Hackers Deploy BRUSHWORM and BRUSHLOGGER Against South Asian
A South Asian financial institution is the latest victim in a focused cyberattack. This operation leveraged two custom-built malware tools: BRUSHWORM, a modular backdoor, and BRUSHLOGGER, a keylogger...
A South Asian financial institution is the latest victim in a focused cyberattack. This operation leveraged two custom-built malware tools: BRUSHWORM, a modular backdoor, and BRUSHLOGGER, a keylogger disguised as a trusted system file.
The attack combined file theft, persistent system access, and real-time keystroke capture, underlining the growing risk that financial organizations across South Asia face from targeted intrusions.
The two malware components were delivered as separate binaries in what appears to be a deliberate operation.
BRUSHWORM, disguised as paint.exe, acted as the primary implant — responsible for establishing persistence, communicating with a remote command-and-control (C2) server, downloading additional payloads, spreading through removable USB drives, and stealing sensitive documents from infected systems.
BRUSHLOGGER, meanwhile, masqueraded as libcurl.dll, a commonly trusted Windows library, through a technique called DLL side-loading.
Its sole function was to silently record every keystroke typed on the compromised machine while also logging the active window title for each session.
Elastic Security Labs researchers identified the malware during an investigation into the targeted financial institution’s infrastructure.
The victim environment had only SIEM-level visibility at the time, which significantly restricted post-exploitation telemetry and made thorough forensic reconstruction difficult.
Through VirusTotal pivoting, researchers also uncovered what appear to be earlier development versions of the backdoor, uploaded under filenames such as V1.exe, V2.exe, and V4.exe, indicating the threat actor was actively improving the toolset before deployment.
Despite the targeted nature of the attack, neither binary relied on meaningful code obfuscation, packing, or advanced protective techniques. The overall code quality was notably weak.
For instance, BRUSHWORM writes its decrypted configuration to disk in cleartext before creating an encrypted copy and then deleting the original — an error-prone sequence that reveals poor development discipline.
Combined with the use of free dynamic DNS infrastructure in testing versions and the absence of a kill switch, researchers assessed with moderate confidence that the malware author is relatively inexperienced and may have used AI code-generation tools during development without fully reviewing the output.
The impact of this attack extended well beyond simple data theft. BRUSHWORM was built to replicate itself across connected USB drives using socially engineered filenames like Salary Slips.exe, Documents.exe, and Dont Delete.exe — names crafted specifically to trick employees in a corporate financial setting into opening them.
BRUSHLOGGER quietly captured every keystroke in parallel, harvesting login credentials, financial inputs, and internal communications throughout the infection period.
BRUSHWORM’s Infection Mechanism and Persistence
One of the most operationally notable aspects of this attack is how BRUSHWORM quietly digs into a system and ensures it stays there.
Upon first execution, the malware creates several hidden directories with hardcoded paths — including C:ProgramDataPhotoesPics for the main backdoor binary and C:UsersPublicLibraries for downloaded modules.
Interestingly, the misspelling of “Photoes” instead of “Photos” appears consistently across both components and is believed to be an authentic mistake by the author, possibly to blend with legitimate user media directories.
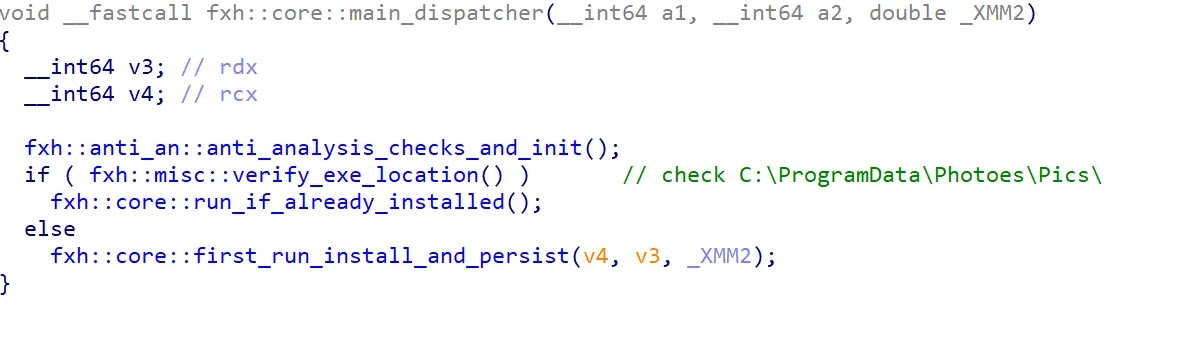
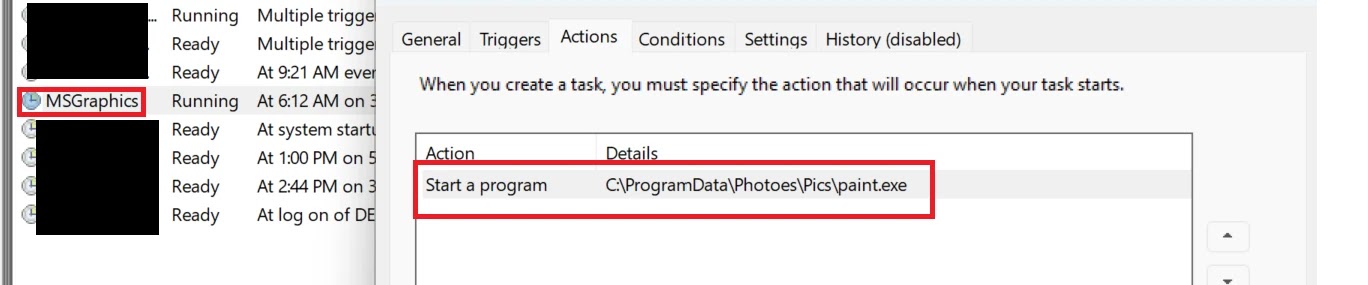
To survive system reboots, BRUSHWORM registers a Windows scheduled task named MSGraphics through the COM Task Scheduler interface, configured to run the backdoor each time a user logs in.
It then fetches a DLL payload from its C2 server at resources.dawnnewsisl[.]com/updtdll using a WinHTTP GET request, saves it as Recorder.dll, and launches it through a second scheduled task named MSRecorder via rundll32.exe.
In environments without active internet access, BRUSHWORM pivots to a physical exfiltration method, copying all stolen files directly to any connected USB drive to bridge air-gapped networks.
Security teams are advised to restrict the execution of unsigned binaries and closely monitor for unusual scheduled task creation, especially tasks named MSGraphics or MSRecorder.
Deploying endpoint detection solutions with USB activity monitoring can block BRUSHWORM’s removable media propagation before it spreads further.
Auditing DLL loading behavior across endpoints is also essential to catch side-loading attempts like those used by BRUSHLOGGER. YARA rules are available to identify both BRUSHWORM and BRUSHLOGGER across endpoints and network environments.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.