Gentlemen RaaS Exploits Fortinet & Leverages Cisco
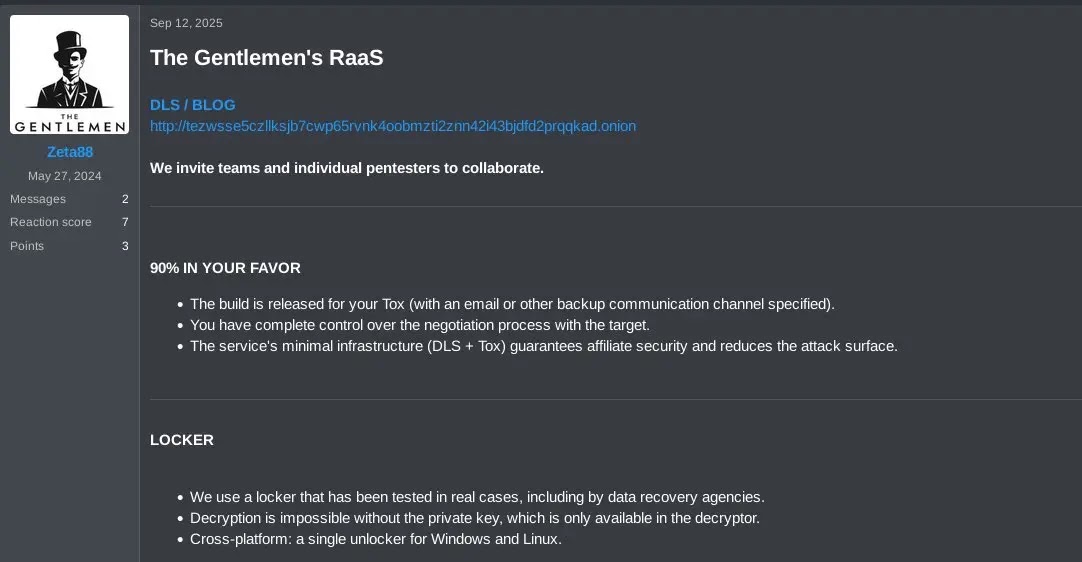
The Gentlemen, a ransomware-as-a-service (RaaS) operation that emerged in mid-2025, has rapidly established itself as a highly active threat. In just the first five months of 2026, the group claimed...
The Gentlemen, a ransomware-as-a-service (RaaS) operation that emerged in mid-2025, has rapidly established itself as a highly active threat. In just the first five months of 2026, the group claimed approximately 332 published victims, quickly becoming one of the world’s most prolific ransomware programs. Its methods, including leveraging Fortinet and Cisco edge devices for initial access, are detailed in
Analysts from Check Point Research have been closely tracking The Gentlemen and recently obtained a rare look inside the group’s inner workings after an internal database leak surfaced on underground forums.
On May 4, 2026, the group’s administrator publicly acknowledged that their backend system, known internally as “Rocket,” had been compromised and that sensitive operational data had been exposed.
