BreachForums Hacked: Dark Web User Records Hackers Expose
A mysterious hacker, operating under the alias ‘James,’ has leaked the complete user database of BreachForums. This notorious Dark Web User, including admins, moderators, and regular...
A mysterious hacker, operating under the alias ‘James,’ has leaked the complete user database of BreachForums. This notorious Dark Web User, including admins, moderators, and regular members, potentially dooming many to law enforcement scrutiny.
This incident underscores the irony of cybercriminals falling victim to their own vulnerabilities.paste.txt
BreachForums Data Breach
BreachForums emerged in 2022 as the successor to RaidForums, which U.S. authorities seized amid investigations into data trafficking.
The forum, powered by MyBB software, facilitated sales of breached datasets, hacking tools, and illicit services, often hosted via DDoS-Guard and Tor mirrors despite repeated takedowns.
Key disruptions included the 2023 arrest of founder Conor Fitzpatrick, who received a 20-year supervised release sentence, and a 2024 domain seizure swiftly reclaimed by operators ShinyHunters.
ShinyHunters, linked to groups like Scattered LAPSUS Hunters, relaunched the site multiple times, surviving French arrests in June 2025 and FBI seizures of extortion portals. The forum’s resilience relied on frequent domain switches and Dark Web presence, but underlying MyBB flaws proved fatal.
The dumped MySQL database, from table “hcclmafd2jnkwmfufmybbusers,” reveals usernames, hashed passwords (Argon2), emails, IP addresses, registration dates, and PGP keys for high-profile accounts like ShinyHunters, Hollow, and IntelBroker.
Analysis shows admins (4), super moderators (3), and mods (6), with user origins spanning the U.S. (largest share), Germany, Netherlands, France, Turkey, UK, and MENA regions like Morocco and Egypt.
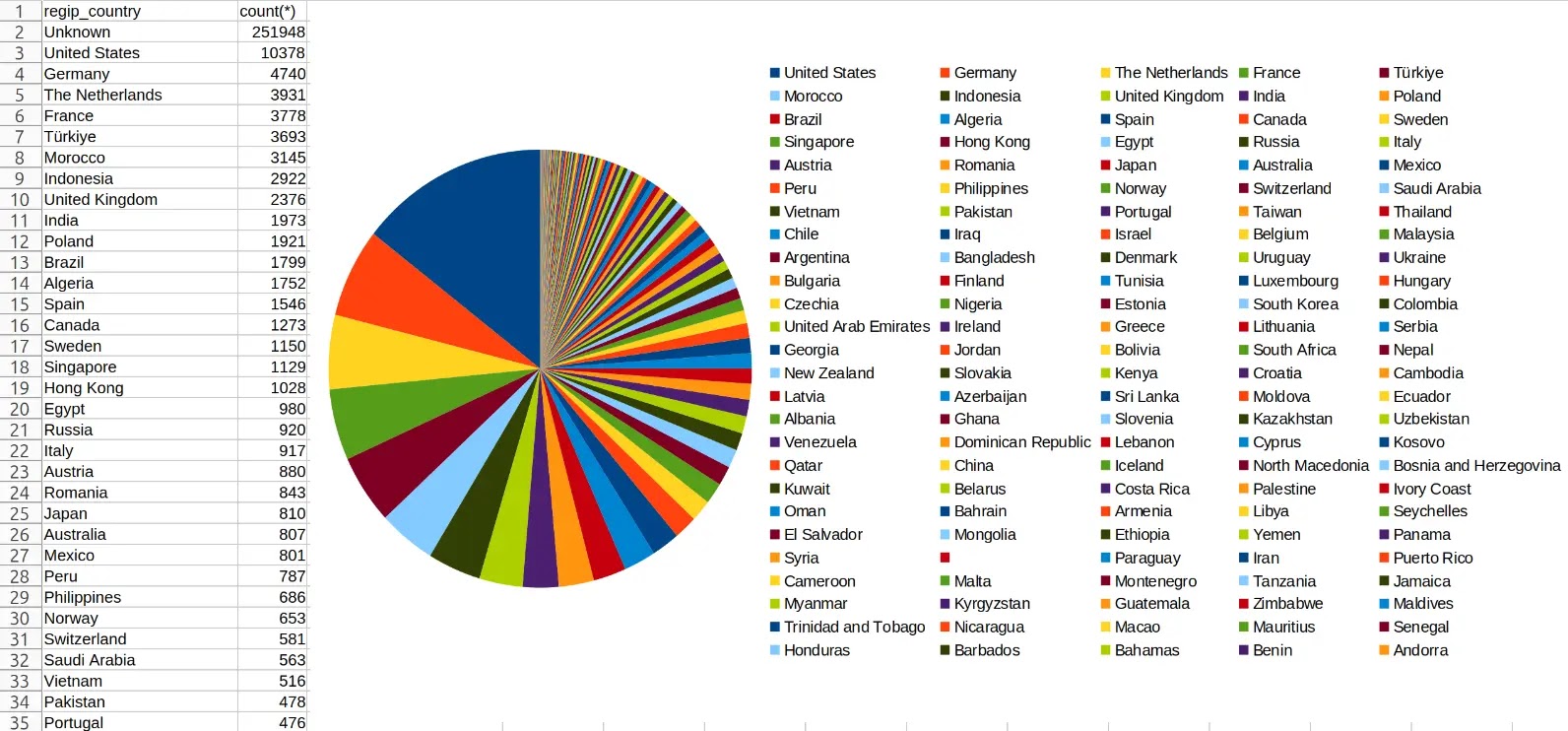
Screenshots from attached images depict the shinyhunte.rs page with “DOOMSDAY: The Story of James” manifesto and a pie chart visualizing user countries, highlighting U.S. dominance. James claims the breach stemmed from a web app vulnerability or misconfiguration, turning the criminals’ haven into a liability.
Under the banner “Doomsday,” James portrays himself as a “predator” transcending generations, boasting infiltrations of Google, Microsoft, the FBI, the NSA, and more.
He names alleged operators like Dorian Dali (Kams), Nahyl Ojeda (INDRA), Ali Aboussi (Kernel), and founders Prosox/Kuroish, vowing their downfall for betraying a higher purpose. Addressing French readers, James positions himself as a protector against these “children” he once mentored, linking to anti-France activities.
The text blends hacker lore with philosophical rants on power, evil, and redemption, echoing past underground manifestos.
This self-inflicted wound exposes plaintext risks even on Dark Web sites, amplifying arrest threats amid global crackdowns. Victims face doxxing, while law enforcement gains leads on ShinyHunters derivatives within “The Com” network. Resecurity, sharing the dump for analysis, warns of broader disruptions to extortion rackets targeting firms like Salesforce.
As James declares “no place to hide,” the BreachForums saga illustrates cybercrime’s fragility, predators devoured by a greater one.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.