BlueDelta Hackers Steal Logins from Attacking Microsoft
BlueDelta, a Russian state-sponsored threat group affiliated with the GRU military intelligence agency, has significantly expanded its credential-stealing operations throughout 2025. Between February...
BlueDelta, a Russian state-sponsored threat group affiliated with the GRU military intelligence agency, has significantly expanded its credential-stealing operations throughout 2025.
Between February and September, the group launched multiple phishing campaigns designed to deceive users of Microsoft Outlook Web Access, Google, and Sophos VPN services into surrendering their login information.
This evolving threat demonstrates the group’s commitment to harvesting credentials from government officials, energy sector workers, and research professionals across Europe and Eurasia.
The attacks represent a clear evolution of BlueDelta’s long-standing tradecraft, which has targeted sensitive organizations since the mid-2000s.
The group focuses primarily on institutions connected to energy research, defense cooperation, and government communication networks.
The recent campaigns show increased sophistication in how BlueDelta combines multiple attack stages, custom code, and authentic-looking lure documents to bypass security controls and boost victim confidence.
Recorded Future analysts identified the malware after the second deployment phase, uncovering the technical mechanisms behind each attack.
The researchers discovered that BlueDelta relies heavily on free hosting services like Webhook.site, InfinityFree, Byet Internet Services, and ngrok to host the fake login pages and automatically capture stolen credentials.
This infrastructure strategy keeps operational costs minimal while maintaining flexibility through disposable services.
Multi-Stage Credential Capture Mechanism
The infection mechanism BlueDelta employs follows a carefully orchestrated chain of redirections designed to collect user data while maintaining a veneer of legitimacy.
When a victim clicks a phishing link, they first encounter legitimate PDF documents from organizations like the Gulf Research Center.
These documents display for approximately two seconds before the page automatically redirects to a spoofed login portal that mirrors the appearance of authentic Microsoft, Google, or Sophos interfaces.
The malicious code uses JavaScript functions to capture victim information systematically.
The code extracts email addresses from the URL parameters and sends a “page-opened” beacon containing the victim’s email, IP address, and browser information back to BlueDelta’s command server.
When victims enter their credentials, additional JavaScript captures the username and password, then transmits this information via HTTP POST requests to the attacker-controlled endpoint.
What makes this particularly effective is BlueDelta’s modification of the browser’s displayed URL.
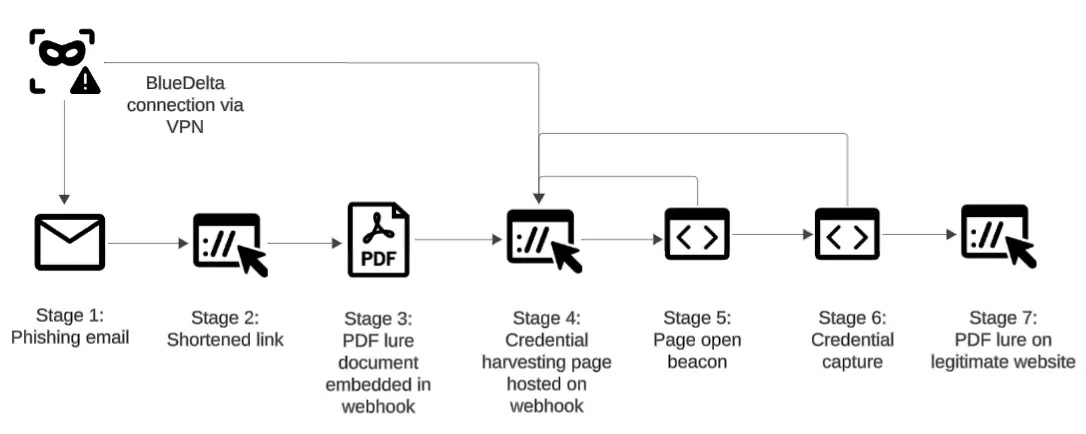
After credentials are submitted, the page changes from showing the phishing domain to displaying “/owa/” or “/pdfviewer?pdf=browser,” creating the impression of a legitimate application interface.
The page then redirects to the authentic PDF or a real login portal belonging to the targeted organization, making victims believe they completed a normal authentication process.
The group’s continuous refinement of these techniques illustrates a sophisticated understanding of user psychology and web browser behavior, allowing BlueDelta to maintain high success rates in credential harvesting while evading detection.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.