Leaks Expose Hidden Infrastructure of Ransomware Operations
The cybercrime world operates largely in the shadows. Yet, when internal disputes cause insiders to turn against each other, those shadows inevitably shrink, revealing previously hidden...
The cybercrime world operates largely in the shadows. Yet, when internal disputes cause insiders to turn against each other, those shadows inevitably shrink, revealing previously hidden infrastructure.
In February 2025, an individual using the alias ExploitWhispers surfaced on Telegram and released internal communications from the BlackBasta ransomware group.
The leak contained a JSON file with roughly 200,000 messages spanning over a year, from September 2023 to September 2024.
Among the exposed details were real identities, including Kirill Zatolokin, better known in underground forums as Slim Shady. This revelation marked the beginning of a chain reaction that would unravel an entire criminal infrastructure network.
The first leak was followed by another in March 2025, when an unknown actor released a database connected to Media Land, a Russian business that appeared legitimate on the surface.
The database revealed server configurations, client purchase records, user account information, and cryptocurrency wallet addresses.
The question arose: why would a supposedly legitimate company be entangled in ransomware operations? The answer proved straightforward yet damning—Media Land was actually Yalishanda, a bulletproof hosting provider that had been operating since late 2009, serving as a critical backbone for cybercriminal activities.
Analyst1 analysts identified how these two leaks connected the dots between BlackBasta and the infrastructure supporting it.
Russian cybercrime operates as a multi-layered ecosystem where ransomware groups rely on protection services, cover companies, and infrastructure providers that often masquerade as legal entities.
Yalishanda, under the legitimate front of Media Land, provided the hosting and technical support that enabled BlackBasta to conduct its attacks without interference.
This relationship represented a professionalized criminal supply chain where each component played a specialized role.
The leaks prompted swift regulatory action. On November 19, 2025, the U.S. Department of the Treasury’s Office of Foreign Assets Control, working alongside authorities in Australia and the United Kingdom, imposed sanctions on Media Land and its subsidiary, Data Center Kirishi.
Two individuals faced direct consequences: Aleksandr Volosovik, the company’s director known in criminal circles as Yalishanda, and Kirill Zatolokin, who played a hands-on role in supporting BlackBasta’s operations.
Volosovik had marketed infrastructure to threat actors while Zatolokin handled customer support and technical coordination under his Slim Shady alias.
The Role of Bulletproof Hosting in Ransomware Operations
Bulletproof hosting providers like Yalishanda thrive on a single promise: they ignore abuse complaints.
For ransomware operators, this creates a safe haven where command-and-control servers, data exfiltration infrastructure, and payment portals can operate without disruption.
Yalishanda offered a comprehensive service package that included server hosting, domain registration, technical support, and most importantly, protection from takedown requests.
The leaked BlackBasta chats revealed that the group maintained approximately 200 servers through Media Land’s infrastructure, consuming between 17 to 20 gigabits per second of bandwidth with plans to scale up to 50 gigabits per second.
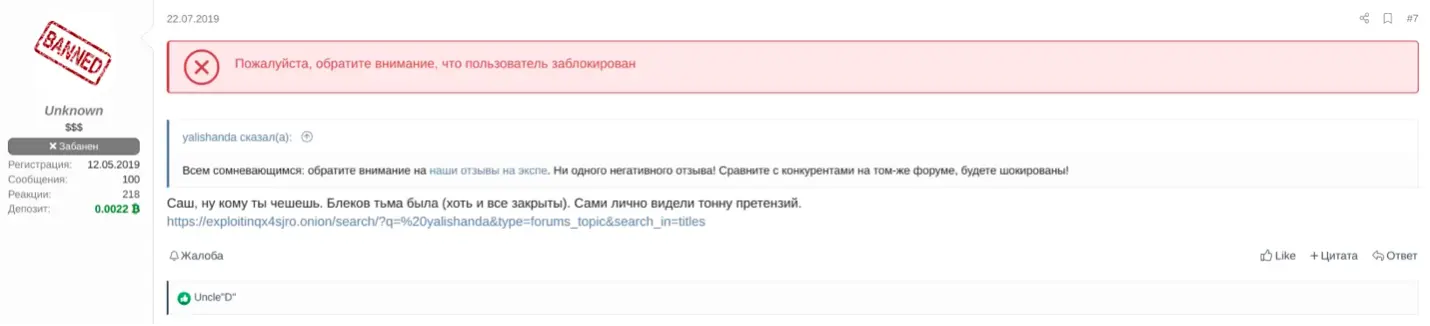
REvil member using the moniker Unknown engaged in a conversation with a Yalishanda representative (Source – Analyst1)
Zatolokin operated as the primary technical contact between BlackBasta and Media Land, coordinating infrastructure needs through his Telegram account @ohyehhellno.
Messages from the leaked chats showed him providing speed test results, bandwidth calculations, and upgrade recommendations.
In one exchange, he described Media Land’s services as coming from a “private data center” rather than rented networks, emphasizing the VIP treatment BlackBasta received.
This level of dedicated infrastructure support demonstrates how modern ransomware groups rely on professional service providers rather than managing their own technical operations, allowing them to focus on victim targeting and encryption while outsourcing the complexity of maintaining resilient, abuse-resistant infrastructure.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.