Silver Fox Phishing Now Uses Python Stealers in Tax Aud
The China-based threat actor known as Silver Fox, also tracked as Void Arachne, has significantly updated its tactics since early 2025. Previously deploying remote access trojans, the group now...
The China-based threat actor known as Silver Fox, also tracked as Void Arachne, has significantly updated its tactics since early 2025. Previously deploying remote access trojans, the group now distributes a custom Python-based stealer across South Asia.
Active since at least 2022, the group first gained attention through mass infection campaigns that used SEO poisoning to push ValleyRAT, a modular backdoor also known as Winos.
This latest shift reflects how Silver Fox has steadily broadened both its geographic reach and its toolkit, all while using convincing tax authority impersonation lures to gain initial entry.
The campaign unfolded in three waves between 2025 and 2026, targeting entities across Taiwan, Japan, Malaysia, India, Indonesia, Singapore, Thailand, and the Philippines.
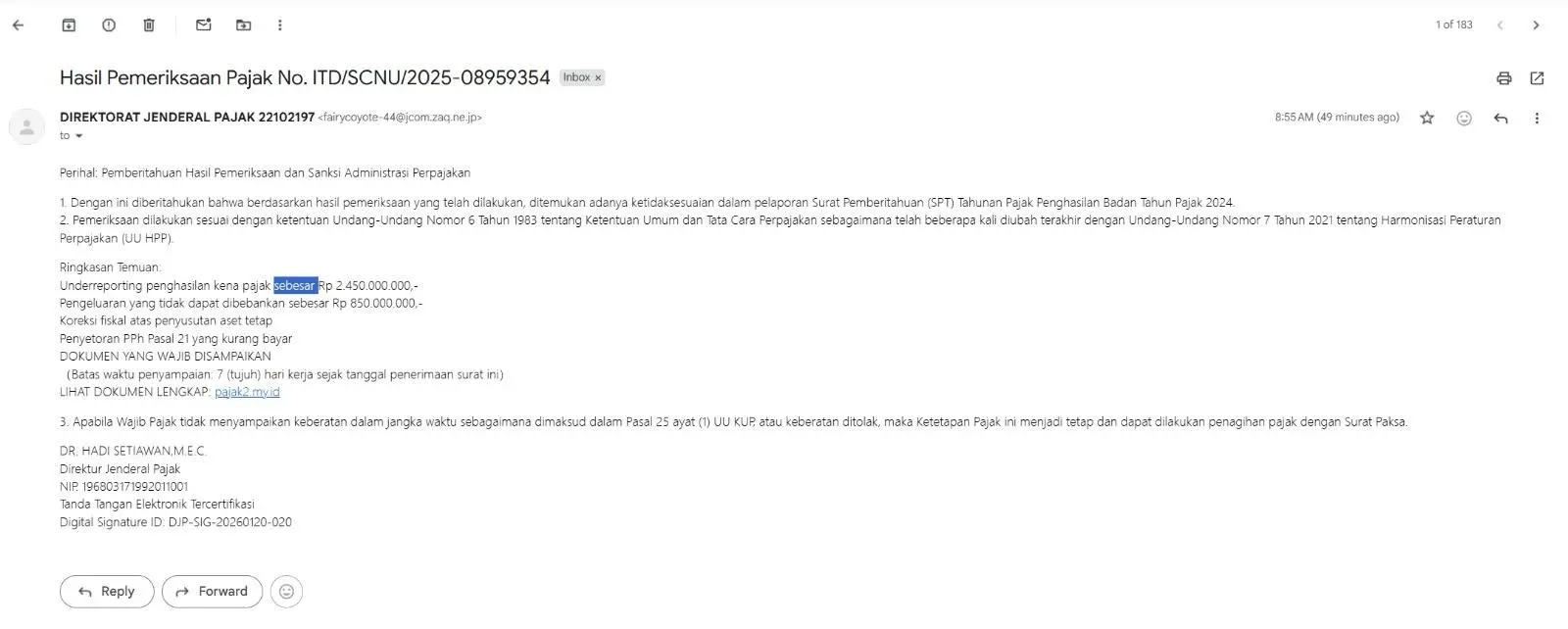
The first wave began in January 2025, when Silver Fox sent phishing emails impersonating Taiwan’s national taxation authority. Each email carried a malicious PDF that, once opened, triggered a hidden annotation leading victims to download a ZIP archive.
That archive held two files — python311.dll and an executable — which together side-loaded ValleyRAT.
Operators deliberately timed this campaign around a real announcement by Taiwan’s Ministry of Finance regarding Year 113 tax audit selections, lending the lure a convincing appearance.