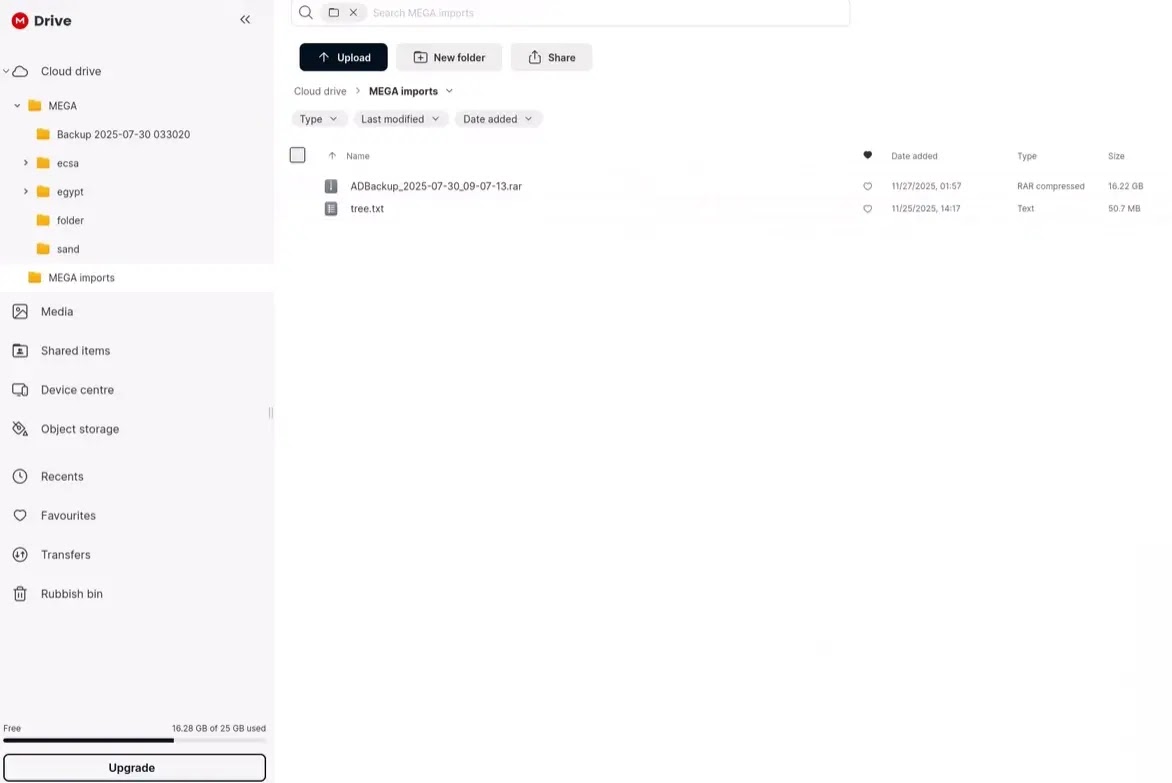
The leaked material included internal chat logs from channels named INFO, general, TOOLS, and PODBOR. These conversations gave researchers an end-to-end view of how the group runs its campaigns, from initial access and reconnaissance all the way through ransom negotiations and payouts.
Targeting Fortinet and Cisco Edge Devices
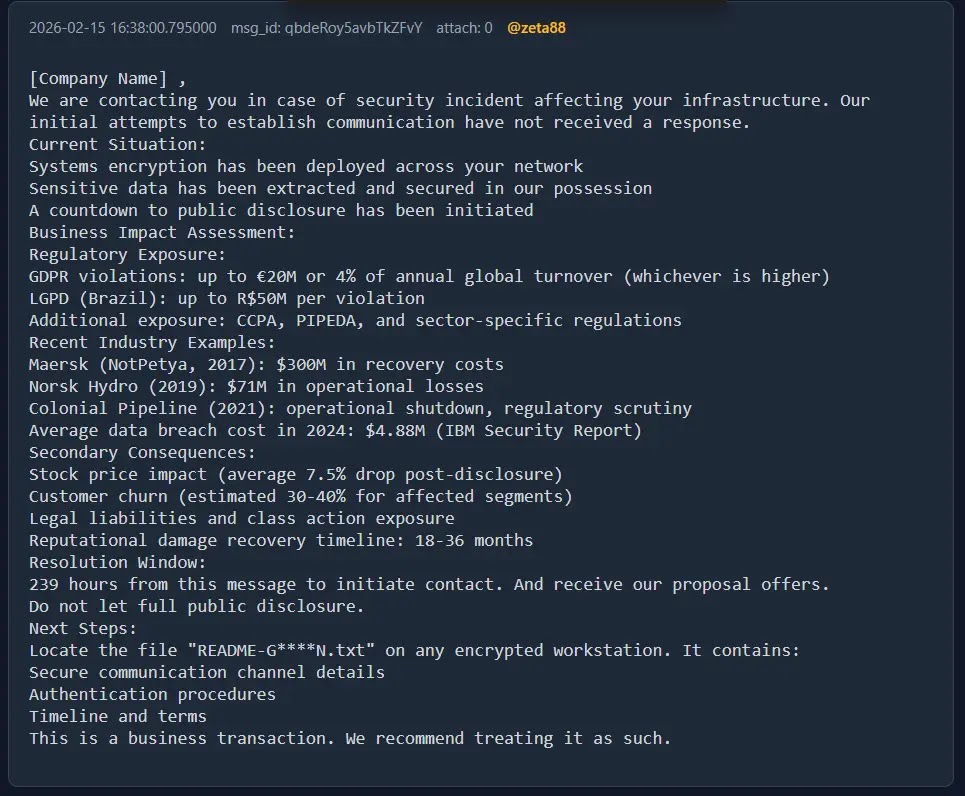
In one documented case, the group negotiated a final ransom payment of 190,000 USD after starting with an initial demand of 250,000 USD.
