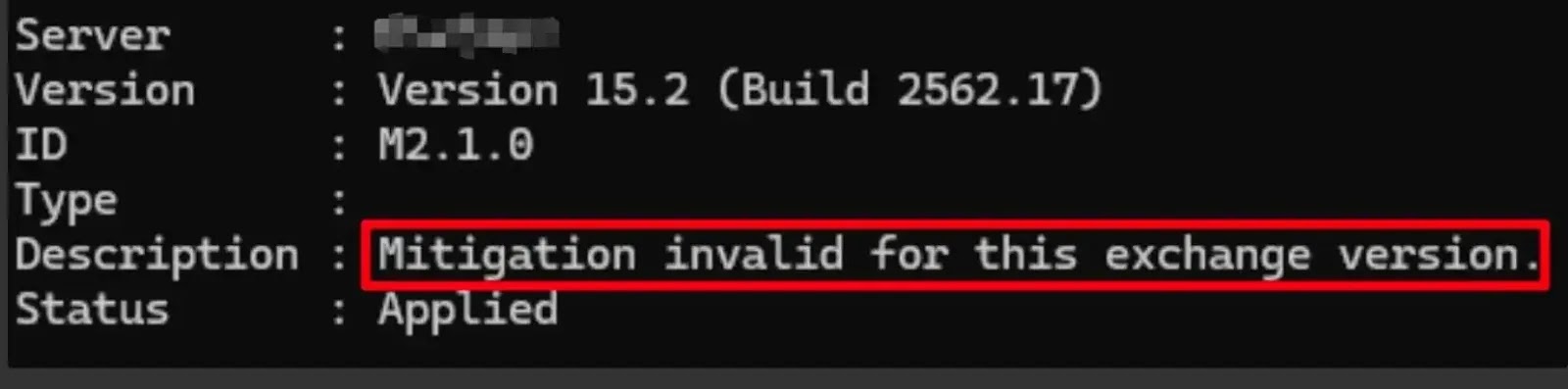
While a permanent security update is currently undergoing development and testing, Microsoft has deployed a temporary safeguard through the automated Exchange Emergency Mitigation Service.
For organizations with this default service enabled, the specific mitigation identified as M2.1.x is automatically applied to protect vulnerable environments.
Administrators operating in disconnected or air-gapped networks must manually download and execute the latest Exchange on-premises Mitigation Tool script via an elevated management shell to achieve this necessary protection.
Implementing this emergency mitigation introduces minor operational side effects that IT teams must manage.
Microsoft documentation indicates that the Outlook Web Access Print Calendar functionality may stop working properly, requiring users to rely on the desktop client or take manual screenshots.
Furthermore, inline images might not display correctly within the reading pane, prompting workarounds such as sending images as direct attachments.
Despite these cosmetic and functional disruptions, the security community strongly advises organizations to keep the mitigation active.
Microsoft software engineers are actively finalizing a permanent official fix that meets their quality assurance standards.
Once released, the security update will be made publicly available for the Exchange Server Subscription Edition.
However, permanent updates for older versions, such as Exchange 2016 and 2019, will be provided only to customers who are actively enrolled in the Period 2 Exchange Server Extended Security Update program.
Organizations relying on older cumulative updates are strongly encouraged to upgrade their infrastructure immediately to ensure compatibility with the final patch when it is deployed.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.