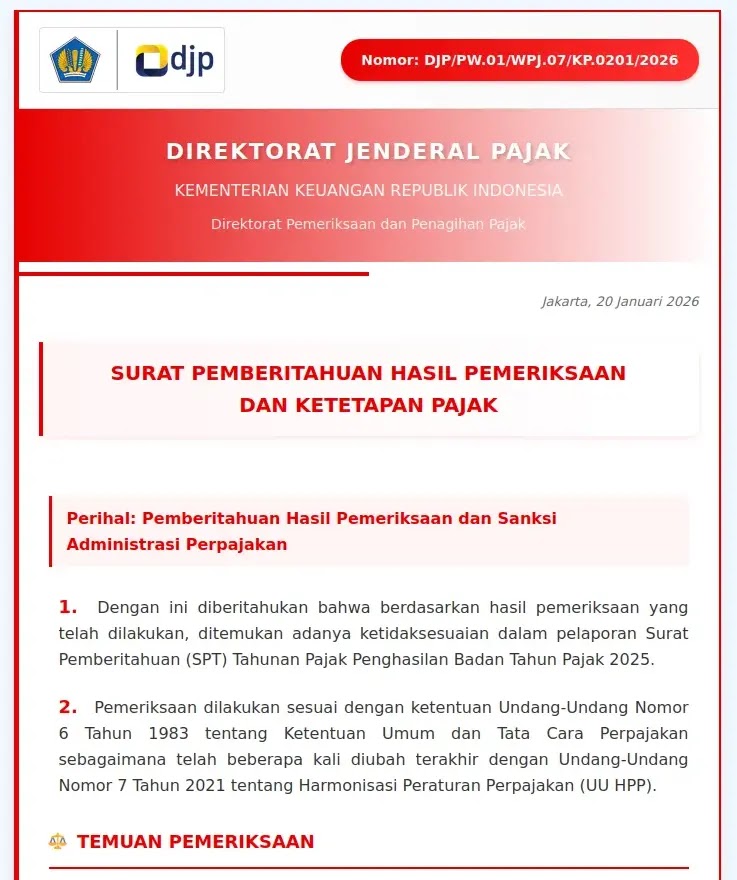
Sekoia analysts identified a second wave in mid-December 2025, when the group widened its targeting and revised its delivery method. Rather than embedding a PDF attachment, the phishing emails now contained a link to a fake tax website tailored to the victim’s country.
Downloading from that site produced an archive holding a legitimate but misconfigured Chinese Remote Monitoring and Management (RMM) tool, signed by “SyncFutureTec Company Limited.”
Silver Fox exploited a flaw in the tool’s configuration by embedding the C2 address directly into the filename, following the pattern [IPv4]ClientSetup.exe, which kept the file’s digital signature untouched and bypassed immediate security checks.
By February 2026, Silver Fox replaced the RMM tool with a compiled Python stealer, marking its third wave. The phishing website was written in Malay, indicating Malaysia as the primary target at this stage.
The stealer ran disguised as a WhatsApp backup application, using the User-Agent WhatsAppBackup/1.0 while communicating with a C2 server at xqwmwru[.]top.
On infected machines, it left behind C:WhatsAppBackupWhatsAppData.zip and a lock file in the %TEMP% directory. The C2 infrastructure was styled to resemble a legitimate WhatsApp web server.
Python Stealer Infection Chain
The Python stealer’s infection chain begins when a victim opens a phishing email and clicks an embedded link, landing on a tax-themed website that mirrors a trusted government portal.
The victim is then prompted to download an archive — either a ZIP or RAR file — that unpacks into a single PE32+ executable.
Running this file launches the stealer disguised as a WhatsApp backup utility, after which it begins gathering credentials, browser data, stored files, and other sensitive material from the infected device.
Collected data is compressed and sent to the C2 server through two dedicated endpoints: https://xqwmwru[.]top/upload_large.php for exfiltration and https://xqwmwru[.]top/upload_status.php to confirm transfers.
The C2 panel presents a structured backend built to manage stolen information across multiple victims at scale.
Organizations across South Asia should treat unsolicited tax-related emails with skepticism, particularly those containing attachments or links to file downloads.
Finance teams should get training on how attackers impersonate government tax agencies in phishing campaigns. Security teams should block known malicious domains and C2 addresses, including xqwmwru[.]top and the RMM tool IPv4 addresses published in the threat intelligence report.
Endpoint monitoring tools should alert on the creation of WhatsAppBackup directories and the whatsapp_backup.lock file, both of which serve as clear host-based indicators of compromise.
Inspecting outbound connections to newly registered domains with uncommon TLDs can help identify similar intrusions before data leaves the network.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.