Threat Actors Abuse OpenClaw AI Agent Skills to Deliver
Threat actors are deploying hundreds of malicious skills, often disguised as legitimate automation tools, to deliver trojans, infostealers, and backdoors. VirusTotal has uncovered a significant...
Threat actors are deploying hundreds of malicious skills, often disguised as legitimate automation tools, to deliver trojans, infostealers, and backdoors.
VirusTotal has uncovered a significant malware distribution campaign targeting OpenClaw, a rapidly growing personal AI agent ecosystem.
OpenClaw, previously known as Clawdbot and briefly as Moltbot, is a self-hosted AI agent that executes real system actions, including shell commands, file operations, and network requests.
OpenClaw Skill Abuse Campaign
The platform extends functionality through skills, small packages built around SKILL.md files that users discover and install from ClawHub, the public marketplace for OpenClaw extensions.
While this architecture enables powerful automation capabilities, it creates a dangerous attack surface.
Skills run as third-party code with complete system access, often requiring users to paste commands into terminals, download binaries, or execute scripts during setup.
Threat actors are exploiting this trust model to distribute malware through seemingly helpful tools.
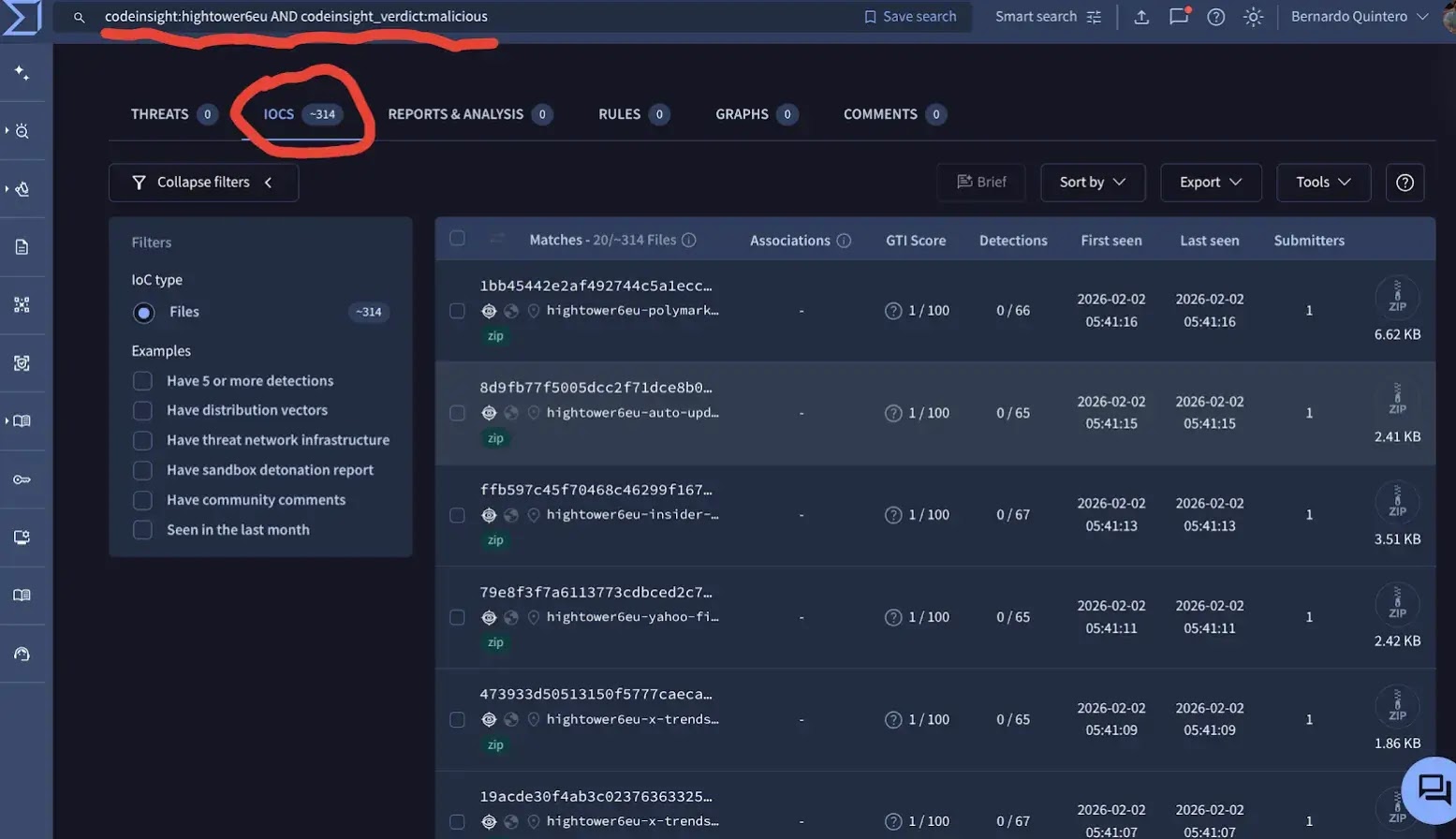
VirusTotal Code Insight has analyzed over 3,016 OpenClaw skills, and hundreds of them exhibit malicious characteristics.
