Silver Fox Phishing Targets Japanese Businesses with Tax Lures
Japan’s tax season has become a prime hunting ground for Silver Fox, a well-organized threat actor. This group is actively targeting Japanese businesses with sophisticated tax-themed phishing...
Japan’s tax season has become a prime hunting ground for Silver Fox, a well-organized threat actor. This group is actively targeting Japanese businesses with sophisticated tax-themed phishing campaigns, as detailed in recent findings. Attackers leverage these lures to compromise systems and facilitate data exfiltration, posing a significant risk to corporate security. A comprehensive analysis of this emerging threat is available in this
As Japanese companies enter their annual cycle of tax filing, salary reviews, and personnel changes, this group is taking full advantage of the moment — sending highly targeted spearphishing emails designed to look like routine internal communications.
The campaign currently targets manufacturers and various other businesses across Japan, exploiting a time when employees are naturally expecting emails about financial and HR matters.
Silver Fox has been active since at least 2023. The group initially focused on Chinese-speaking targets before expanding operations into Southeast Asia, Japan, and potentially North America, running each campaign in the local language.
Over the years, the group has targeted a wide range of industries — finance, healthcare, education, gaming, government, and even cybersecurity.
This broad reach shows that Silver Fox is not a one-trick operation; it adapts its tactics to fit the environment and the season.
This latest campaign against Japan is a continuation of a pattern observed during the same period last year, confirming that the group deliberately times its attacks around predictable business cycles.
WeLiveSecurity analysts identified this ongoing campaign and noted that Silver Fox’s emails are not generic blasts. The attackers conduct prior reconnaissance on each target, gathering real employee names and even CEO identities to use as spoofed senders.
Each email includes the target company’s name directly in the subject line, making the message feel like a legitimate internal notification.
Subject lines reference topics such as tax compliance violations, salary adjustments, employee stock ownership plan changes, and personnel updates — exactly the kind of messages employees expect and trust during this busy season.
