BlobPhish Attack Steals Login Credentials via Browser Blo
Since October 2024, a sophisticated, memory-resident phishing campaign named BlobPhish has been actively stealing credentials. It exploits browser Blob URL APIs to silently target Microsoft 365...
Since October 2024, a sophisticated, memory-resident phishing campaign named BlobPhish has been actively stealing credentials. It exploits browser Blob URL APIs to silently target Microsoft 365 users, major U.S. banks, and financial platforms. A key concern is BlobPhish’s ability to remain almost completely invisible to traditional security tools.
Table Of Content
BlobPhish is a sustained credential-phishing operation that fundamentally changes how phishing pages are delivered to victims.
Rather than hosting fake login pages on attacker-controlled servers and serving them over standard HTTP, BlobPhish generates phishing pages entirely inside the victim’s browser using JavaScript Blob objects.
The result is a phishing payload that exists only in memory, leaving no file on disk, no cache artifact, and no suspicious HTTP request in proxy logs for security tools to flag.
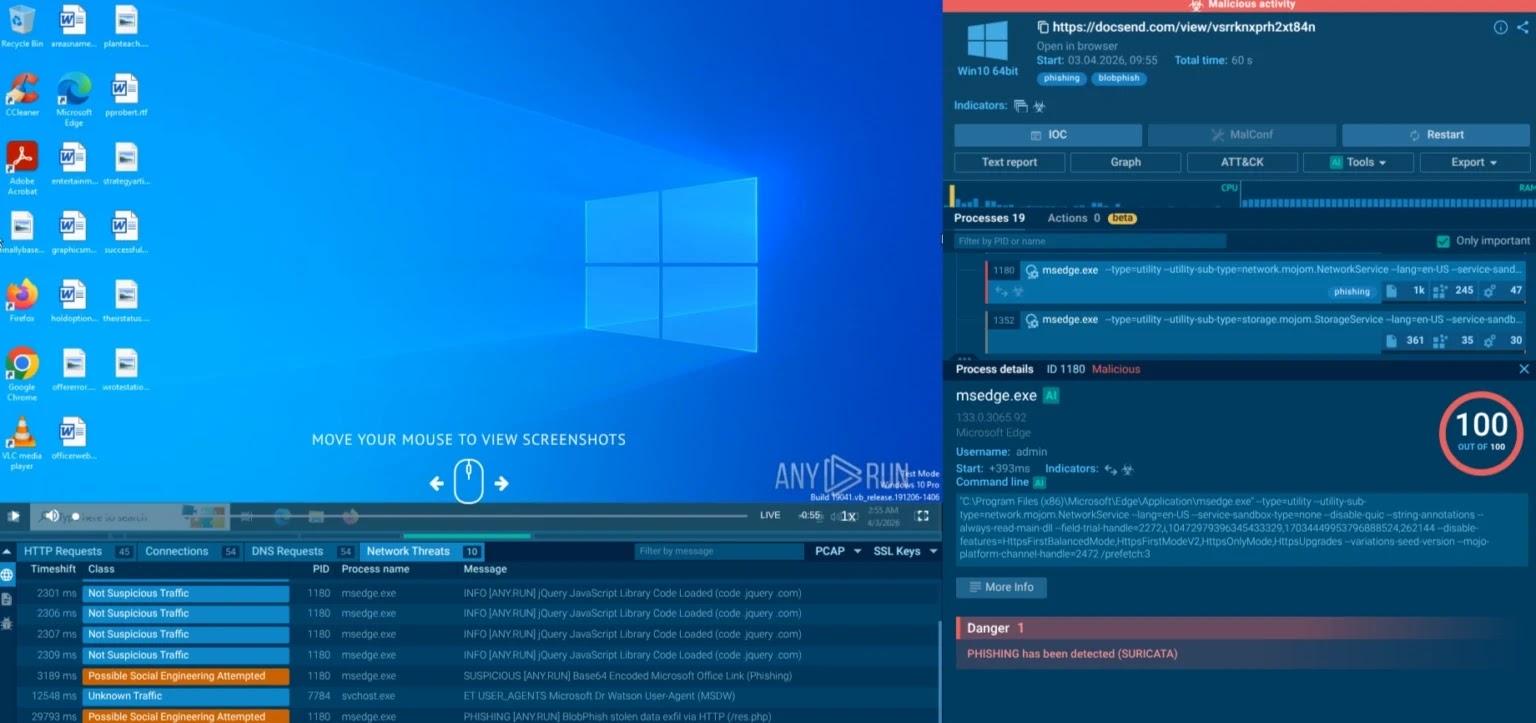
First observed in October 2024, the campaign has run uninterrupted for over 18 months and recorded a significant spike in activity in February 2026, confirming it as a mature, well-maintained threat operation rather than a short-lived opportunistic attack.