What makes The Gentlemen particularly dangerous is how tightly organized they are despite being affiliate-based. The leak identified nine named accounts working together in a coordinated way, with the administrator, known as zeta88 or hastalamuerte, personally involved in carrying out attacks alongside managing the overall program.
The group’s preferred method for breaking into a target’s network starts at the perimeter. Their main focus is on exposed edge devices such as Fortinet FortiGate VPN appliances and Cisco systems, which are commonly found at the entry points of corporate networks. Once they find a vulnerable or misconfigured device, they use it as a gateway inside.
To gain that initial foothold, the group combines several approaches. They brute-force login panels, exploit known security flaws, and purchase ready-made access from underground brokers.
Three vulnerabilities they actively track include CVE-2024-55591, affecting the FortiOS management interface, CVE-2025-32433, an Erlang SSH flaw relevant in Cisco environments, and CVE-2025-33073, tied to NTLM relay attacks.
One key operator known as qbit was specifically observed scanning for Fortinet VPNs and running NTLM relay checks using a tool called RelayKing.
After getting a foothold, the group pivots deeper into the network. They perform Active Directory reconnaissance, escalate privileges, and disable security tools using purpose-built evasion kits.
They also use cloud-based tunneling through services like Cloudflare to maintain reliable, long-term access without being detected. Only once the network is firmly in their control do they deploy their custom ransomware locker and begin encrypting systems.
A Sophisticated Double-Extortion Playbook
The Gentlemen do not stop at encryption. They exfiltrate data before deploying their locker and use it as leverage in negotiations. In a notable case from April 2026, the group breached a software consultancy in the United Kingdom, stole sensitive client data, and then reused that same data weeks later to assist an attack against a company in Turkey, where they had also gained initial access through a vulnerable VPN appliance.
In the Turkish operation, the group published the UK consultancy as the supposed “access broker” on their data leak site, creating pressure on both victims simultaneously.
This tactic, where earlier victims are weaponized against future ones, signals a notable shift in how ransomware groups think about stolen data. Ransom demand letters drafted by zeta88 also emphasized regulatory exposure and reputational damage to push victims into paying faster.
For defenders, the patterns seen in this campaign highlight clear areas that need attention. Organizations should prioritize patching internet-facing systems, particularly VPN appliances and firewalls.
Monitoring for NTLM relay activity, hardening Active Directory configurations, and ensuring that EDR solutions are tamper-resistant are all meaningful steps that can reduce exposure to groups operating with this level of sophistication.
