Resecurity Honeypot Traps Hackers in Trapped Resecurity’s
Resecurity leverages synthetic data honeypots as a strategic tool against threat actors, transforming their reconnaissance into actionable intelligence. This approach recently yielded significant...
Resecurity leverages synthetic data honeypots as a strategic tool against threat actors, transforming their reconnaissance into actionable intelligence. This approach recently yielded significant results. It not only ensnared an Egyptian-linked hacker but also successfully misled the ShinyHunters group into announcing false breach claims.
Resecurity has refined deception technologies for counterintelligence, mimicking enterprise environments to lure threat actors into controlled traps.
These build on traditional honeypots, misconfigured services, or dummy resources that passively log intruders, now powered by AI-generated synthetic data that resemble real-world patterns without exposing proprietary information. Previously breached data from dark web sources enhances realism, fooling even advanced actors who validate targets.
On November 21, 2025, Resecurity’s DFIR team spotted a threat actor scanning public-facing services after targeting a low-privilege employee. Indicators included IPs like 156.193.212.244 and 102.41.112.148 (Egypt), plus VPNs 45.129.56.148 (Mullvad) and 185.253.118.70.
Responders deployed a honeytrap in an emulated app with synthetic datasets: 28,000 consumer records (usernames, emails, fake PII from combo lists) and 190,000 Stripe-like payment transactions generated via tools like SDV, MOSTLY AI, and Faker. A bait account, “Mark Kelly,” was planted on Russian Marketplace to draw attackers.
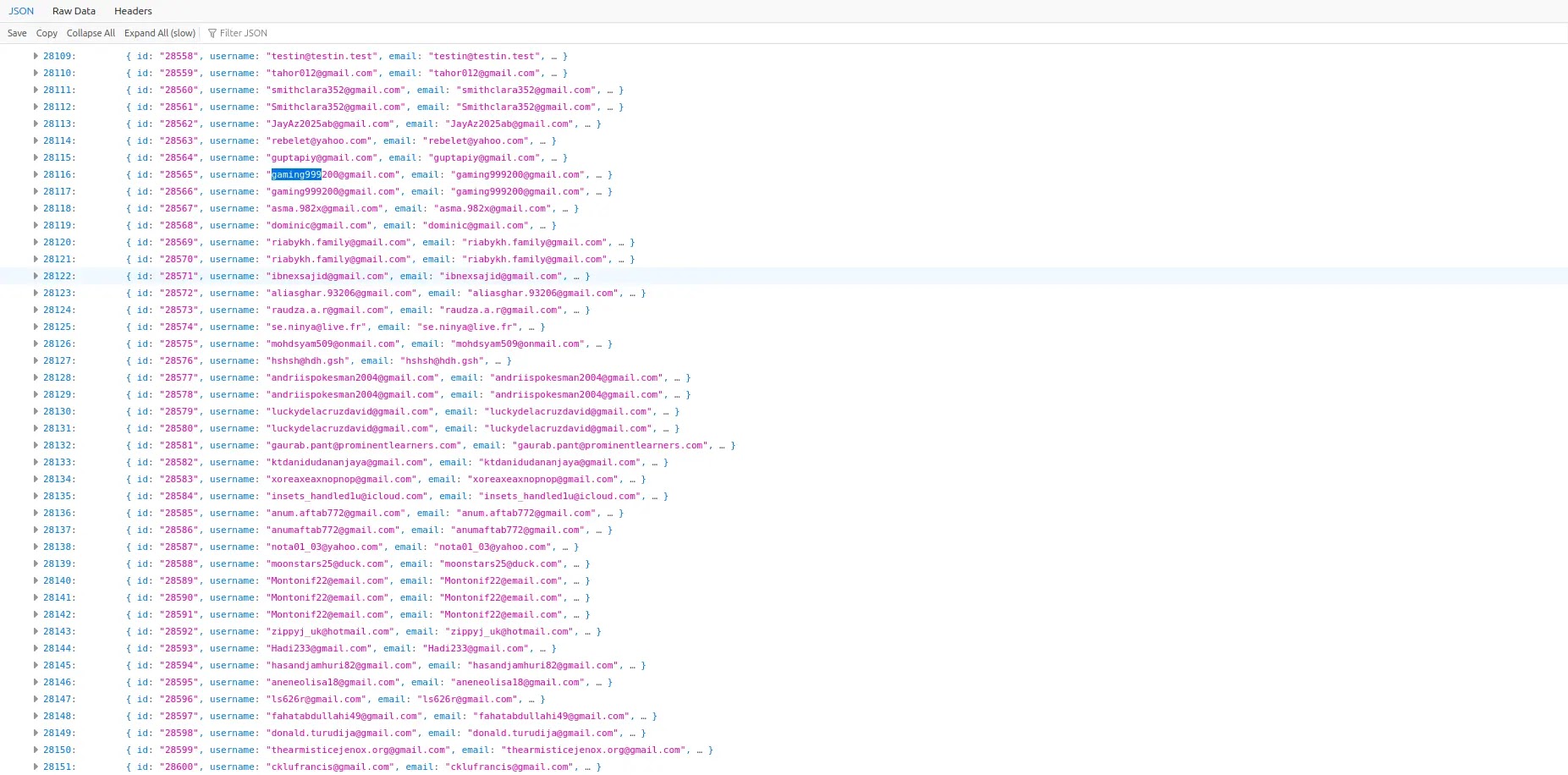
