0-Day Exploit Actively Attacks Adobe Reader Users Hackers Attacking
An unpatched, highly sophisticated zero-day exploit is actively targeting users of Adobe Reader. Discovered by the EXPMON threat-hunting system, the malicious PDF file is designed to steal sensitive...
An unpatched, highly sophisticated zero-day exploit is actively targeting users of Adobe Reader. Discovered by the EXPMON threat-hunting system, the malicious PDF file is designed to steal sensitive local data and perform advanced system fingerprinting.
The exploit functions flawlessly on the latest version of Adobe Reader. It requires no user interaction beyond simply opening the malicious document.
The attack begins when a victim opens a specially crafted PDF, initially submitted to malware analysis platforms under the file name “yummy_adobe_exploit_uwu.pdf”.
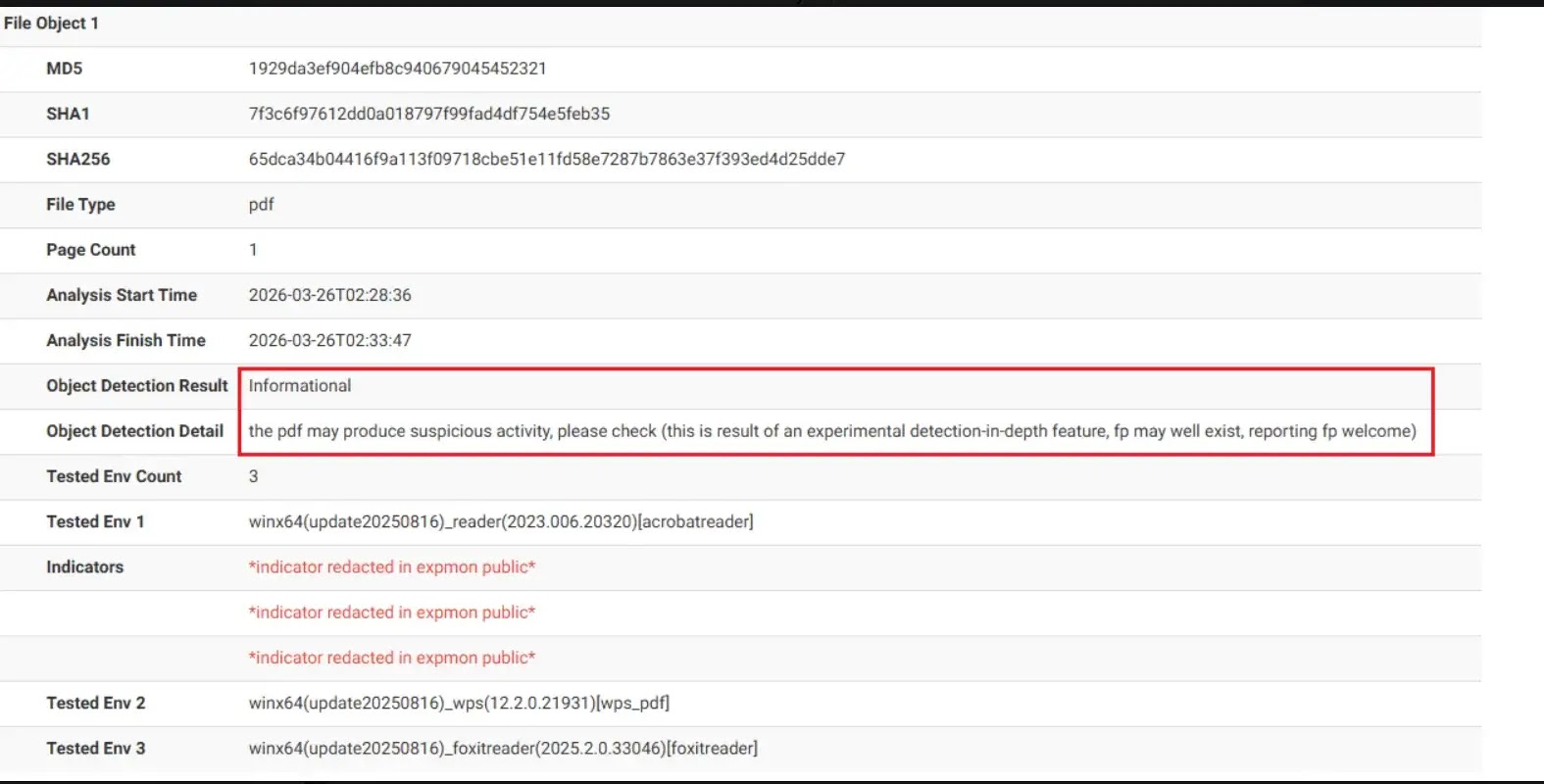
The malware successfully bypassed traditional antivirus tools, scoring a low initial detection rate on public scanning engines.