Indicators of Compromise (IoCs):-
| Type | Indicator | Description |
|---|---|---|
| SHA-256 | 025fc0976c548fb5a880c83ea3eb21a5f23c5d53c4e51e862bb893c11adf712a |
The Gentlemen Windows Ransomware |
| SHA-256 | 1334f0189a8e6dbc48456fa4b482c5726ab7609f7fa652fcc4c1a96f2334436f |
The Gentlemen Windows Ransomware |
| SHA-256 | 1af419b36a5edefef387409e2b3248c9223f7dc49a4f7b15ea095d371c3a70b2 |
The Gentlemen Windows Ransomware |
| SHA-256 | 22b38dad7da097ea03aa28d0614164cd25fafeb1383dbc15047e34c8050f6f67 |
The Gentlemen Windows Ransomware |
| SHA-256 | 24ac3588fb8cfbff63b7fdfcbc7dec1f3c60e54e6f949dd69d68e89e0c89d966 |
The Gentlemen Windows Ransomware |
| SHA-256 | 2ed9494e9b7b68415b4eb151c922c82c0191294d0aa443dd2cb5133e6bfe3d5d |
The Gentlemen Windows Ransomware |
| SHA-256 | 3ab9575225e00a83a4ac2b534da5a710bdcf6eb72884944c437b5fbe5c5c9235 |
The Gentlemen Windows Ransomware |
| SHA-256 | 3c2182cb0bc7528829ef03f1b1745a92bcc47d917eb8870862488f21fdf1a6d6 |
The Gentlemen Windows Ransomware |
| SHA-256 | 48d9b2ce4fcd6854a3164ce395d7140014e0b58b77680623f3e4ca22d3a6e7fd |
The Gentlemen Windows Ransomware |
| SHA-256 | 4a175eed927c0a477eafb8aa35a93c191748acaa781 |
The Gentlemen Windows Ransomware |
| SHA-256 | ac7aecd8ea3c4cd868887c51b9f246d6da856311 |
The Gentlemen Windows Ransomware |
| SHA-256 | 31fcd1fabf0a67937d4bdde33625a44f7ee6a3a7baebd262c2c24937d67fdeb4 |
The Gentlemen Windows Ransomware |
| SHA-256 | 3f2c9690ab10e8bb90713af46945048db9a94a465ffcb86a3ab9e984a759d55a |
The Gentlemen Windows Ransomware |
| SHA-256 | f4e84487d1fc44683065cc9a1089d5aa4ad1c0e4e84a63860a6177b055a2f5aa |
The Gentlemen Windows Ransomware |
| SHA-256 | 61470d17ec3c69da24f1cdf0a782237055cba43115892387d25d0e5880b3b5cd |
The Gentlemen Windows Ransomware |
| SHA-256 | 30106853cbfc6ef1ad38966b30d9bd5b99df46098e546c8aa0cb69ca2777001e |
The Gentlemen Windows Ransomware |
| SHA-256 | 0f4ba0eaab0841592710e4cc5ccd6b0b526d78bbd8bfba8c87134c1b45e990e9 |
The Gentlemen Windows Ransomware |
| SHA-256 | 568f0a3899b0076f94be16d3c40fa824ac1e6c6ee892db91415e0b9fe4e7cbe4 |
The Gentlemen Windows Ransomware |
| SHA-256 | 3ec0558a7adf89423de30d22b00b985c2e4b97e75076b1994d6d1edb57f945f4 |
The Gentlemen Windows Ransomware |
| SHA-256 | 284cc0163ec998861c7496d85f6d45c08657c9727186e39f61ff4deb8afced8b |
The Gentlemen Windows Ransomware |
| SHA-256 | 1ecdc8787a134c63bde632b18293fbfc94a91749e3e454a7a19cab7aab606f83 |
The Gentlemen Windows Ransomware |
| SHA-256 | 3fa8225bc94ec9570a6666660b02cc41a63fe39ea8b0adb67958afc982cafbe1 |
The Gentlemen Windows Ransomware |
| SHA-256 | c3f114b444d7f4c91a88a3e7a86f89ab8795ac2110d1e6c46b5a18ab3fb5fd1c |
The Gentlemen Windows Ransomware |
| SHA-256 | 5c8288a41c75bf0170c10b5e829af89370a12c86dd10f8c7f7b5a6e7d9322134 |
The Gentlemen Windows Ransomware |
