Silver Fox Uses Stolen EV Certs in AtlasCross Abuses Certificates
A sophisticated AtlasCross RAT campaign is currently underway, orchestrated by the Chinese-nexus advanced persistent threat (APT) group Silver Fox. This threat actor, also known as Void Arachne and...
A sophisticated AtlasCross RAT campaign is currently underway, orchestrated by the Chinese-nexus advanced persistent threat (APT) group Silver Fox. This threat actor, also known as Void Arachne and SwimSnake, is specifically targeting Chinese-speaking users and professionals.
Security researcher Maurice Fielenbach of Hexastrike found that threat actors leveraging typosquatted domains impersonating trusted software brands like Surfshark, Signal, and Zoom use stolen Extended Validation (EV) code-signing certificates to bypass automated security checks and establish deep persistence within enterprise networks.
The threat actors established an extensive infrastructure network to host polished landing pages mimicking legitimate application vendors. When victims attempt to download the software, they receive a ZIP archive containing a triple-nested Setup Factory installer.
To masquerade as legitimate software, the attackers signed the payloads using a stolen EV certificate issued to a Vietnamese entity, “DUC FABULOUS CO.,LTD,” which remains valid until May 2027.
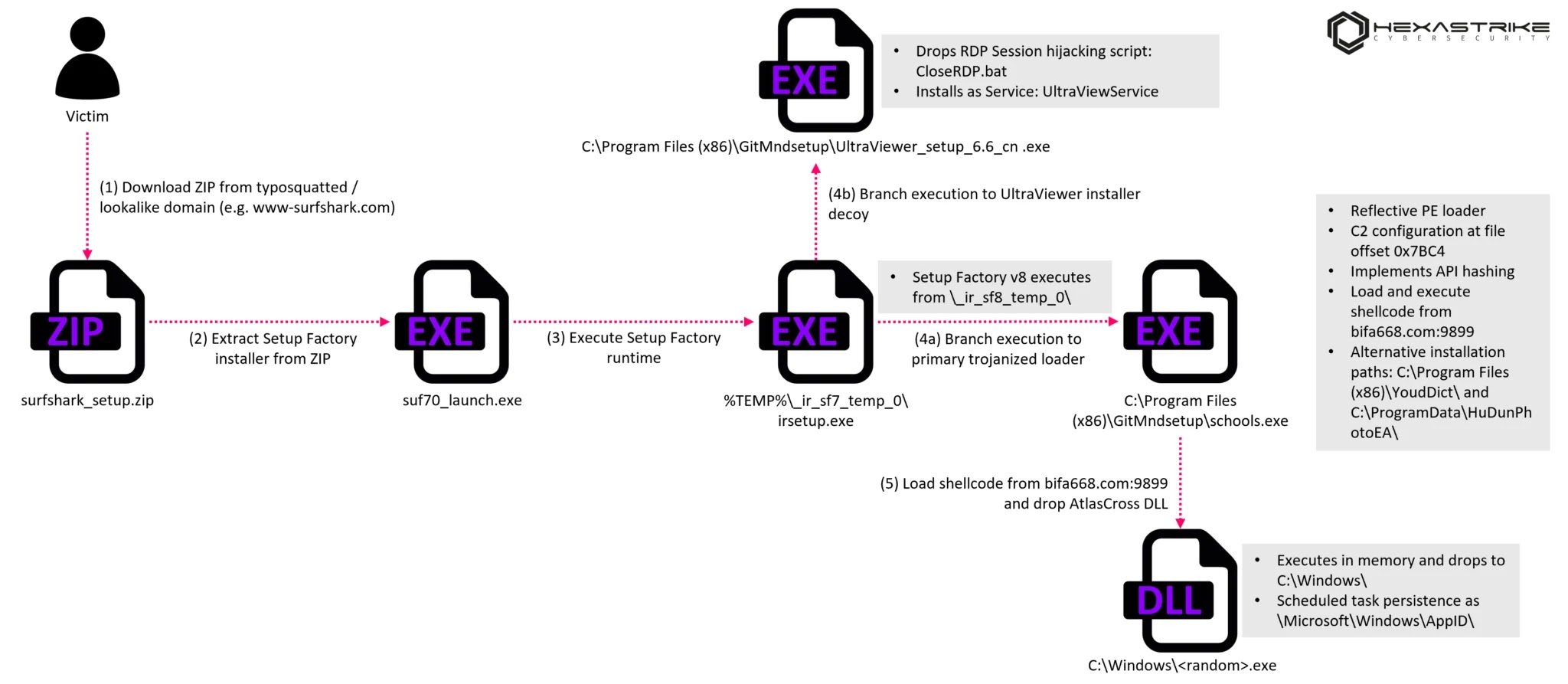
This outer wrapper drops a trojanized Autodesk component, dubbed Schools.exe, alongside legitimate decoy applications such as UltraViewer, to allay user suspicion.
