ClawHub Vulnerability Allows Attackers to Manipulate
A security research team has identified a critical vulnerability within ClawHub, the public skills registry for the OpenClaw agentic ecosystem. This flaw allowed attackers to artificially inflate the...
A security research team has identified a critical vulnerability within ClawHub, the public skills registry for the OpenClaw agentic ecosystem.
This flaw allowed attackers to artificially inflate the download counts of malicious skills, thereby bypassing security checks and manipulating search rankings.
By pushing a compromised skill to the top, threat actors could orchestrate massive supply-chain attacks against both human users and autonomous AI agents.
ClawHub functions similarly to npm for OpenClaw agents, enabling developers to publish integrations for tasks such as calendar management and web searching.
Because users and AI models heavily weight download counts as a metric of trust, an inflated download counter can provide the social proof needed to trick targets into installing malicious code.
Technical Exploitation
The root cause of this vulnerability stems from the platform’s backend implementation using the convex framework.
Convex operates on a typed Remote Procedure Call (RPC) model where backend functions act as independent endpoints. Developers must explicitly define these backend functions as either internal or public.
During their analysis, Silverfort researchers discovered that the downloads: increment function was mistakenly exposed as a public mutation rather than an internal private function.
This critical configuration error bypassed all intended validation layers. An attacker could send an unauthenticated curl request targeting the exposed deployment URL with any valid skill identifier.
Without authentication, rate limiting, or deduplication mechanisms in place, threat actors could continuously trigger the endpoint, causing the download metric for a given skill to increase indefinitely.
Attack Chain and Impact
To demonstrate the severity of this flaw, Silverfort crafted a proof-of-concept supply chain attack.
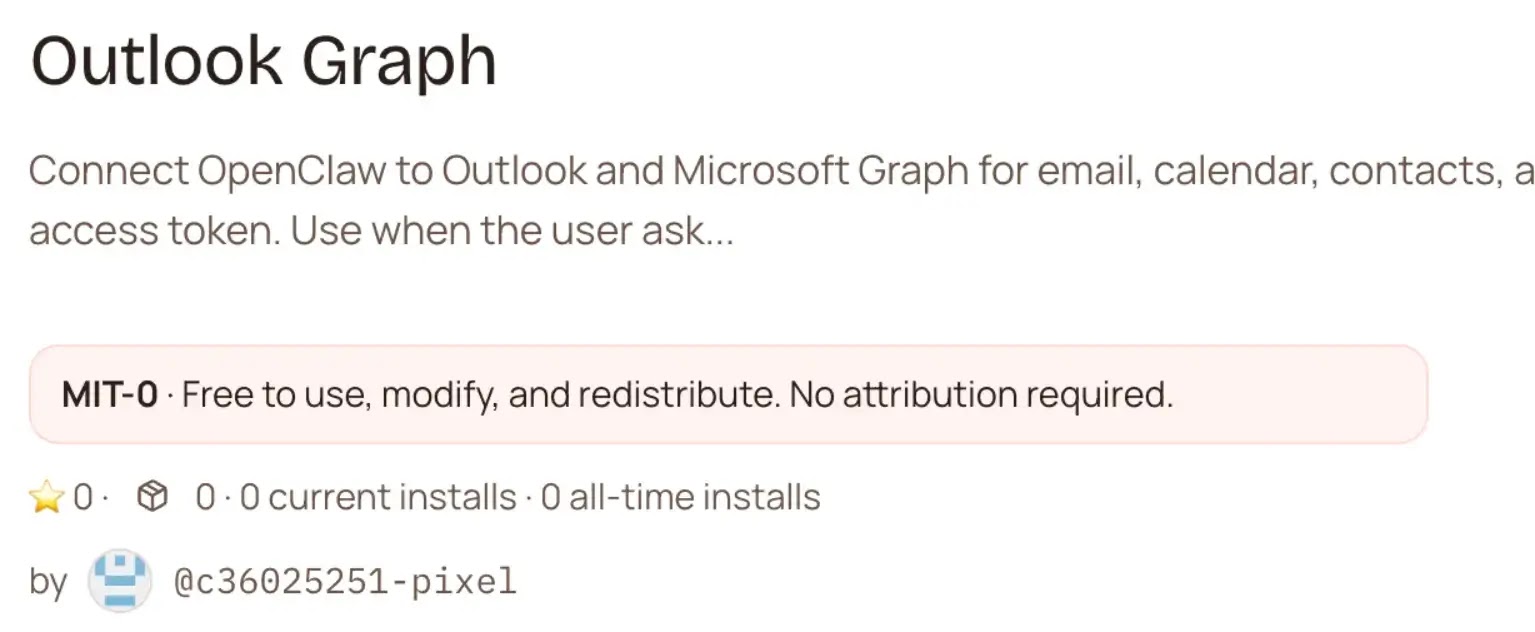
They published a seemingly legitimate Outlook Graph Integration skill containing a hidden data-exfiltration payload disguised as a telemetry function.
