Windows Error Reporting Flaw Grants SYSTEM Access Escalation
Analysis has revealed a local privilege escalation vulnerability within the Windows Error Reporting (WER) service, allowing attackers to easily gain full SYSTEM access. The flaw, tracked as...
Analysis has revealed a local privilege escalation vulnerability within the Windows Error Reporting (WER) service, allowing attackers to easily gain full SYSTEM access.
The flaw, tracked as CVE-2026-20817, was considered so structurally dangerous that Microsoft completely removed the vulnerable feature rather than attempting a traditional code patch.
The security flaw exists within the main executable library of the Windows Error Reporting service, specifically the WerSvc.dll file.
According to vulnerability researchers Denis Faiustov and Ruslan Sayfiev at GMO Cybersecurity, the service suffers from improper handling of insufficient permissions when processing specific client requests.
This architectural weakness provides a reliable pathway for a low-privileged local user to trigger an elevated command execution primitive.
Historically, the Windows Error Reporting service has been a frequent target for privilege escalation attacks due to its complex inter-process communication requirements.
To exploit this specific flaw, the attacker must first connect to the ALPC port using the NtAlpcConnectPort API and subsequently send their payload using the NtAlpcSendWaitReceivePort API.
The malicious data structure must contain exactly the right MessageFlags parameter and structural padding to successfully trigger the vulnerable dispatcher logic.
The Exploitation Mechanism
The core of this vulnerability involves the manipulation of Advanced Local Procedure Call (ALPC) messages sent to the WindowsErrorReportingServicePort endpoint.
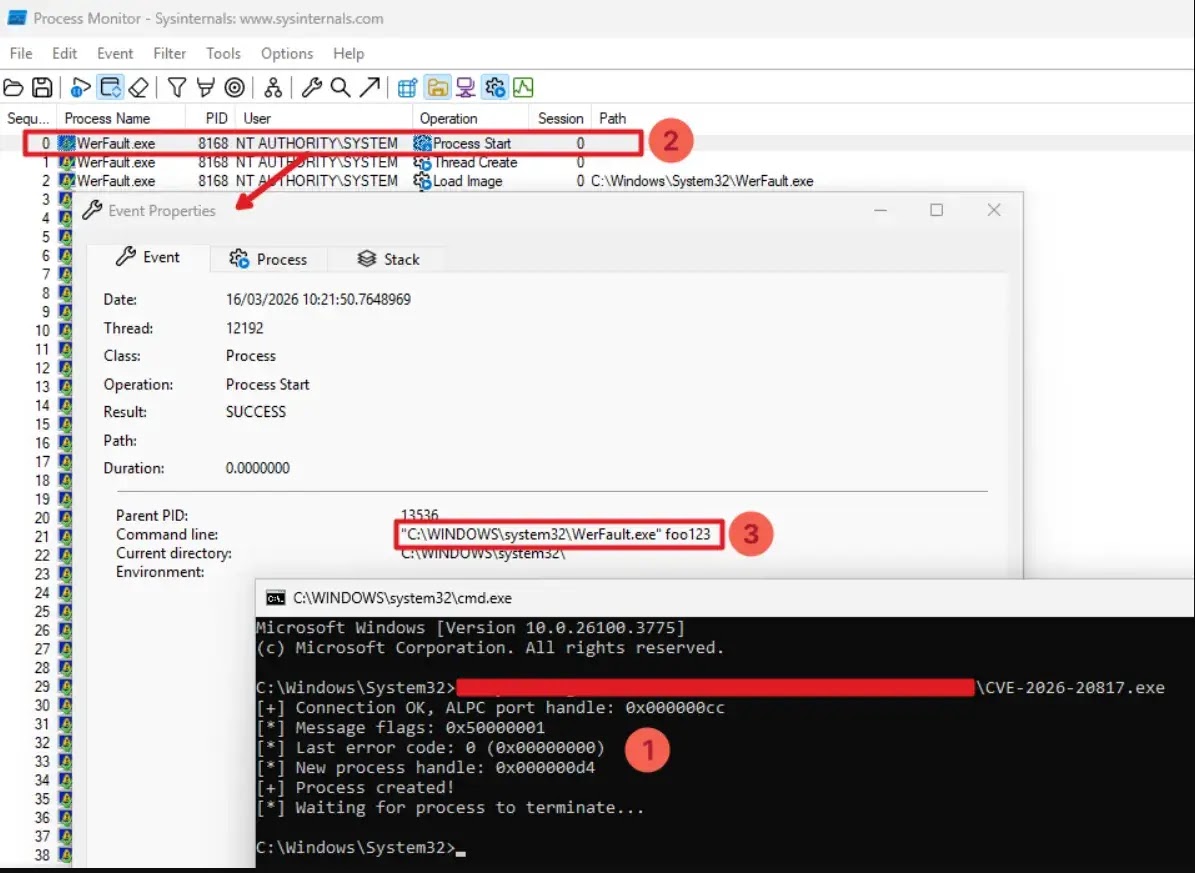
An attacker crafts a message containing a File Mapping object, prompting the internal ElevatedProcessStart function to duplicate the handle and read the malicious command-line arguments using the MapViewOfFile API.
Ultimately, the CreateElevatedProcessAsUser function is called, which inadvertently launches the legitimate WerFault.exe application with highly privileged SYSTEM rights and the attacker’s heavily controlled parameters.
Security analysts performing binary diffing between versions 10.0.26100.7309 and 10.0.26100.7623 of the WerSvc.dll file discovered that Microsoft took an unusually aggressive approach to remediation.
Instead of adding permission checks or input sanitization routines, developers introduced a strict __private_IsEnabled() feature test that permanently disables the SvcElevatedLaunch functionality.
If the patched code is executed, the function immediately returns an 0x80004005 (E_FAIL) error code, effectively neutralizing the entire attack surface by removing the feature entirely.
Weaponization and Detection
While the vulnerability successfully forces the execution of WerFault.exe as SYSTEM, attackers must combine specific command-line options with advanced Windows internal tricks to achieve arbitrary code execution.

During the exploit process, the WER service uses parent process ID spoofing to make the new elevated process appear as a direct child of the attacker’s low-privileged client.
Because this specific process spoofing technique is heavily abused by modern malware, security solutions like Microsoft Defender actively detect the behavior and raise immediate alerts.
Cybersecurity professionals must remain highly vigilant when researching this specific local privilege escalation threat.
Multiple fake and potentially malicious proof-of-concept repositories for CVE-2026-20817 have appeared on platforms like GitHub.
These deceptive project files often contain hidden malware payloads, serving as a critical reminder to carefully isolate and statically analyze all downloaded security tools before execution.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.