BlobPhish kill chain
The BlobPhish kill chain is elegantly designed to defeat both network-based and file-based defenses:
- Initial Access: The victim receives a phishing email — often mimicking a financial alert, invoice, or document share — containing a link to a trusted-looking service such as DocSend or a shortened URL via t.co. PDF attachments carrying QR codes that lead to malicious JavaScript pages have also been observed, particularly in energy-sector campaigns.
- Loader Execution: Clicking the link redirects the victim to an attacker-controlled HTML page hosting a JavaScript loader. Using jQuery, the loader invisibly creates a hidden
<a>anchor element, Base64-decodes a bundled phishing payload usingatob(), constructs aBlobobject of typetext/html, generates ablob:https://URL viawindow.URL.createObjectURL(), and forces the browser to navigate to it — all without any visible user interaction.
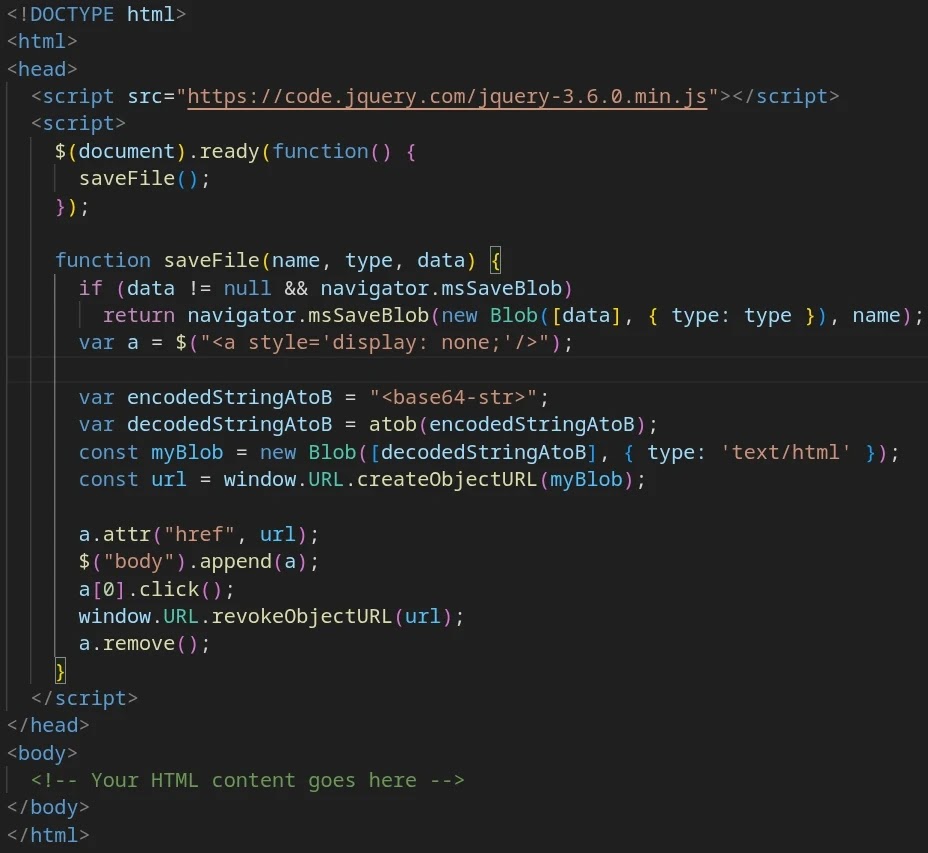
- Evidence Destruction: Immediately after navigation, the loader calls
window.URL.revokeObjectURL()and removes the anchor element from the DOM, destroying any remaining in-memory trace of the loader’s operation.