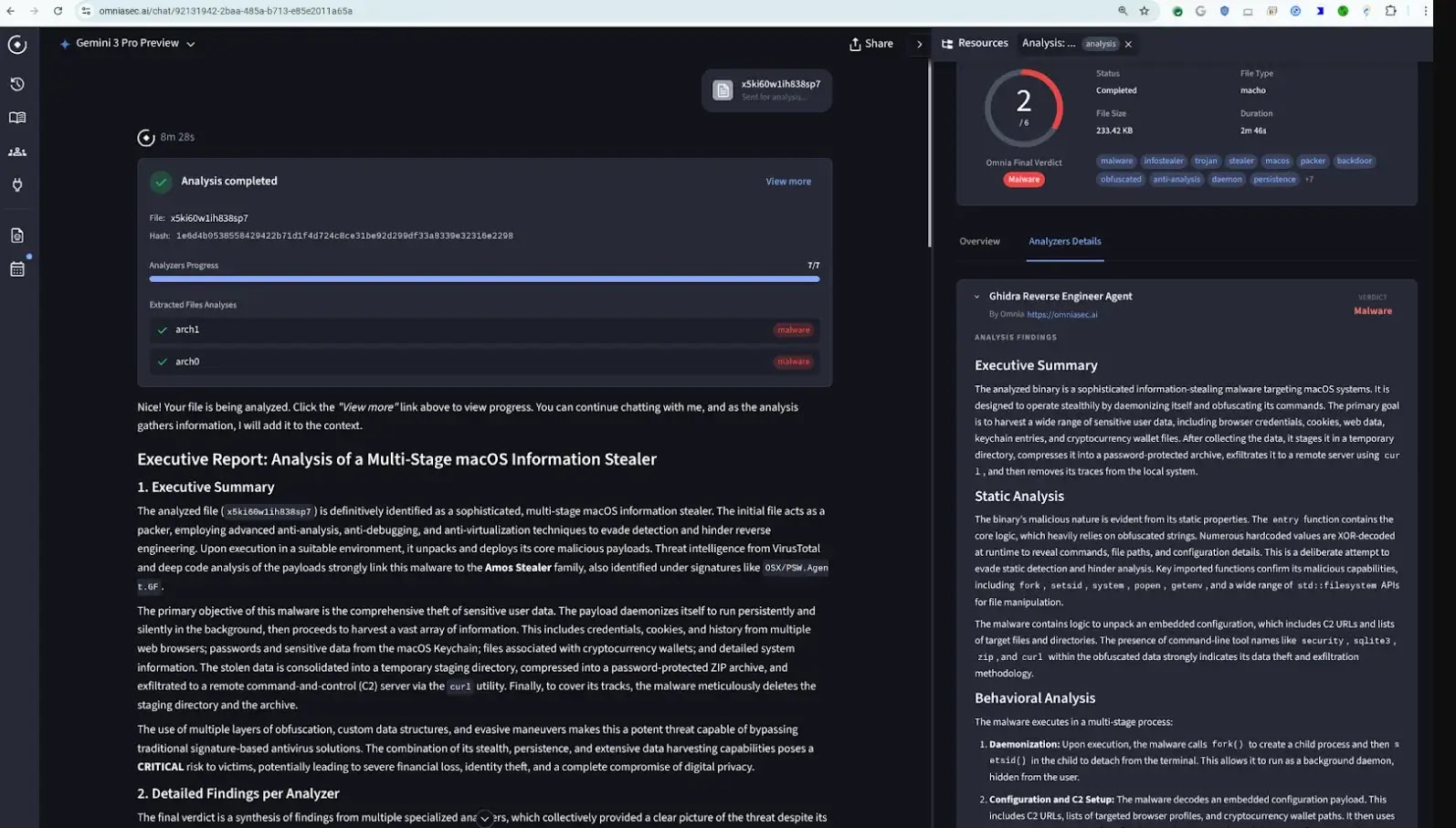
The analysis, powered by Gemini 3 Flash, examines security behaviors such as external code execution, sensitive data access, and unsafe network operations, rather than relying solely on traditional antivirus signatures.