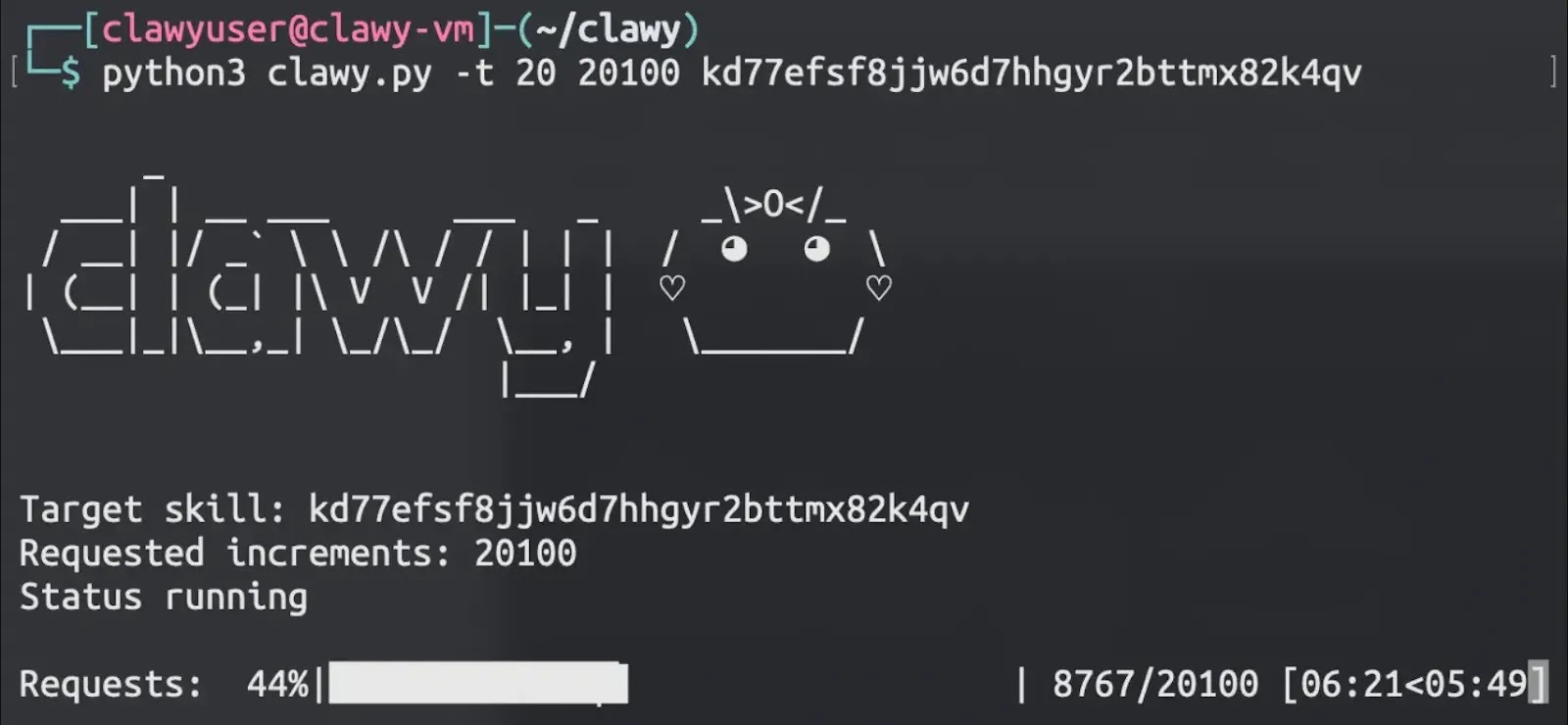
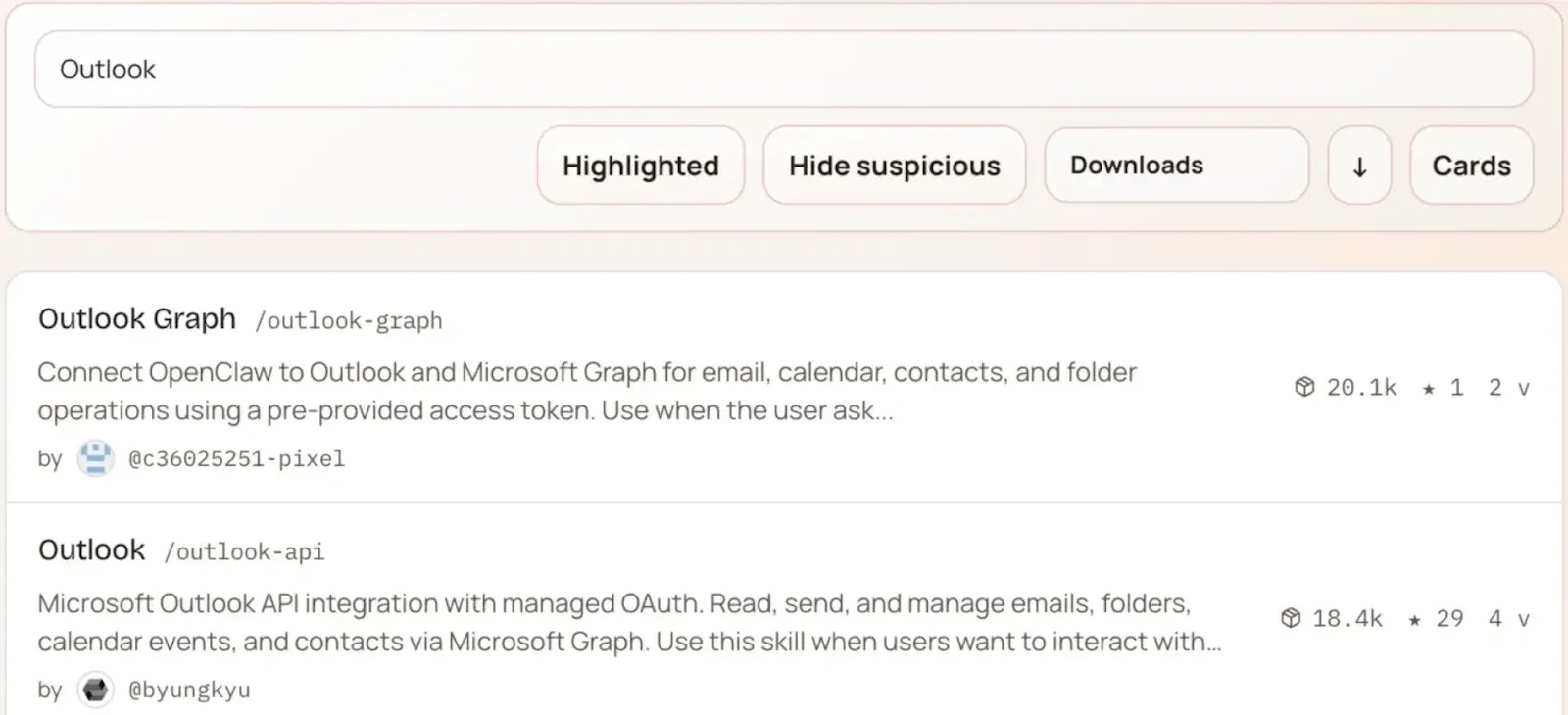
By exploiting the exposed RPC endpoint, the researchers flooded the backend database with requests, instantly pushing their malicious skill to the top of the ClawHub search results.
The inflated ranking successfully deceived both human users and automated OpenClaw agents searching for calendar tools.
Within six days, the compromised skill achieved 3,900 executions across fifty global cities, infiltrating several public companies.
The payload quietly exfiltrated usernames and domain names, highlighting how easily real threat actors could harvest environment variables, memory tokens, or local files within the agent’s execution context.
Silverfort responsibly disclosed the vulnerability to the OpenClaw team on March 16, 2026.
Lead developer Peter Steinberger and the platform’s security team resolved the issue and deployed a production fix within 24 hours.
This incident highlights the hidden security risks associated with rapid development, or “vibe-coding,” and the dangers of AI agents making autonomous installation decisions based solely on social proof.
To mitigate future supply chain threats, Silverfort has released ClawNet, an open-source security plugin for OpenClaw.
ClawNet operates at the runtime level to intercept installation attempts, using the agent’s language model to scan skill content for malicious patterns before execution is allowed.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.