SystemBC Botnet Hijacked 10,000 Devices Worldwide to Use for DDoS
The SystemBC malware family has escalated into a significant global threat. First documented in 2019, this persistent malware now forms a massive botnet infrastructure, controlling over 10,000...
The SystemBC malware family has escalated into a significant global threat. First documented in 2019, this persistent malware now forms a massive botnet infrastructure, controlling over 10,000 hijacked devices worldwide.
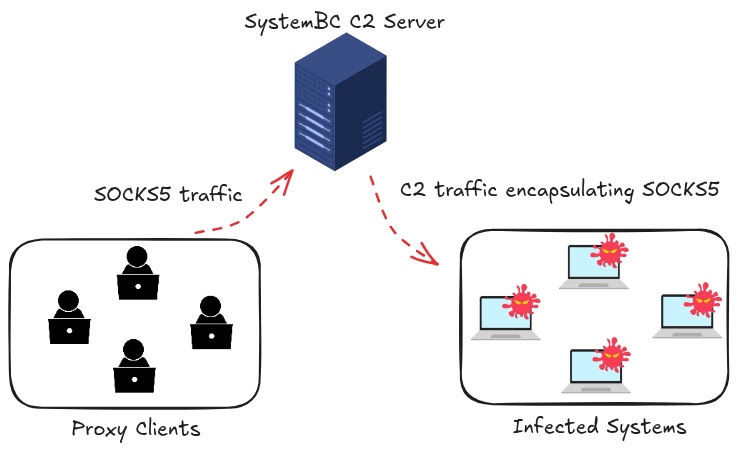
Functioning primarily as a SOCKS5 proxy and a backdoor, this malware enables threat actors to mask their malicious traffic and maintain long-term access to compromised networks.
By converting infected systems into relays, the botnet allows attackers to route command-and-control communications through victim machines, effectively hiding their true location from defenders and complicating attribution efforts.
This “backconnect” architecture creates a resilient network that has survived significant law enforcement disruptions, including Europol’s Operation Endgame in May 2024.
Rather than disappearing, the infrastructure has adapted, shifting its focus toward compromising hosting providers instead of residential networks.
This strategic pivot allows infections to persist significantly longer than typical malware campaigns, with the average system remaining compromised for 38 days and some infections lasting over 100 days.
The botnet serves as a critical precursor to ransomware deployments, tunneling traffic for data theft and further exploitation.
Silent Push analysts noted that the botnet’s resurgence involves sophisticated tracking of infected IP addresses across the globe.
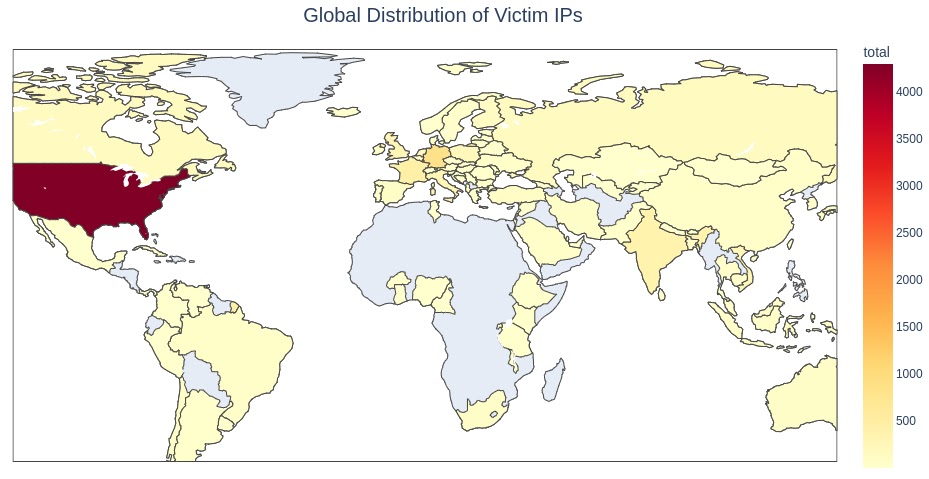
Their research identified the United States as the primary target, hosting more than 4,300 compromised devices, followed by significant concentrations in Germany, France, and Singapore.