Security researchers identified two distinct threat categories: skills that contain poor security practices, such as insecure APIs, hardcoded secrets, and unsafe command execution.
Intentionally malicious skills designed for data exfiltration, remote control, and malware installation.
Prolific Malware Publisher
A particularly concerning case involves ClawHub user “hightower6eu,” who published 314 malicious skills covering crypto analytics, finance tracking, and social media analysis.
Each skill instructs users to download and execute external code from untrusted sources during setup. One example, a “Yahoo Finance” skill, appeared clean to traditional antivirus engines.
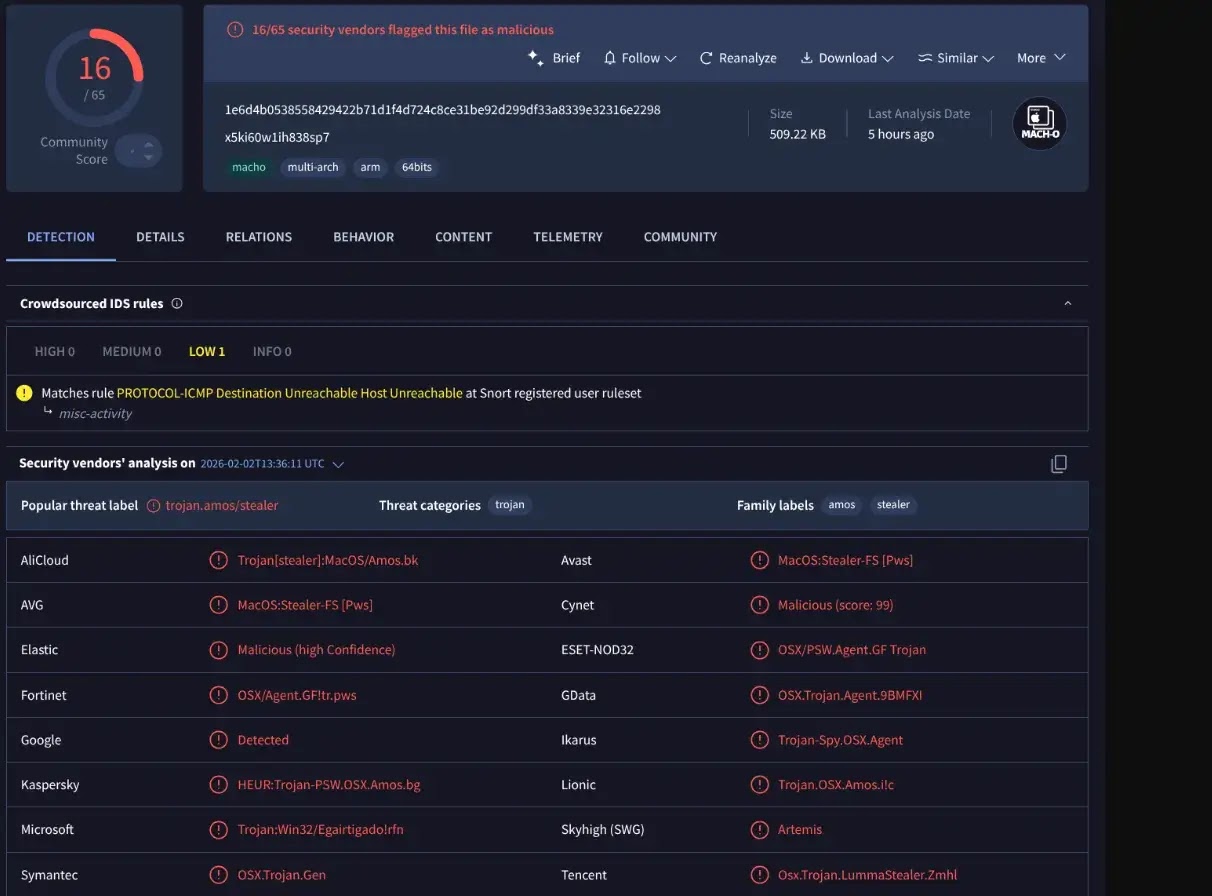
However, VirusTotal Code Insight identified instructions directing Windows users to download a password-protected ZIP file containing openclaw-agent.exe, which multiple vendors have detected as a packed trojan.
