Malicious npm Packages Steal Crypto Wallet Keys via
The cryptocurrency development community now faces a serious supply chain threat. Five malicious npm packages have been discovered, engineered to steal private wallet keys and transmit them directly...
The cryptocurrency development community now faces a serious supply chain threat. Five malicious npm packages have been discovered, engineered to steal private wallet keys and transmit them directly to a Telegram bot.
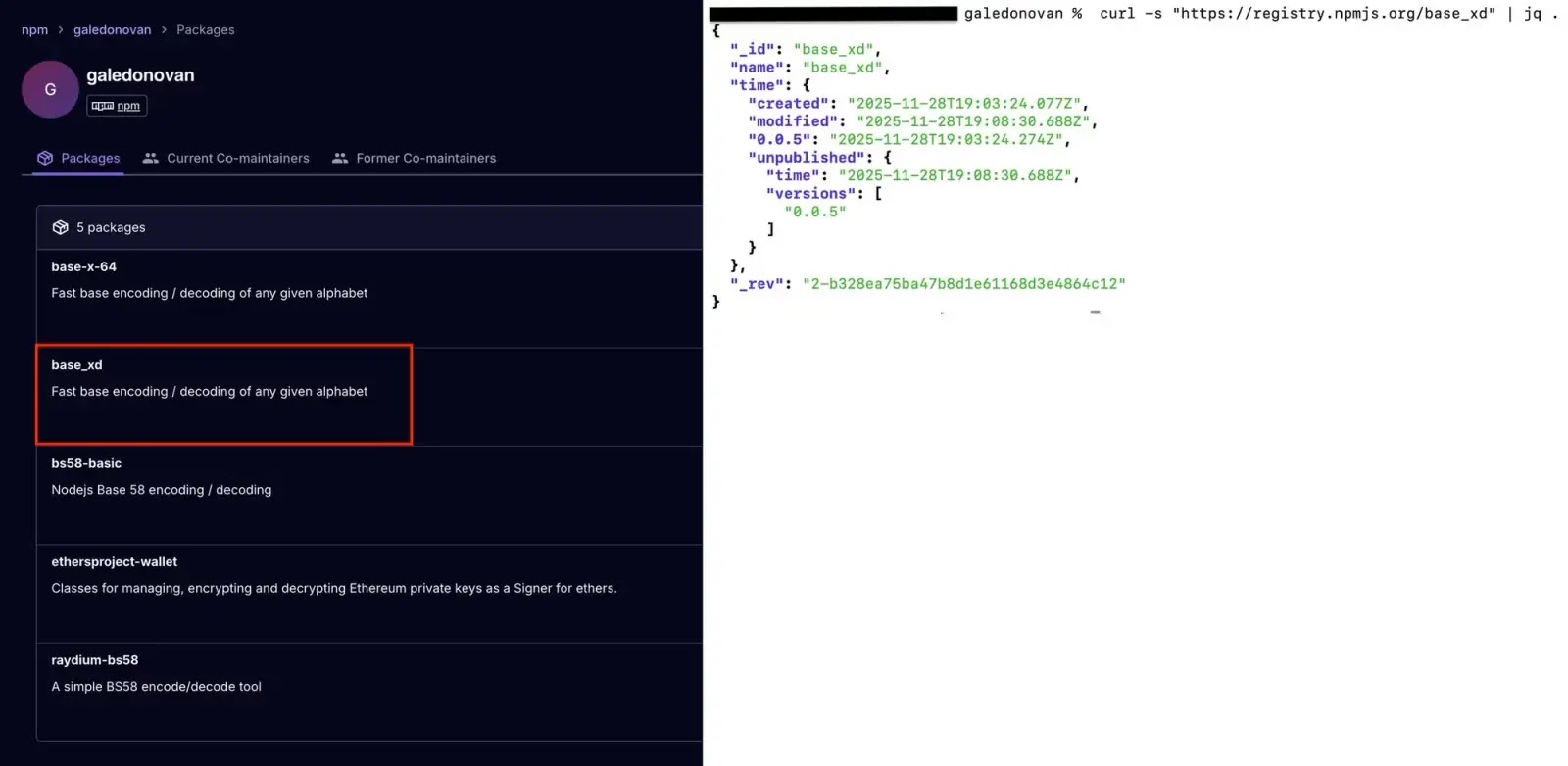
Published under the npm account “galedonovan,” these packages were crafted to look like trusted libraries that Solana and Ethereum developers rely on every day.
Once installed, they work silently in the background, capturing key material and sending it to an attacker without triggering any visible errors.
The attack targets both major blockchain ecosystems at once. Four packages — raydium-bs58, base-x-64, bs58-basic, and base_xd — go after Solana developers by intercepting Base58 decode() calls, the standard way to load a keypair from a private key string.