Upon execution, the trojanized loader dynamically resolves its application programming interfaces (APIs) via Process Environment Block (PEB) walking and ROR13 hashing, effectively evading static analysis.
It then extracts an embedded Gh0st RAT-style configuration and retrieves a second-stage shellcode payload from its command-and-control (C2) server over raw TCP, Maurice Fielenbach added.
A reflective loader subsequently maps the AtlasCross RAT into memory, executing it entirely filelessly without writing the final payload to disk.
AtlasCross RAT and the PowerChell Framework
At the core of this operation is the AtlasCross RAT, equipped with a custom native C/C++ PowerShell execution engine named PowerChell. This framework directly hosts the .NET Common Language Runtime (CLR) within the malware process, allowing it to execute PowerShell scripts without ever spawning powershell.exe.
PowerChell systematically neuters host defenses by patching memory to disable the Antimalware Scan Interface (AMSI), disabling Event Tracing for Windows (ETW), bypassing Constrained Language Mode (CLM), and completely suppressing ScriptBlock logging.
The RAT maintains communication with its C2 infrastructure using ChaCha20 encryption, leveraging per-packet random keys generated by hardware random number generators.
To ensure operational longevity, AtlasCross actively terminates TCP connections established by popular Chinese security products, including 360 Total Security and Huorong.
This subtle disruption methodology prevents these tools from receiving cloud-based signature updates without conspicuously killing their host processes.
Additionally, the malware performs targeted DLL injection into WeChat (Wxfun.dll) for data harvesting and utilizes a bundled script leveraging tscon.exe to hijack active Remote Desktop Protocol (RDP) sessions.
Indicators of Compromise (IOCs)
Defense teams are advised to hunt for the following infrastructure and payload indicators observed between November 2025 and March 2026.
| Indicator Type | Value / Details | Description |
|---|---|---|
| Stolen EV Certificate | 2C1D12F8BBE0827400A8440AF74FFFA8DCC8097C |
DUC FABULOUS CO.,LTD (Valid through May 2027) |
| C2 Domain & IP | bifa668.com / 61.111.250[.]139 |
Primary raw TCP C2 communication (Port 9899) |
| Malicious Network Beacon | 53 46 75 63 6b 00 00 00 |
Hex value for “SFuck” sent during C2 handshake |
| Typosquatted Domain | www-surfshark[.]com |
Surfshark VPN lure delivery domain |
| Typosquatted Domain | signal-signal[.]com |
Signal encrypted messenger lure delivery domain |
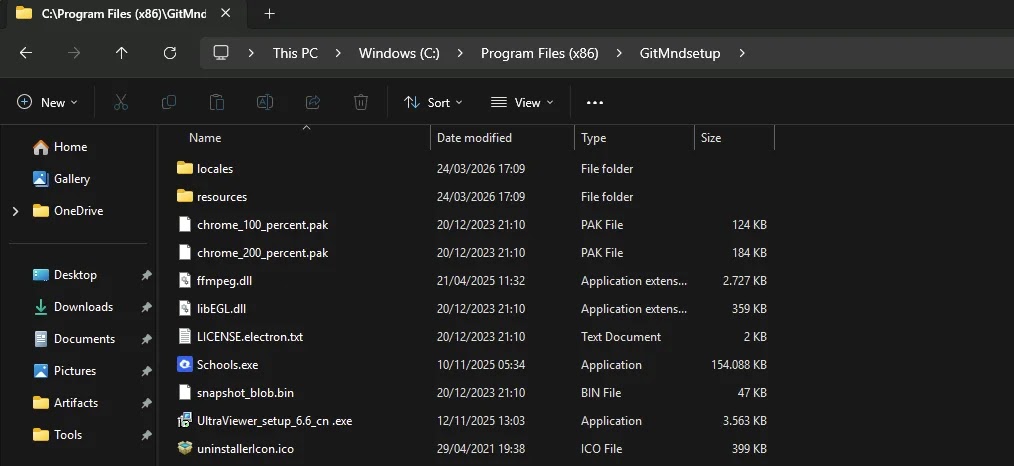
| Staging Directory | C:Program Files (x86)GitMndsetup |
Dropped payload and decoy application folder |
Silver Fox’s transition from driver-based process termination to network-level security disruption showcases a rapidly maturing threat actor.
Security teams should proactively monitor for non-standard processes loading System.Management.Automation.dll and audit scheduled task creation under the MicrosoftWindowsAppID path to detect PowerChell execution within their environments.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.