Attackers Impersonate MalwareBytes to Steal Threat Actors
A new malware campaign is actively tricking users into downloading fraudulent Malwarebytes software. This deceptive tactic puts their login credentials and cryptocurrency wallets at serious risk....
A new malware campaign is actively tricking users into downloading fraudulent Malwarebytes software. This deceptive tactic puts their login credentials and cryptocurrency wallets at serious risk.
Security researchers discovered this operation actively spreading between January 11 and January 15, 2026, using specially crafted ZIP files that impersonate legitimate Malwarebytes installers.
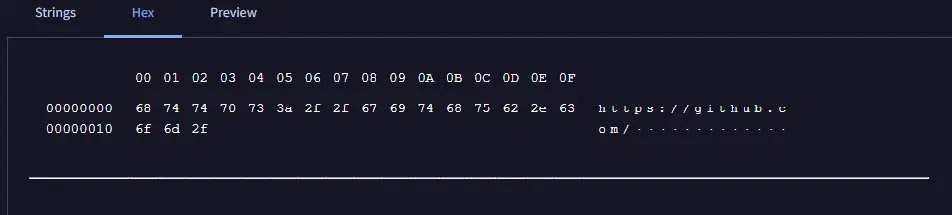
The fake files are named malwarebytes-windows-github-io-X.X.X.zip, making them appear authentic to unsuspecting users who believe they are downloading genuine antivirus protection.
The campaign’s primary goal centers on delivering an information-stealing malware that harvests sensitive user data.
These malicious ZIP archives contain a dangerous combination of files designed to bypass security defenses and establish persistence on infected systems.
When users extract and run what appears to be the legitimate Malwarebytes executable, they unknowingly trigger a chain of malicious events that ultimately compromises their digital security and personal information.
VirusTotal analysts identified the malware after examining the infection patterns and file structures, noting that all suspicious ZIP archives share a consistent identifier known as a behash value of “4acaac53c8340a8c236c91e68244e6cb.”
This technical marker became crucial in tracking the campaign’s scope and identifying additional variants used in the operation.
The researchers documented how the malware operates through a sophisticated layering technique that makes detection and analysis more challenging.
DLL Sideloading: The Attack Mechanism
The attack relies on a deceptive technique called DLL sideloading, which exploits how Windows loads legitimate software libraries. The malicious payload is hidden inside a file named CoreMessaging.dll.
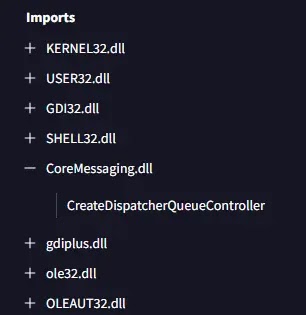
When the legitimate Malwarebytes executable runs, the operating system loads this malicious DLL instead of the genuine library file.
Threat actors place both the fake DLL and legitimate EXE in the same folder, tricking Windows into executing the malware without raising suspicion.
The malicious DLLs feature distinctive metadata including signature strings like “© 2026 Eosinophil LLC” and unusual exported functions containing alphanumeric sequences such as “15Mmm95ml1RbfjH1VUyelYFCf” and “2dlSKEtPzvo1mHDN4FYgv.”
These characteristics allow security researchers to hunt for related samples and track the broader campaign.
Once the malicious DLL executes, it drops secondary-stage infostealers that specifically target cryptocurrency wallet information and stored browser credentials, enabling attackers to commit identity theft and cryptocurrency theft.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.