Windows RDP Flaw: Image Fragments Allow Att Remote Desktop
During any Windows Remote Desktop session, the operating system routinely saves visual fragments of the active display. As recently highlighted by SCYTHE Labs, attackers can easily extract these...
During any Windows Remote Desktop session, the operating system routinely saves visual fragments of the active display.
As recently highlighted by SCYTHE Labs, attackers can easily extract these breadcrumbs and rebuild them into readable screenshots.
This process requires no special privileges, takes just a few minutes, and relies entirely on free tools.
If your team uses Remote Desktop Protocol (RDP), you might be leaving behind a trail of highly sensitive data.
The RDP Bitmap Cache Risk
Windows uses a built-in performance feature called the RDP Bitmap Cache to speed up the loading of remote connections.
This cache stores small image tiles of your active session directly to your local hard drive.
Think of it like a web browser saving website thumbnails to speed up loading times.
However, these RDP tiles capture everything visible on your screen during the remote session.
This includes open internal tools, confidential documents, email inboxes, and even credentials typed into visible fields.
The critical issue is that this cache remains on the disk long after the connection terminates.
It sits in a standard user directory, meaning attackers do not need administrative privileges to access the files.
According to recent threat research, RDP represents nearly a third of overall security issues on the global enterprise attack surface.
Threat groups like BianLian, Medusa, and Scattered Spider frequently exploit RDP access, turning this default cache into a powerful and undetected reconnaissance tool.
Extracting and Rebuilding Images
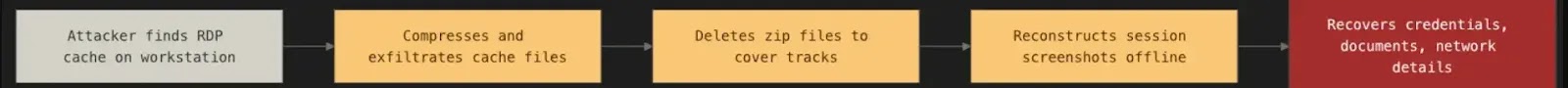
Adversaries can easily locate the cache folder because it always resides in the local application data path on every Windows machine.
They typically use a simple PowerShell command to compress the cache folder into a zip archive.
Attackers then exfiltrate this archive over standard HTTPS, which easily blends in with normal outbound network traffic, before deleting the zip file to cover their tracks.
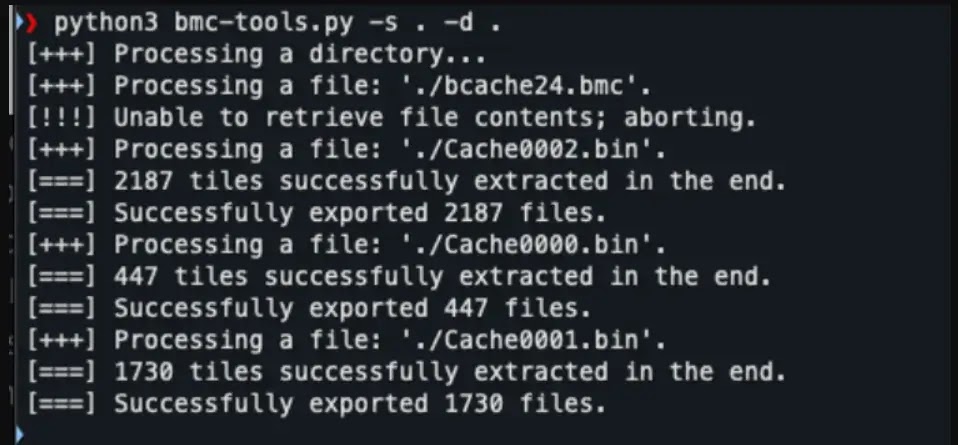
Once attackers possess the extracted files, they rely on two open-source tools to visualize the stolen data.
First, an application like bmc-tools parses the raw cache files into thousands of tiny image tiles.
Next, a visualization tool like RdpCacheStitcher arranges these scattered tiles like a jigsaw puzzle to rebuild the original session screen.
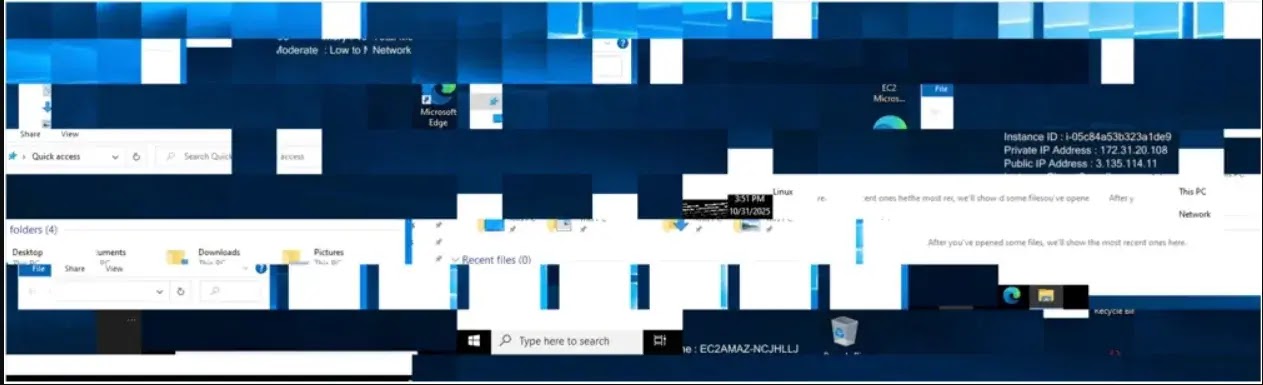
Even partial image reconstructions often reveal enough environmental details to fuel the next phase of a cyberattack.
This cache serves as an important indicator of compromise, even when attackers attempt to hide their tracks.
Threat actors who use RDP during an intrusion often delete the cache directory entirely before logging out.
Finding an empty bitmap cache on a workstation with a long history of Remote Desktop usage is highly suspicious.
Security teams should always treat this sudden absence of evidence as a strong signal to launch an investigation.
SCYTHE researchers emphasize that defending against this exposure by improving monitoring visibility and adjusting default system configurations.
Implement these practical defense measures to secure your endpoints.
- Verify that your endpoint detection systems flag unauthorized access to the local RDP cache folder.
- Confirm that outbound HTTPS transfers of compressed archives from temporary directories generate immediate alerts.
- Test if your security tools catch PowerShell compression commands targeting the local application data directory.
- Turn off the cache entirely using a standard Windows Group Policy setting to eliminate the risk.
- Add RDP cache review checks to your standard incident response playbook to actively look for suspiciously missing files.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.