Fake Screenshots Infect Web3 Support Staff with Multi-Stage Malware
The threat group APT-Q-27 is waging an active campaign targeting Web3 customer support teams. Attackers are using fake screenshot links, delivered via live chat windows, to silently install a...
The threat group APT-Q-27 is waging an active campaign targeting Web3 customer support teams. Attackers are using fake screenshot links, delivered via live chat windows, to silently install a persistent backdoor on victim machines, according to a
The group, also tracked as GoldenEyeDog, has been active since at least 2022 and carries a strong history of targeting the gambling and cryptocurrency sectors.
Prior campaigns relied on trojanized software and watering hole sites, but this operation marks a clear shift in strategy. Instead of waiting for victims to stumble onto a malicious page, the attackers come directly to the support queue, posing as confused customers seeking help with a transaction.
ZeroShadow analysts identified this campaign after their partners at 1inch flagged unusual activity in their support queue — multiple help requests from different accounts and rotating IP addresses, each following the same pattern: a shortlink disguised as a screenshot.
ZeroShadow tracked the tooling, mapped the infrastructure, and traced the activity back to APT-Q-27 with moderate confidence.
What the attackers delivered was a sophisticated, multi-stage malware package. The victim receives a link in chat that appears to go to a Google-hosted image.
Clicking it downloads a file with a name that looks like a photo. On Windows, file extensions are hidden by default, making the file look like an ordinary image.
The file uses the .pif format — an obscure executable type that most people would never recognize as a threat. Opening it displays what looks like a broken web page, while malware installation runs silently in the background.
The final implant communicates with 37 hardcoded command-and-control servers over TCP port 15628 and registers itself as a Windows service named “Windows Eventn” — a deliberate misspelling designed to blend into a service listing.
The malware also silently disables User Account Control across three separate registry keys, removing a key layer of Windows protection without the victim ever seeing a prompt.
Inside the Attack: DLL Sideloading and Staged Delivery
Once the lure file executes, it reaches out to an AWS S3 bucket to fetch a manifest file — a remotely updatable list of URLs pointing to the next set of components.
This design allows the attackers to rotate their infrastructure without ever modifying the malware itself.
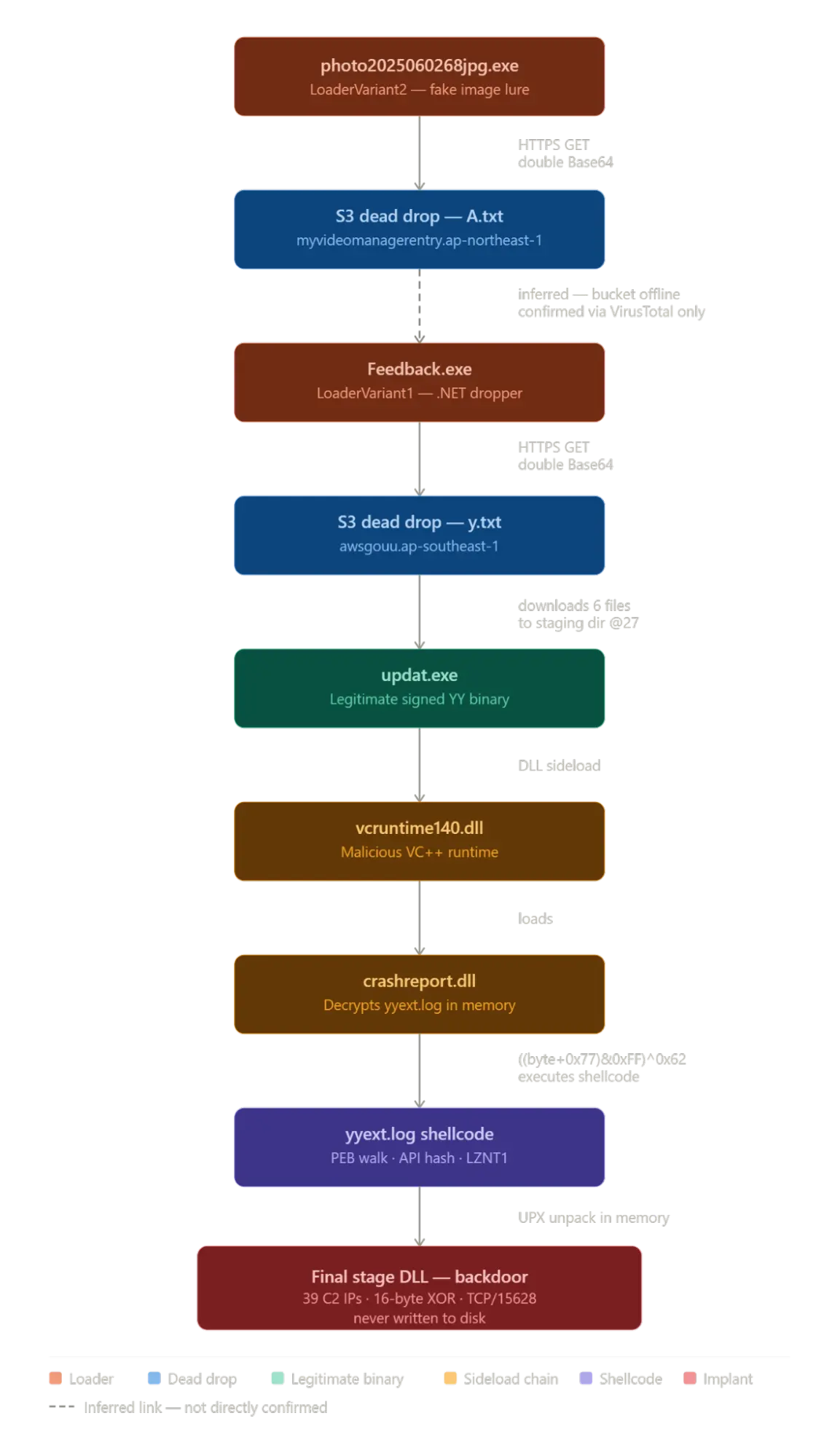
The downloaded package includes a legitimate, signed binary from the YY platform called updat.exe, alongside malicious copies of two standard Windows runtime files — vcruntime140.dll and msvcp140.dll.
Since Windows searches the application’s working directory before the system folder when loading dependencies, launching updat.exe from the staging directory causes it to load the malicious DLLs instead of the real ones.
The signed binary runs cleanly but loads the attacker’s code — a technique known as DLL sideloading.
The malicious DLL, crashreport.dll, reads an encrypted file called yyext.log, decrypts it in memory, and executes the resulting shellcode without writing a file to disk. This step sidesteps memory scanning tools that hunt for injected executables.
The shellcode then decompresses a final backdoor implant — around 340KB — entirely within process memory, leaving no file artifact behind.
For persistence, the loader writes a registry startup key using the name “SystemUpdats” — a deliberate misspelling of the legitimate “SystemUpdate” — ensuring the malware launches every time the machine reboots.
The staging directory mimics the Windows Update cache path, and every installation includes a hardcoded @27 tag in the directory name, serving as a reliable detection signature.
System administrators should enable visible file extensions on all workstations, as this alone would expose the lure file for what it is.
Security teams should block all outbound connections on TCP port 15628 and add the 37 known C2 IP addresses to network blocklists.
Monitoring for the registry value “SystemUpdats” and staging directories containing the @27 suffix will surface active infections.
Detection rules should also alert on simultaneous disablement of all three UAC registry keys, as no legitimate software performs this action.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.