node-ipc npm Package Compromised in Supply Weekly Downloads
The widely used JavaScript inter-process communication library, node-ipc, has once again fallen victim to a supply chain attack. Security firms Socket and Stepsecurity confirmed that three recently...
The widely used JavaScript inter-process communication library, node-ipc, has once again fallen victim to a supply chain attack. Security firms Socket and Stepsecurity confirmed that three recently published versions of the package, which sees over 822,000 weekly downloads, now contain obfuscated stealer and backdoor payloads. This marks node-ipc’s second major supply chain compromise since 2022.
The affected versions are [email protected], [email protected], and [email protected].
node-ipc npm Package Hacked
Security researcher Ian Ahl (@TekDefense), CTO at Permiso, identified the likely attack vector as a dormant maintainer account takeover.
The account “atiertant,” one of twelve listed npm maintainers, had been inactive for years.
According to Socket security, attackers appear to have acquired the account’s recovery email domain atlantis-software[.]net after it expired, allowing them to trigger a standard npm password reset and silently gain publish rights without ever touching the original maintainer’s infrastructure.
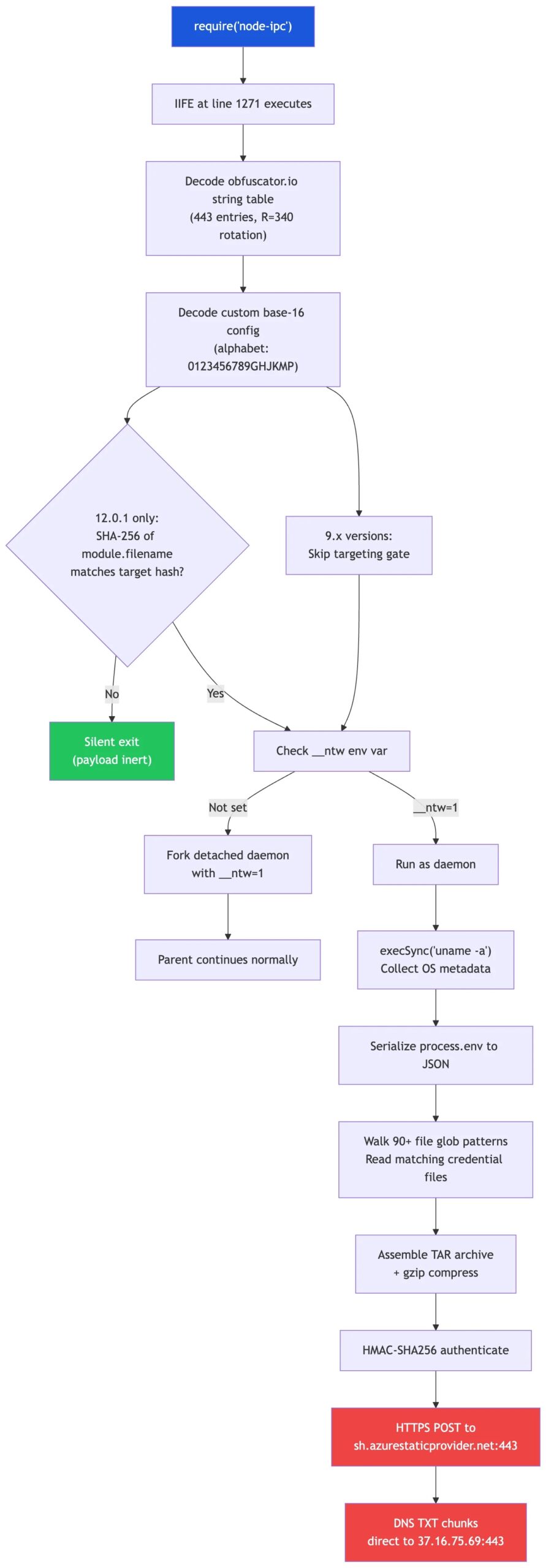
The malicious payload is embedded exclusively in node-ipc.cjs, the CommonJS entrypoint, appended as a single obfuscated IIFE.
The ESM module remains clean. This means developers using require("node-ipc") are at risk, while pure ESM consumers may not be directly affected.
Once triggered via setImmediate() on module load, the payload forks a detached child process using the __ntw=1 environment variable flag, then proceeds to:
- Fingerprint the host using OS metadata, including platform, architecture, hostname, and
uname -aoutput - Harvest credentials and configuration files from over 100 target patterns, covering AWS, Azure, GCP, Kubernetes, Docker, SSH keys, npm tokens, GitHub/GitLab credentials, Terraform secrets,
.envfiles, shell histories, and macOS Keychain databases - Archive collected data into a gzip tarball written to
<tmp>/nt-<pid>/<machineHex>.tar.gz - Exfiltrate via DNS TXT queries — not HTTP — using a fake Azure lookalike domain,
sh[.]azurestaticprovider[.]net, routing data through the zonebt[.]node[.]jswith query prefixesxh,xd, andxf
A 500 KiB compressed archive can generate approximately 29,400 DNS TXT queries, making high-volume TXT query bursts a strong detection signal.
Notably, every file in the malicious tarballs carries a forensic timestamp of October 26, 1985, a deliberate artifact useful for identifying cached or mirrored copies.
Indicators of Compromise (IOCs)
| Type | Indicator |
|---|---|
| Malicious packages | [email protected], [email protected], [email protected] |
| node-ipc.cjs SHA-256 | 96097e0612d9575cb133021017fb1a5c68a03b60f9f3d24ebdc0e628d9034144 |
| node-ipc-9.1.6.tgz SHA-256 | 449e4265979b5fdb2d3446c021af437e815debd66de7da2fe54f1ad93cbcc75e |
| node-ipc-9.2.3.tgz SHA-256 | c2f4dc64aec4631540a568e88932b61daebbfb7e8281b812fa01b7215f9be9ea |
| node-ipc-12.0.1.tar.gz SHA-256 | 78a82d93b4f580835f5823b85a3d9ee1f03a15ee6f0e01b4eac86252a7002981 |
| C2 bootstrap domain | sh[.]azurestaticprovider[.]net |
| C2 IP | 37.16[.]75.69 |
| Exfiltration DNS zone | bt[.]node[.]js |
| Runtime env variable | __ntw=1 |
| Temp archive pattern | <tmp>/nt-<pid>/<machineHex>.tar.gz |
[.]) to prevent accidental resolution or hyperlinking. Re-fang only within controlled threat intelligence platforms such as MISP, VirusTotal, or your SIEM.Developers should immediately remove the three affected versions and audit package-lock.json, yarn.lock, and local npm caches.
Any environment variables, SSH keys, cloud credentials, or API tokens present on a system that loaded the CommonJS entrypoint should be treated as fully compromised and rotated without delay.
Security teams should hunt for DNS TXT query bursts to bt[.]node[.]js and block the bootstrap resolver domain.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.







No Comment! Be the first one.