This level of pre-attack research is what separates Silver Fox from lower-tier threat actors and makes its campaigns significantly harder to spot.
The emails carry either malicious attachments or links that lead to pages where victims are instructed to download a file.
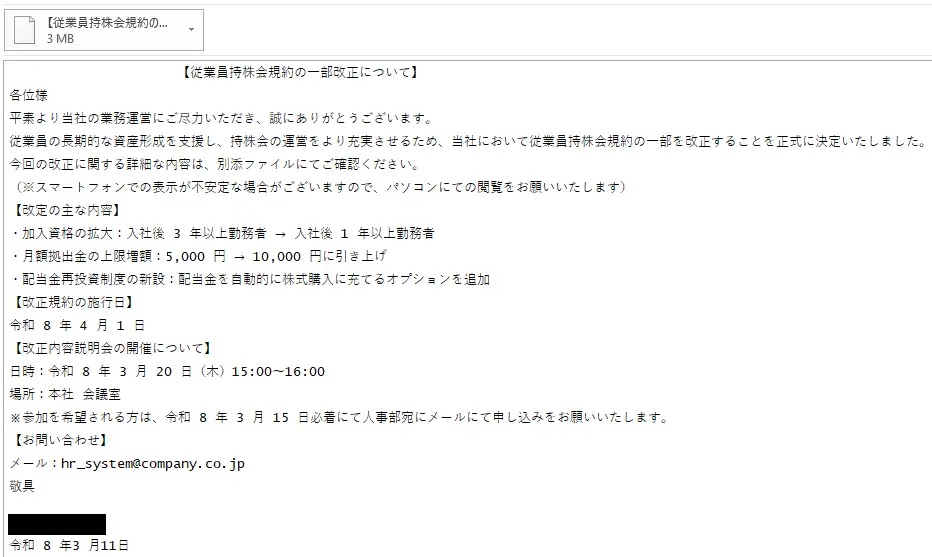
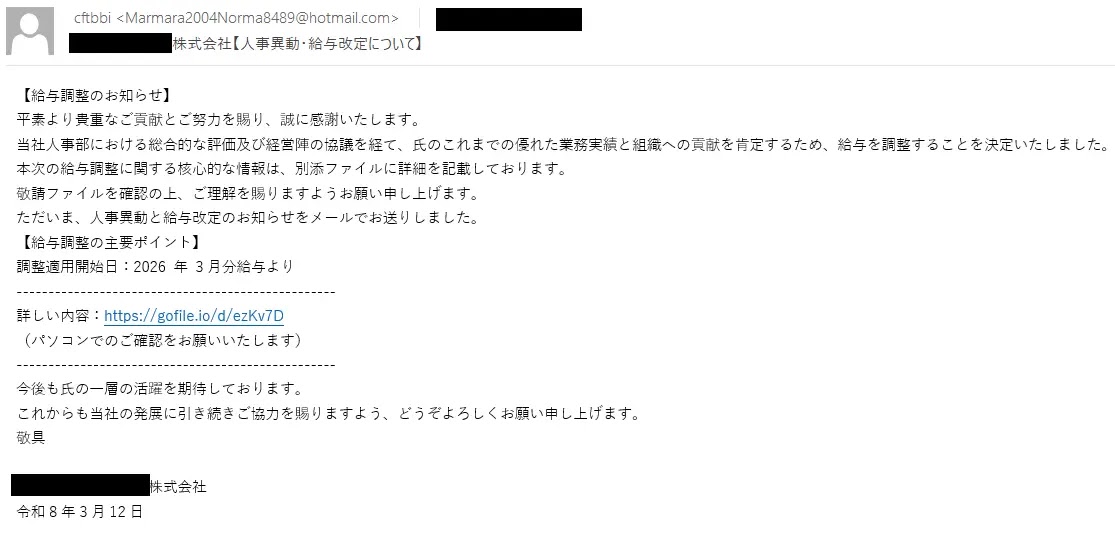
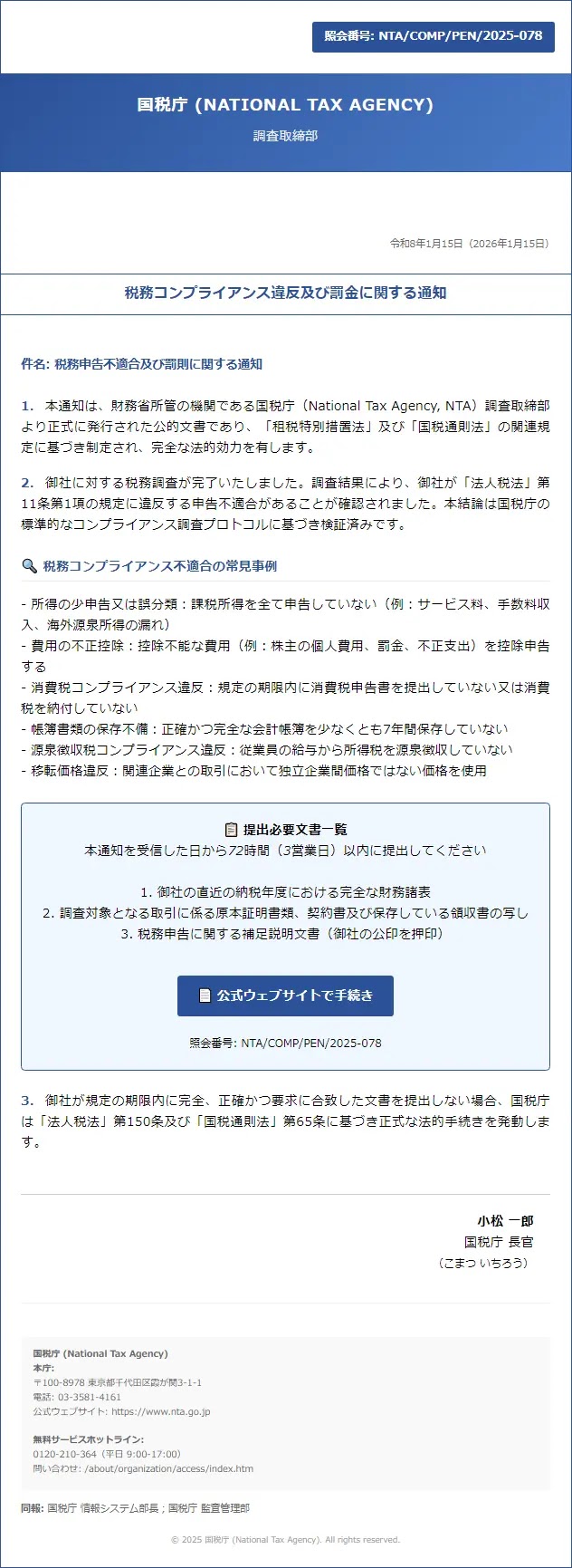
These shows the examples of spearphishing emails distributed on March 11 and March 12, 2026, respectively, while a tax-related lure webpage used to push the malicious download.
Opening any of these files drops ValleyRAT onto the victim’s machine — a remote access trojan that ESET products detect as Win64/Valley. Once installed, ValleyRAT gives the attacker full remote control of the compromised system.
This allows them to steal sensitive data, monitor user activity, and move deeper into the network to set up further stages of the attack.
How the Attack Is Structured
The infection chain behind this particular campaign is straightforward but effective. After a victim opens the malicious file — typically disguised as a salary notice or HR document — ValleyRAT silently takes hold of the system.
The trojan then maintains persistence in the environment, meaning it continues running even after restarts, keeping the attacker’s access alive over time.
The files are often delivered through publicly available file-hosting services such as gofile[.]io or WeTransfer, which adds another layer of deception since these are recognizable platforms.
Archives in RAR or ZIP format are commonly used to package the payload, making it less immediately obvious to the recipient.
To reduce the risk of falling victim to this campaign, WeLiveSecurity researchers recommended that employees verify any email about salary changes, tax penalties, or personnel updates through a separate channel — such as a phone call or a direct message — before taking any action.
Recipients should also check whether the sender’s email address actually matches the name displayed, as mismatches are a common sign of spoofing.
Employees should also be cautious if the language in the email feels unusually stiff or formal, since Silver Fox operators are not native Japanese speakers and subtle phrasing errors sometimes appear in the messages.
Organizations are also advised to keep security software up to date and to promptly report any suspicious email to the IT or security team, even when the email appears routine at first glance.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.