| SHA-256 | 4e6368c7ab4abf93e162f7567e1a7bcb8786cb8a183a73dce2e5cc00eff2493f |
The Gentlemen Windows Ransomware |
| SHA-256 | 8ced546dc51f9d5ef78c5ee56805906ec642dfa77a1c70dfe696ff713318c53f |
The Gentlemen Windows Ransomware |
| SHA-256 | b17731bd4a6585a02c085b590149b19847990b324a0be6ec368ae0b4369b6ef0 |
The Gentlemen Windows Ransomware |
| SHA-256 | da244774995c819c63cffb7fd2132379963b9c1640ccd2efaf8e7422ffd09c7f |
The Gentlemen Windows Ransomware |
| SHA-256 | 03f1a5b4e5c2cc32b05334c18d1ccb9673667f8f43108ff736be55193c77af34 |
The Gentlemen Windows Ransomware |
| SHA-256 | 6dbe905e25f6a1dee3ec1aedca8989ad2088e4f6576b12 |
The Gentlemen Windows Ransomware |
| SHA-256 | fc75ed2159e0c8274076e46a37671cfb8d677af9f586224da1713df89490a958 |
The Gentlemen Windows Ransomware |
| SHA-256 | 1eece1e1ba4b96e6c784729f0608ad2939cfb67bc4236dfababbe1d09268960c |
The Gentlemen Linux Ransomware |
| SHA-256 | 5dc607c8990841139768884b1b43e1403496d5a458788a1937be139594f01dca |
The Gentlemen Linux Ransomware |
| SHA-256 | 788ba200f776a188c248d6c2029f00b5d34be45d4444f7cb89ffe838c39b8b19 |
The Gentlemen Linux Ransomware |
| TOX ID | F8E24C7F5B12CD69C44C73F438F65E9BF560ADF35EBBDF92CF9A9B84079F8F04060FF98D098E |
RaaS Administrator (zeta88 / hastalamuerte) |
| TOX ID | 15CE8D5DB0BAC3BCBB1FA69F2E672CC54EFBEC7684DA792F3CBF8B007A9FEA1D1637456 |
Affiliate TOX ID |
| TOX ID | 2F1A9C8B8AA163BBB84FF799A0954B232C279C5E9EE42505955288EAAD28685A2BC0713 |
Affiliate TOX ID |
| TOX ID | 88984846080D639C9A4EC394E53BA616D550B2B3AD691942EA2CCD33AA5B9340FD1A8FF |
Affiliate TOX ID |
| TOX ID | 98C132E2B20B531BE6604397D97040C1E9EB42FCE12EDF119BCE8B4031CA5C70DAF5E65 |
Affiliate TOX ID (most active) |
| TOX ID | D2CBA43A1AF6D965432AE11487726DB84D2945CF2CD975D7774B76B54AF052418AC2E59 |
Affiliate TOX ID |
| TOX ID | D527959A7BC728CB272A0DB683B547F079C98012201A48DD2792B84604E8BC29F6E6BDB |
Affiliate TOX ID |
| TOX ID | F96C481CBB0D6E7BDA49C6D68CFDB1D284354961534EDEEDA854C672B48A8D6B7146F90 |
Affiliate TOX ID |
| TOX ID | 7862AE03A73AAC2994A61DF1F635347F2D1731A77CACC155594C6B681D201F7AD6817AD3AB0A |
Account n7778 selling leaked RaaS data |
| File Name | README-GENTLEMEN.txt |
Ransomware ransom note file |
| File Name | gentlemen.bmp |
Ransomware wallpaper file |
| File Name | gentlemen_system |
Ransomware internal system identifier |
| CVE | CVE-2024-55591 |
FortiOS management interface vulnerability |
| CVE | CVE-2025-32433 |
Erlang SSH vulnerability (Cisco context) |
| CVE | CVE-2025-33073 |
NTLM reflection / relay vulnerability |
Note: IP addresses and domains are intentionally defanged (e.g., [.]) to prevent accidental resolution or hyperlinking. Re-fang only within controlled threat intelligence platforms such as MISP, VirusTotal, or your SIEM.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.