Investigations also revealed alarming breaches within sensitive government environments, including high-density servers hosting official websites in Vietnam and Burkina Faso.
These compromised assets are frequently leveraged to launch additional attacks or support other criminal operations.
Undetected Perl Variant Analysis
A critical aspect of this campaign is the discovery of a previously undocumented SystemBC variant written in Perl, designed specifically to evade traditional security controls.
Files communicating with the botnet’s command infrastructure included this unusual script, which initially registered zero detections across major antivirus engines.
This variant is typically deployed by ELF binary droppers, identified as “SafeObject” and “StringHash,” which use UPX packing to conceal their malicious code from static analysis tools.
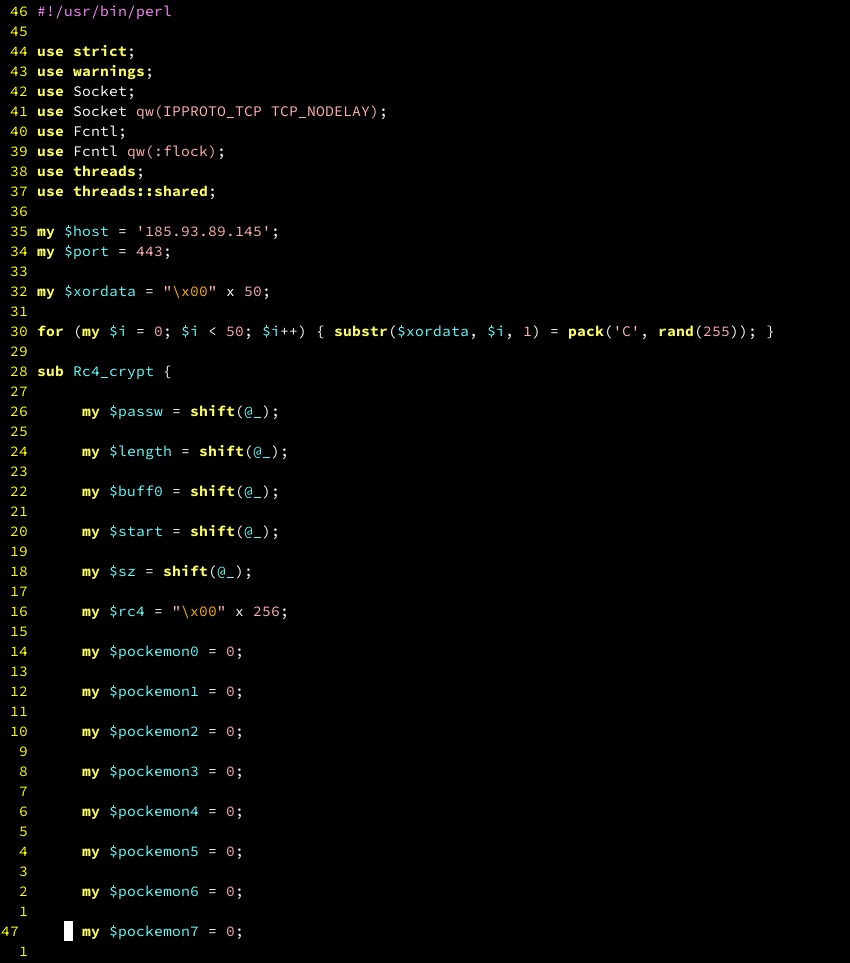
Once unpacked, these droppers aggressively hunt for writable directories on the host system before executing hundreds of embedded payloads.
The investigation into the dropper code revealed it is unusually “noisy” and filled with Russian-language strings, offering a potential clue regarding the threat actor’s origins.
Since SystemBC infrastructure often signals the early stages of an intrusion chain, security teams are recommended to prioritize proactive monitoring of these indicators to prevent the escalation to ransomware.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.