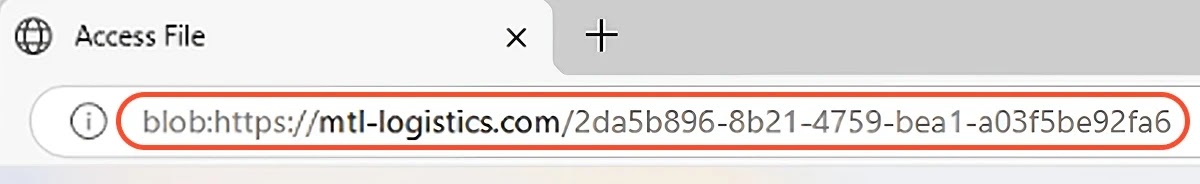
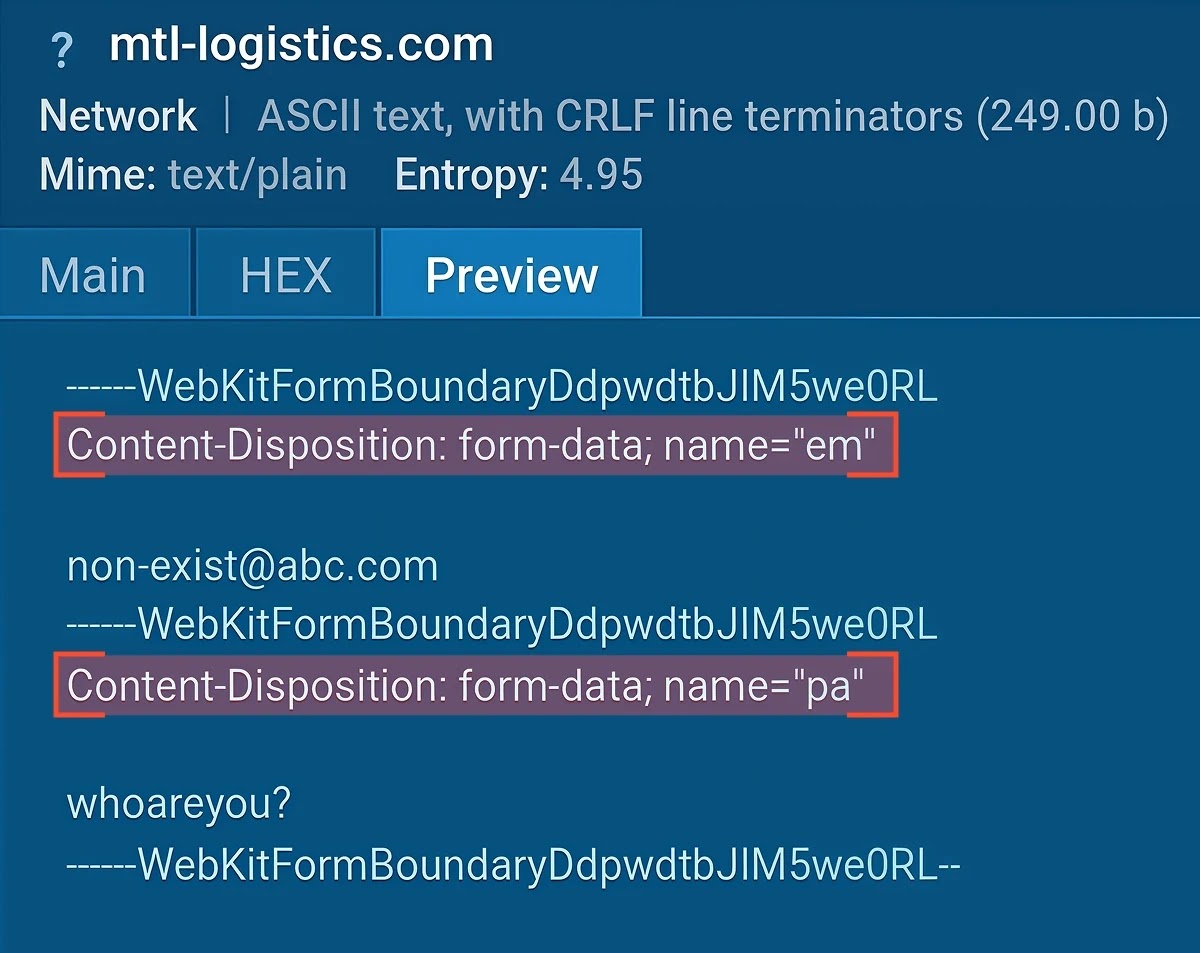
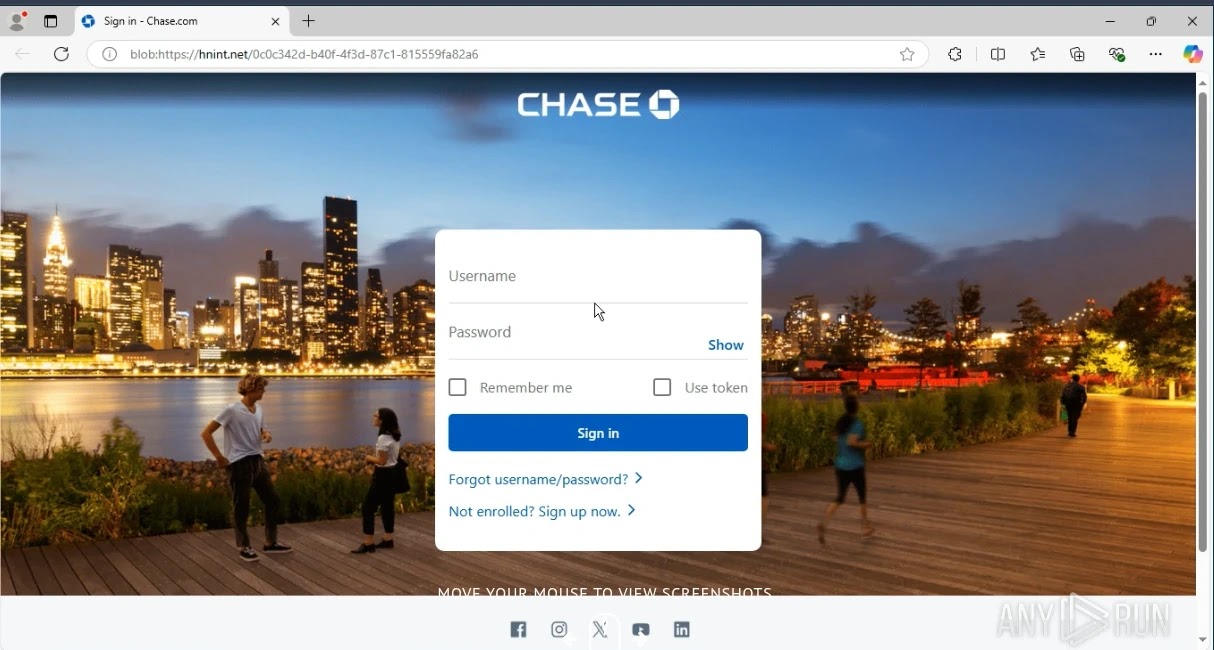
- Credential Harvest: The victim is presented with a convincing replica of a Microsoft 365, Chase, Capital One, or other financial service login page. The browser address bar shows a
blob:https://URL, which can appear legitimate to an untrained eye. A failed-login counter forces victims to re-enter credentials multiple times, maximizing harvest accuracy. Captured data is exfiltrated via HTTP POST to attacker-controlled endpoints matching the pattern*/res.php,*/tele.php, or*/panel.php— hosted predominantly on compromised legitimate WordPress sites.
