Zero-Day Exploit Toolkit Actively H Hackers Exploiting
Hackers Exploiting VMware ESXi instances in the wild with a Zero-Day Exploit Toolkit. This toolkit chains multiple vulnerabilities, enabling virtual machine escapes. Cybersecurity firm Huntress...
Hackers Exploiting VMware ESXi instances in the wild with a Zero-Day Exploit Toolkit. This toolkit chains multiple vulnerabilities, enabling virtual machine escapes. Cybersecurity firm Huntress disrupted one such attack, attributing initial access to a compromised SonicWall VPN.
Threat actors gained a foothold via SonicWall VPN, then used a compromised Domain Admin account for lateral movement to backup and primary domain controllers.
On the primary DC, they deployed reconnaissance tools like Advanced Port Scanner and ShareFinder, staged data with WinRAR, and altered Windows firewall rules to block external outbound traffic while allowing internal lateral movement.
Approximately 20 minutes after toolkit deployment, they executed the ESXi exploit, which Huntress stopped before ransomware deployment.
VMware ESXi Instances Exploit Toolkit
The toolkit, dubbed MAESTRO by Huntress, orchestrates disabling VMware VMCI drivers with devcon.exe, loading an unsigned driver via KDU to bypass Driver Signature Enforcement, and executing the core escape.
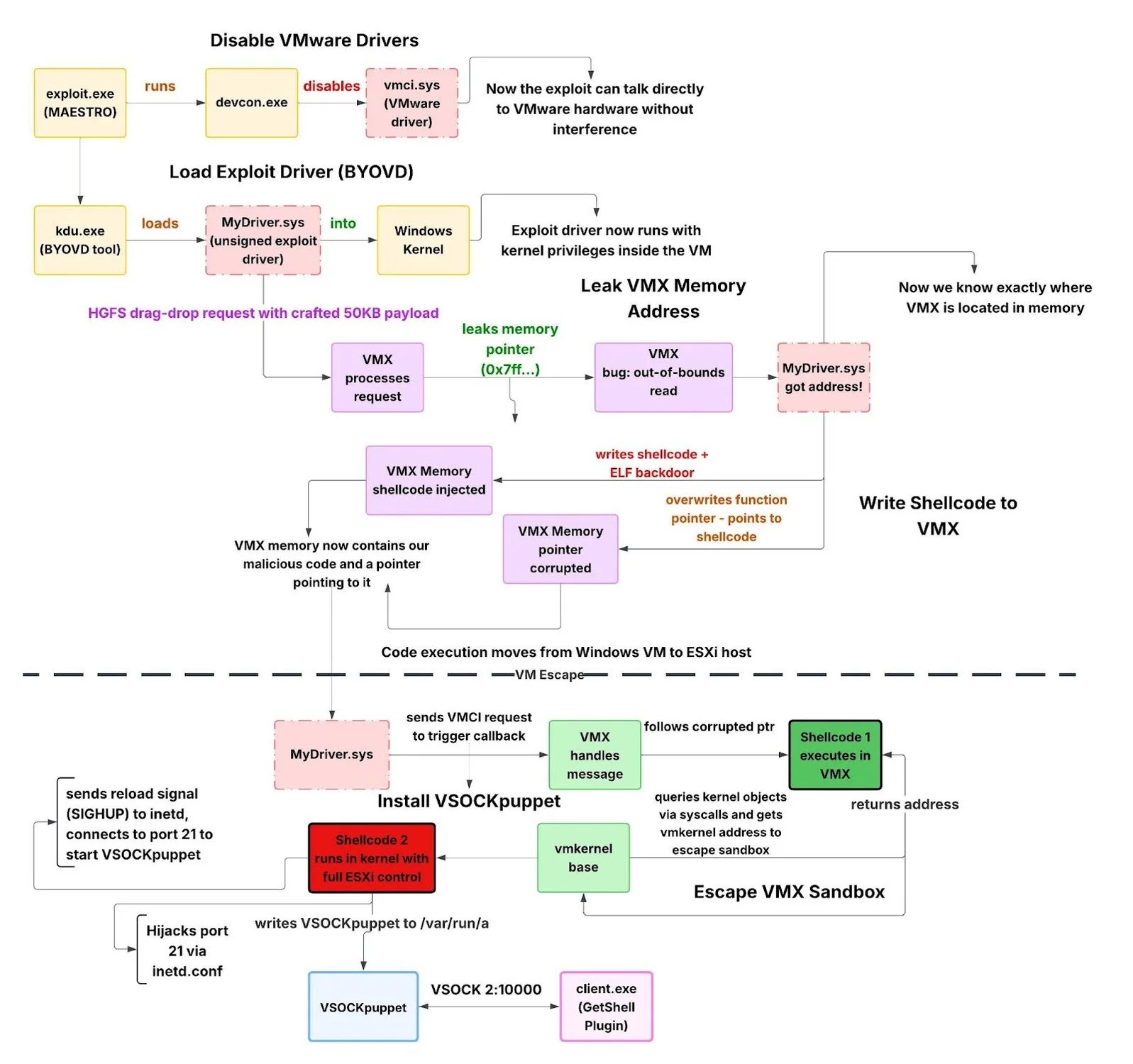
MyDriver.sys queries the ESXi version via VMware Guest SDK, selects offsets from a table supporting 155 builds across ESXi 5.1 to 8.0, leaks VMX base via HGFS (CVE-2025-22226), corrupts memory via VMCI (CVE-2025-22224), and deploys shellcode for sandbox escape (CVE-2025-22225).
| CVE ID | CVSS Score | Description |
|---|---|---|
| CVE-2025-22226 | 7.1 | Out-of-bounds read in HGFS leaking VMX memory |
| CVE-2025-22224 | 9.3 | Arbitrary write escaping the VMX sandbox to kernel |
| CVE-2025-22225 | 8.2 | Arbitrary write escaping the VMX sandbox to the kernel |
Shellcode stages deploy VSOCKpuppet, a backdoor hijacking ESXi’s inetd on port 21 for root execution, using VSOCK for stealthy guest-host communication invisible to network tools.
PDB paths reveal development in simplified Chinese environments, like “全版本逃逸–交付” (All version escape-delivery), dated February 2024, over a year before Broadcom’s VMSA-2025-0004 disclosure on March 4, 2025.
A client.exe PDB from November 2023 suggests modular tooling, with tampered VMware drivers referencing “XLab”. Huntress has high confidence in Chinese-speaking origins due to resources and zero-day access.
VM isolation fails against hypervisor flaws; patch ESXi urgently, as end-of-life versions lack fixes. Monitor ESXi hosts with “lsof -a” for VSOCK processes, watch for BYOD loaders like KDU, and secure VPNs. Firewall tweaks and unsigned drivers signal compromise; VSOCK backdoors evade IDS.
This incident underscores persistent hypervisor threats, with attackers prioritizing stealth via driver restoration and config cleanup post-exploitation. Organizations must harden virtualization aggressively amid rising ransomware targeting ESXi.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.