However, it triggered EXPMON’s advanced behavioral analytics by exhibiting highly suspicious activities within the Acrobat JavaScript engine.
To mask its malicious intent, the threat actors used Base64 encoding to embed the core script within hidden PDF objects.
Once de-obfuscated and opened, the exploit abuses an unpatched vulnerability to execute privileged programming commands.
First, it uses an internal application programming interface (API), util.readFileIntoStream(), to bypass standard sandbox protections and read arbitrary files on the victim’s local computer.
Next, the malware uses the RSS-addFeed() API to silently transmit the stolen information to a remote, attacker-controlled server.
This stolen data includes the exact operating system details, language settings, Adobe Reader version, and the PDF’s local file path.
Advanced System Fingerprinting
Security experts classify this as an advanced fingerprinting attack. The threat actors use the initial data theft to evaluate whether the victim’s machine meets their specific target criteria.
If the system is deemed a valuable target, the attacker’s server dynamically sends back additional malicious JavaScript payloads.
The malware utilizes cryptography to decrypt this incoming payload, a tactic specifically designed to evade network-based detection tools.
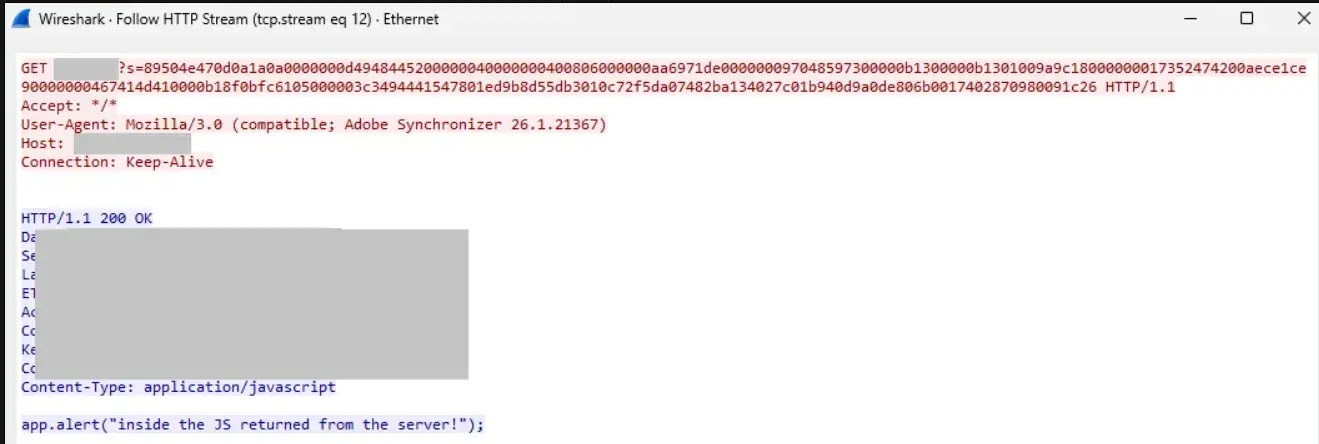
During controlled testing, researchers confirmed that this secondary payload mechanism is fully functional and capable of launching additional attacks, including Remote Code Execution (RCE) and Sandbox Escape (SBX).
This means attackers could theoretically bypass all remaining security boundaries to take complete control over the compromised machine.
Currently, this remains a zero-day threat, meaning no official patch from Adobe is available to prevent the initial data theft.
According to researcher justhaifei1, the vulnerability was responsibly disclosed to Adobe Security, individual users should implement the following precautions immediately:
- Exercise extreme caution: Do not open PDF files received from unknown, untrusted, or unverified sources.
- Block malicious infrastructure: Network administrators should monitor and block outgoing traffic communicating with the IP address 169.40.2.68 on port 45191.
- Monitor network traffic: Defenders should carefully inspect HTTP and HTTPS network traffic for suspicious activity containing the “Adobe Synchronizer” string within the User-Agent field.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.