BlobPhish Evades Conventional Defenses
BlobPhish impersonates a broad list of high-value platforms, including Microsoft 365, OneDrive, SharePoint, Chase, Capital One, FDIC, E*TRADE, Charles Schwab, Morgan Stanley/Merrill Lynch, American Express, PayPal, and Intuit.
Although financial and cloud-productivity lures dominate, victim organizations span Finance, Manufacturing, Education, Government, Transport, and Telecommunications sectors.
Geographically, approximately one-third of observed victims are U.S.-based, with additional activity recorded across Germany, Poland, Spain, Switzerland, the UK, Australia, South Korea, Saudi Arabia, Qatar, Jordan, India, and Pakistan.
The blob:https:// scheme is the campaign’s core evasion innovation. Because the phishing page is never transmitted over the network as a standalone HTTP response:
- URL reputation engines cannot block it — no external URL to scan.
- Proxy logs show no suspicious requests for the phishing page itself.
- Secure Email Gateways (SEGs) miss the payload, which materializes only after delivery.
- File-based endpoint solutions find nothing — no file is ever written to disk.
- Cache forensics return empty — the Blob URL is revoked before investigators can inspect it.
A single successful BlobPhish compromise can cascade into Business Email Compromise (BEC) fraud, full Microsoft 365 tenant takeover, unauthorized wire transfers, investment account manipulation, and ransomware deployment following lateral movement.
Regulatory consequences, including GDPR 72-hour breach notification, SEC cybersecurity incident disclosure, and FFIEC authentication guidance, add material legal exposure on top of operational damage.
Key Indicators of Compromise (IOCs)
| IOC Type | Example |
|---|---|
| Loader URL | hxxps[://]mtl-logistics[.]com/blb/blob[.]html |
| Exfiltration endpoint | hxxps[://]mtl-logistics[.]com/css/sharethepoint/point/res[.]php |
| Capital One exfil | hxxps[://]wajah4dslot[.]com/wp-includes/certificates/tmp//res[.]php |
| Chase Banking exfil | hxxps[://]hnint[.]net/cgi-bin/peacemind//res[.]php |
| E*TRADE exfil | hxxps[://]ftpbd[.]net/wp-content/plugins/cgi-/trade/trade//res[.]php |
| tele.php variant | hxxps[://]_wildcard_[.]gonzalezlawnandlandscaping[.]com/…/tele[.]php |
Additional compromised domains include larva888[.]com, riobeautybrazil[.]com, i-seotools[.]com, and mts-egy[.]net.
Defensive Recommendations
Security teams should take the following priority actions:
- Deploy sandbox analysis capable of executing JavaScript in real browsers to detonate blob-based payloads safely before they reach end users
- Hunt proactively using the
BlobPhishLoaderHTMLYARA rule and URL pivot queries (url:"/res.php$",url:"*/blob.html$") in threat intelligence platforms - Enforce phishing-resistant MFA (FIDO2/hardware keys) on all Microsoft 365 and banking portals to limit post-compromise blast radius
- Integrate live TI feeds that push BlobPhish IOCs into firewalls, proxies, and SIEM rules automatically as attacker infrastructure rotates
- Train employees to recognize unexpected
blob:https://URLs in browser address bars as a red flag
BlobPhish demonstrates that the phishing threat has outpaced perimeter and static-signature defenses.
Effective protection now demands dynamic behavioral analysis, continuous threat hunting, and automated intelligence propagation operating at the speed of attacker infrastructure rotation.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.