Malicious NPM Packages Attack Developers, Steal Three Attacking
Three malicious npm packages have been identified actively targeting JavaScript developers, aiming to steal browser logins, API keys, and cryptocurrency wallet data. The packages, named...
Three malicious npm packages have been identified actively targeting JavaScript developers, aiming to steal browser logins, API keys, and cryptocurrency wallet data.
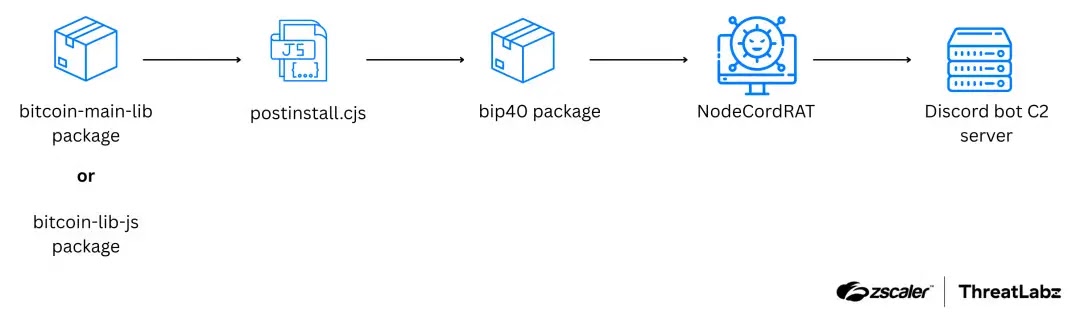
The packages, named bitcoin-main-lib, bitcoin-lib-js, and bip40, were uploaded to the public npm registry and posed as tools linked to the popular bitcoinjs project.
Any developer who added them as dependencies could silently install a new remote access trojan called NodeCordRAT.
NodeCordRAT is written in Node.js and uses Discord as its command-and-control (C2) channel, giving attackers remote shell and file access on compromised systems.
Once active, it hunts for Chrome login databases, .env files that may hold secrets like API tokens, and MetaMask data files tied to a popular browser wallet extension.
The goal is to loot credentials and sensitive project data straight from developer machines.
Zscaler ThreatLabz analysts identified the trio in November 2025 while scanning the npm registry for suspicious packages and strange download patterns.
They linked the libraries to a single author account and confirmed that the final payload, delivered through bip40, is a data-stealing RAT they named NodeCordRAT.
By copying names and details from real bitcoinjs components, the attacker made these lookalike modules appear harmless at a glance.
For victims, the attack chain looks like a normal package install: npm fetches bitcoin-main-lib or bitcoin-lib-js, runs the standard post-install script, and then pulls in bip40 as a dependency.
Attack flow
Behind the scenes, that flow ends with a remote attacker on a developer workstation that may hold cloud keys, source code, and access to production pipelines. While the attack flow can show how bip40 sits at the center of this staged infection path.
Infection mechanism details start in package.json, where the attacker adds script entries that look like normal build tasks but in fact trigger a custom installer. A typical snippet includes entries such as:-
"scripts": {
"postinstall": "node postinstall.cjs",
"bip40:start": "node postinstall.cjs"
}On install, this script runs without user input, resolves the bip40 module, and starts it as a background process using PM2 so it keeps running even after npm exits.
This gives the attacker a live access during the session, though it does not survive a full reboot by default.
Once active, NodeCordRAT connects to a hardcoded Discord server, listens for commands like !run or !sendfile, and streams stolen data and screenshots back over the same channel.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.