The fifth package, ethersproject-wallet, hooks directly into the Ethereum Wallet constructor the moment a private key is passed in.
In both cases, the key travels as plain text to a Telegram group before the legitimate function finishes, giving the attacker immediate access to drain any connected wallet.
Socket.dev researchers identified all five packages as part of a coordinated typosquatting campaign, noting that each one was tied to the same npm account and used the same hardcoded Telegram bot endpoint for exfiltration.
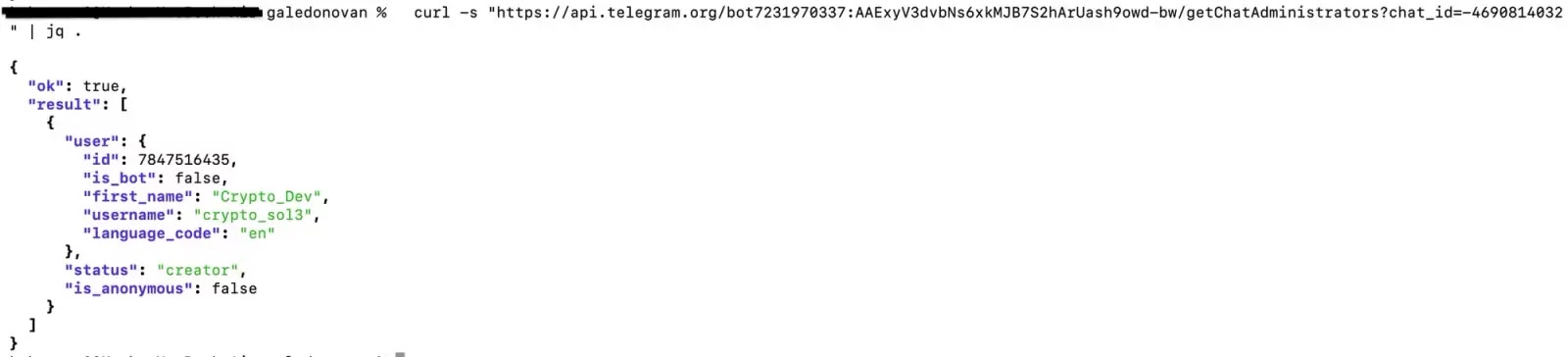
The C2 infrastructure led to a single Telegram bot, @Test20131_Bot, with a receiving group run by @crypto_sol3 (display name: Crypto_Dev, user ID: 7847516435).
Since the bot token and chat ID were hardcoded into every package, there was no external staging server or domain needed — the theft worked as long as the Telegram bot stayed online.
One package, base_xd, was pulled from npm just five minutes after it was published, but the other four remained live at the time of discovery.
Socket’s AI scanner caught base-x-64 by spotting the obfuscated exfiltration channel inside src/cjs/index.cjs and flagging that data passed to decode() was being sent to a Telegram bot
Takedown requests for all five packages and the threat actor’s account have been submitted to the npm security team.
The threat is especially hard to detect because the malicious packages behave exactly like the real ones.
A developer who installs raydium-bs58 would get back the correct output, see no errors, and have no reason to suspect anything — even as their private key is sent to a stranger’s Telegram group.
How the Key Theft Works
Each package in this campaign relies on a technique known as function hooking. The attacker wraps a function that developers regularly pass private keys through, intercepts the key the moment it arrives, sends it to a Telegram bot, and then passes control back to the original function so everything appears to work normally.
In raydium-bs58, the modified decode() function calls sendMessage() with the key before running the actual decode, so the key is sent out even if the decode itself fails.
In base-x-64, the payload hides behind an array rotation cipher that scrambles the Telegram URL, bot token, and chat ID, making it harder to spot during a code review.
The package bs58-basic carries no malicious code of its own — it simply lists base-x-64 as its only runtime dependency, so the theft happens through a transitive chain without any obvious red flags.
The ethersproject-wallet package clones the legitimate @ethersproject/wallet 5.8.0 release nearly perfectly, with just a single injected line inserted after the TypeScript build step, confirmed by a mismatch between the source map and compiled output.
Any developer who installed these packages should treat every private key that passed through them as fully compromised. Funds should be moved and keys rotated without delay.
The legitimate replacements are bs58, base-x, and the scoped @ethersproject/wallet from the official ethers.js monorepo. Transitive dependencies must be audited, since bs58-basic silently pulls in base-x-64.
Going forward, any npm package that re-exports a cryptographic utility with a thin wrapper, or contains obfuscated code near key-handling logic, should be treated as suspicious until proven otherwise.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.