PhantomVAI Custom Loader Attacks Users with RunPE Uses Utility
Recently identified in global phishing campaigns, the sophisticated custom loader PhantomVAI delivers various stealers and remote access trojans (RATs) to compromised systems. This malware loader...
Recently identified in global phishing campaigns, the sophisticated custom loader PhantomVAI delivers various stealers and remote access trojans (RATs) to compromised systems.
This malware loader operates by masquerading as legitimate software and employing process hollowing techniques to inject malicious payloads into Windows processes.
Security researchers across multiple organizations have documented this threat under different names, creating confusion in the cybersecurity community about its true identity and capabilities.
The loader targets users worldwide through diverse phishing lures embedded in malicious email attachments and links.
Once executed, PhantomVAI downloads remote payloads and injects them into legitimate Windows processes, making detection significantly more challenging.
The malware has been associated with delivering notorious threats including Remcos, XWorm, AsyncRAT, DarkCloud, and SmokeLoader across various geographical regions.
Intrinsec analysts identified that multiple security vendors documented this loader independently, assigning different names such as VMDetectLoader and Caminho Loader to the same threat.
This naming inconsistency stems from different organizations analyzing the loader’s various components separately.
Researchers discovered that all instances share critical characteristics: the presence of a “VAI” method, Portuguese strings within the code, and masquerading as “Microsoft.Win32.TaskScheduler.dll” based on a legitimate GitHub project.
Technical Architecture and Execution Flow
The loader’s core functionality relies on a RunPE utility called “Mandark,” developed by HackForums user “gigajew” and open-sourced several years ago.
This utility performs process hollowing by creating a suspended legitimate process, unmapping its memory, and injecting malicious code.
The namespace “hackforums.gigajew” found within the loader’s code confirms this connection to the original utility.
PhantomVAI specifically abuses version 2.11.0.0 of the legitimate Microsoft Windows Task Scheduler library.
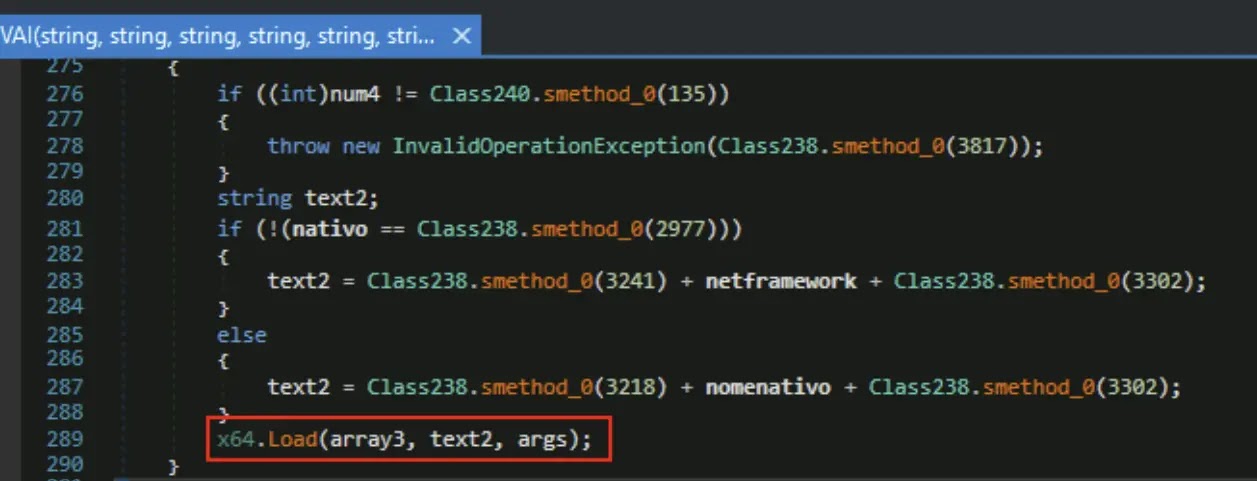
The malware extracts relevant fields from the downloaded payload’s header, including image size, headers size, entry point, and base address.
It then starts a host process, allocates memory with read/write/execute permissions, and copies both PE headers and sections into the allocated memory.
The loader patches processor registers to ensure correct import resolution and relocation before resuming the thread to execute the malicious payload.
The threat operates under a suspected loader-as-a-service model, evidenced by the large variety of payloads delivered and the acceptance of arbitrary payload URLs as arguments.
This model allows multiple threat actors to leverage the same infrastructure for different malicious campaigns, contributing to the widespread nature of attacks observed globally.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.