The actor logged into the honeytrap, prompting over 188,000 requests from December 12-24 to scrape data via custom automation and residential proxies.
This yielded “abuse data” on tactics, infrastructure, and OPSEC slips, real IPs leaked during proxy failures. Resecurity blocked proxies, forcing the reuse of known hosts, and shared findings with law enforcement, culminating in a foreign subpoena.
Isolated decoys like Office 365, VPNs, and a decommissioned Mattermost instance with 2023 fake chatter (six groups, AI-generated via OpenAI) proved ideal for high-value mimicry without risk.
ShinyHunters Caught in Update
A January 3, 2026, update revealed ShinyHunters previously profiled by Resecurity fell into the same trap, boasting Telegram “full access” to “[honeytrap].b.idp.resecurity.com” and fake systems.
Screenshots showed dummy Mattermost for “Mark Kelly,” non-existent domains like “resecure.com,” bcrypt-hashed API tokens from duplicate tester accounts, and useless old logs.
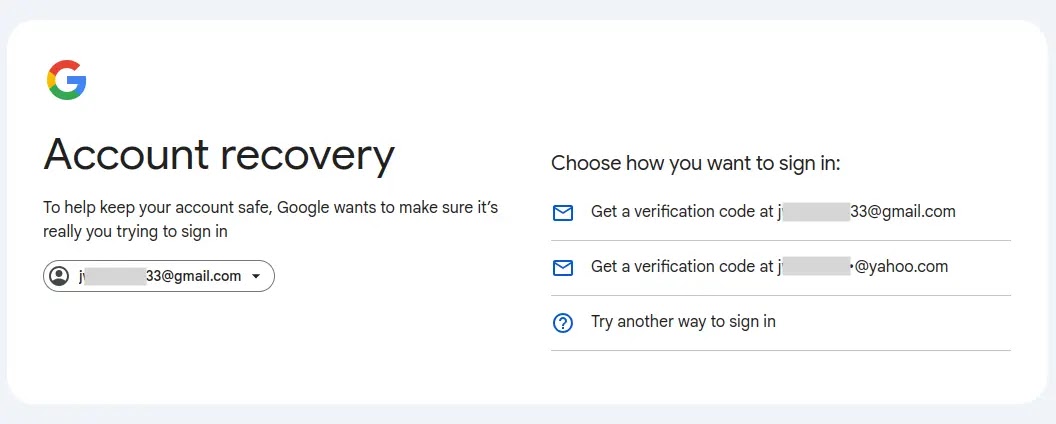
The group acknowledged disruptions caused by Resecurity’s tactics; social engineering identified links to jwh*****[email protected], a US phone number, and a Yahoo account registered during the activity.
This validates cyber deception’s power for threat hunting and investigations, generating IOCs/IOAs from controlled engagements. Compliance with privacy laws remains key.
Resecurity’s logs and prior ShinyHunters exposés suggest retaliation backfired into self-incrimination. Enterprises can replicate via monitored decoys in non-production environments, enhancing proactive defense against financially motivated threat actors.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.