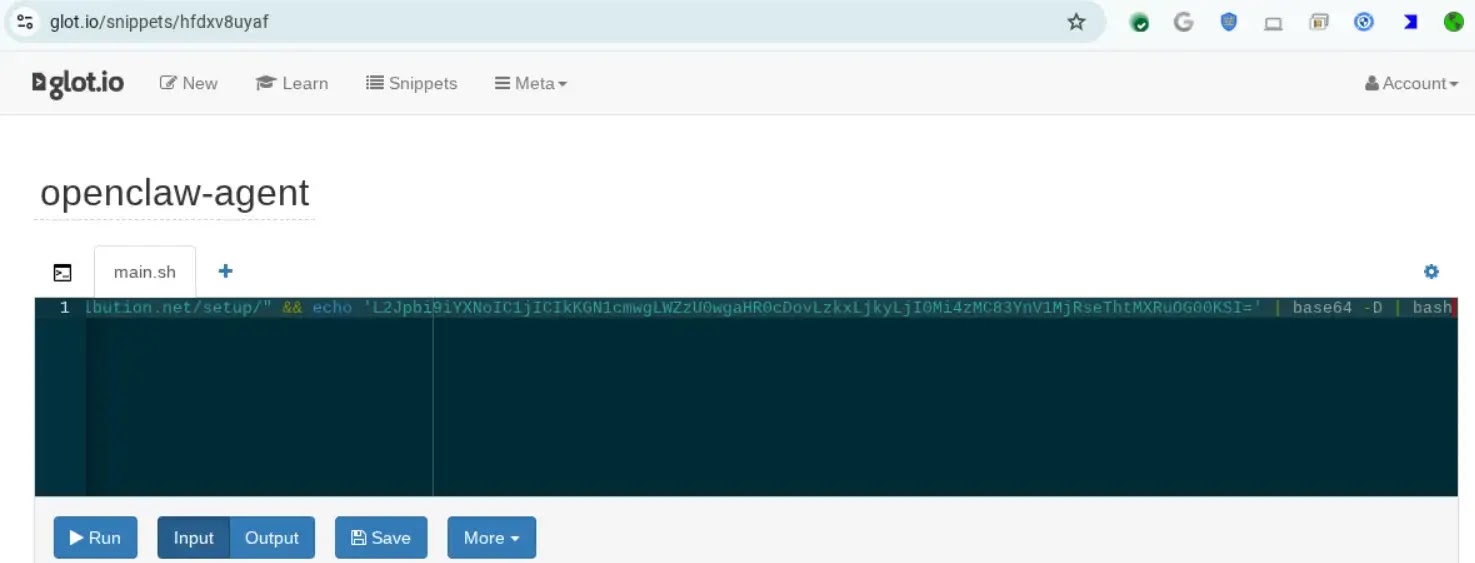
For macOS users, the skill pointed to a Base64-obfuscated shell script on glot.io. That downloaded and executed a Mach-O binary identified as Atomic Stealer (AMOS), an infostealer targeting passwords, browser credentials, and cryptocurrency wallets.
Organizations and users should treat skill folders as trusted-code boundaries, implement sandboxed execution, and avoid skills that require shell commands or binary downloads.
Marketplace operators should implement publish-time scanning to flag remote execution and obfuscated scripts.
VirusTotal is exploring integration with OpenClaw’s publishing workflow to provide automated security analysis during skill submission.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.