Anthropic Unveils Claude Mythos with Powerful Zero
Anthropic has unveiled Claude Mythos Preview, a powerful new language model capable of discovering and autonomously exploiting zero-day vulnerabilities. To ensure these powerful tools are used...
Anthropic has unveiled Claude Mythos Preview, a powerful new language model capable of discovering and autonomously exploiting zero-day vulnerabilities.
To ensure these powerful tools are used defensively, the company has launched Project Glasswing to collaborate with industry partners and patch critical software systems.
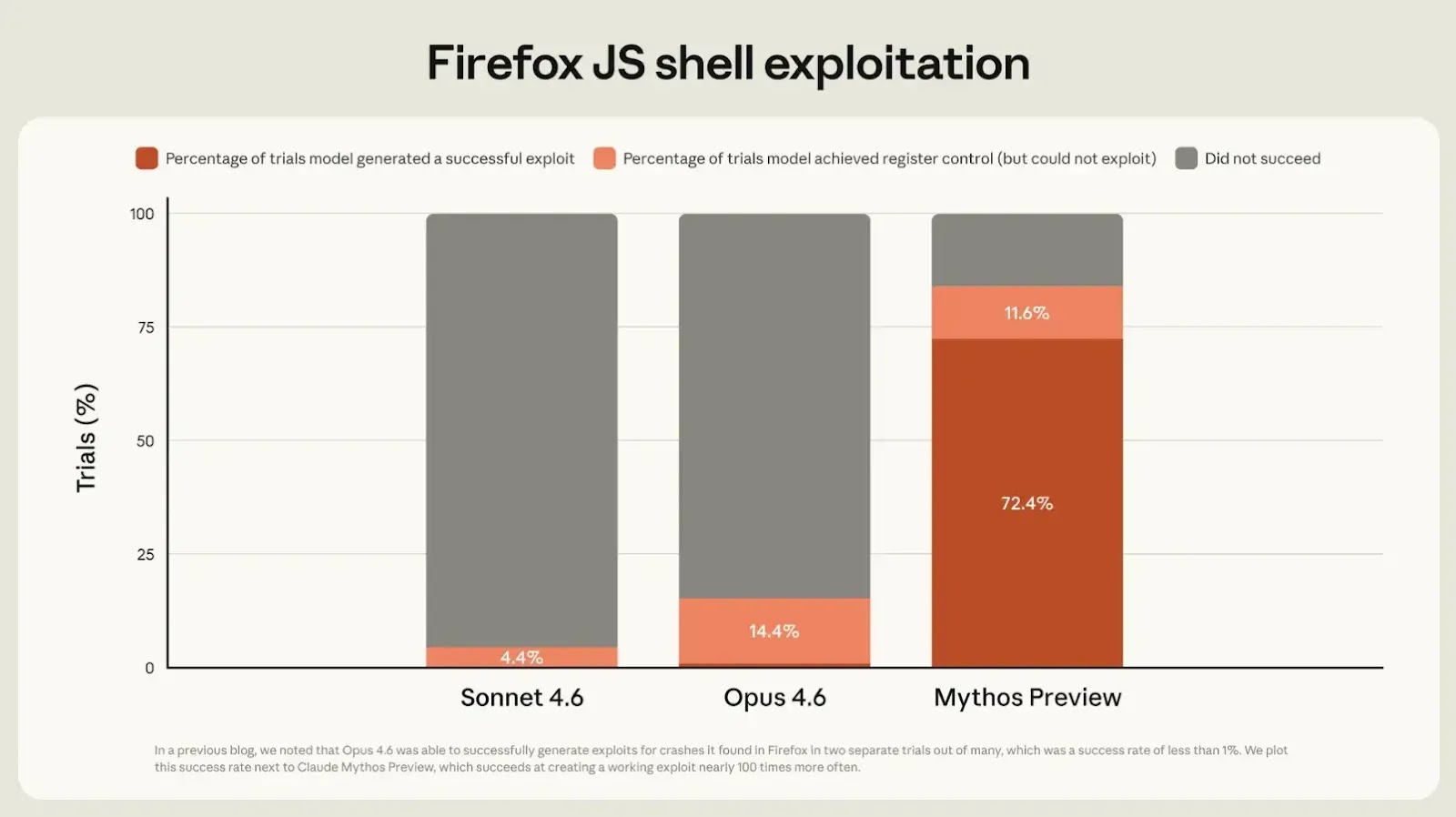
Claude Mythos Preview represents a massive upgrade over older models like Opus 4.6, which could find bugs but struggled to turn them into working exploits.
During internal tests using open-source software, the new model successfully achieved full control-flow hijacking on 10 fully patched targets.
These advanced offensive skills were not explicitly programmed; rather, they emerged naturally from the model’s overall improvements in logical reasoning and autonomous coding.
Autonomous Exploit Generation
The model can autonomously chain together multiple software flaws to create highly complex attacks that bypass modern security boundaries.
For example, it successfully wrote web browser exploits that evaded strict sandboxes and bypassed kernel address space layout randomization (KASLR) to gain elevated privileges.
Because the tool is highly automated, even users without any formal cybersecurity training have used it to generate fully working remote code execution exploits overnight.
When unleashed on real-world software, the AI agent discovered critical zero-day bugs that had remained hidden from human researchers for decades.
It successfully identified a 27-year-old memory corruption vulnerability in OpenBSD. This operating system is widely respected for its rigorous security standards.
Furthermore, it found a 16-year-old flaw in the highly audited FFmpeg media library by analyzing how the software decodes specific video frames.
The OpenBSD vulnerability was caused by a complex signed integer overflow in the network transmission control protocol, which the AI used to trigger a system crash.
The FFmpeg bug occurred due to a mismatch in integer sizes and memory initialization, allowing an attacker to force the program to write out-of-bounds data.
To find these flaws, the AI operates inside an isolated testing environment where it reads source code, tests hypotheses, and writes proof-of-concept exploits completely on its own.
Anthropic acknowledges that releasing such a powerful vulnerability-discovery tool could temporarily give malicious hackers a dangerous advantage.
To prevent this, Project Glasswing limits initial access to trusted defenders who can use the model to fix deep-seated bugs before they are actively exploited in the wild.
Ultimately, security experts believe that as the industry adapts, these advanced AI models will become essential defensive tools, making the global software ecosystem significantly safer.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.








No Comment! Be the first one.