MacSync Stealer Evades Gatekeeper with Signed macOS App
A new variant of the MacSync malware, specifically targeting macOS users, has been uncovered by cybersecurity researchers. Unlike previous versions that relied on complex ClickFix techniques, this...
A new variant of the MacSync malware, specifically targeting macOS users, has been uncovered by cybersecurity researchers.
Unlike previous versions that relied on complex ClickFix techniques, this iteration masquerades as a legitimately signed, notarised Apple application, thereby bypassing macOS Gatekeeper security and stealing sensitive data.
Code-Signed Malware Bypasses Security
Jamf Threat Labs recently identified this evolved Stealer Evades Gatekeeperincludes two significant technical changes.
The malware now presents itself as a code-Signed macOS App from a verified developer.
Cybercriminals obtain legitimate developer certificates through theft, the purchase of compromised developer accounts, or the establishment of fake developer companies using fraudulent identities.
By leveraging these certificates, MacSync avoids triggering macOS security warnings about “unidentified developers” that would usually alert users to potential threats.
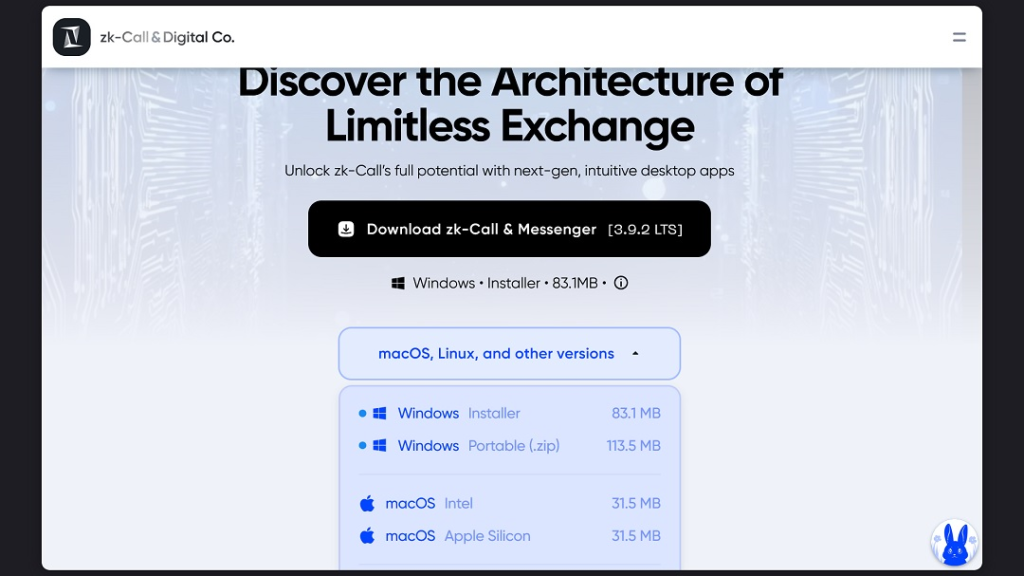
The new variant impersonates online messaging platforms, particularly targeting users interested in applications like zk-Call, an Estonia-based call and messenger service.
This social engineering tactic increases the likelihood that victims will install the malicious software without suspicion.
This MacSync version represents a significant departure from its predecessors. Earlier variants were lightweight, running modular payloads directly in memory without a substantial disk footprint.
However, Jamf researchers noted this version features a huge disk image of 25.5MB, suggesting enhanced functionality and embedded components.
MacSync poses serious threats to infected systems. The malware can install backdoors for remote system control, steal stored data and browser information, target cryptocurrency wallet credentials, and maintain persistent hidden access.
Jamf identified focusgroovy[.]com as a command-and-control server used to fetch additional payloads, with web browsers now flagging the site for suspected phishing activity, as reported by Moonlock.
While the exact distribution method remains unclear, potential infection vectors include malicious advertising campaigns, social media exploitation, search engine manipulation, and targeted spear-phishing attacks.
Mac users should remain vigilant and avoid downloading applications from untrusted sources, even if they appear legitimately signed.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.