Researcher Reverse Engineers 0-Day Disabling CrowdStrike E
Leading endpoint security solutions, including CrowdStrike Falcon, are vulnerable to a newly disclosed Bring Your Own Vulnerable Driver (BYOVD) attack. A cybersecurity researcher recently uncovered...
Leading endpoint security solutions, including CrowdStrike Falcon, are vulnerable to a newly disclosed Bring Your Own Vulnerable Driver (BYOVD) attack. A cybersecurity researcher recently uncovered this method, which can effectively disable these top-tier defenses.
By reverse-engineering a previously unknown zero-day kernel driver, the researcher revealed how threat actors use legitimately signed drivers to bypass endpoint detection and response (EDR) systems completely.
In BYOVD attacks, hackers deploy a trusted but flawed driver on a compromised machine to exploit its elevated kernel privileges.
The investigation identified over 15 distinct variants of this malicious driver. Despite their destructive capabilities, all variants carry valid Microsoft digital signatures and have not been blocked or revoked by the vendor.
Alarmingly, scans on platforms like VirusTotal show zero detections from modern antivirus engines.
Because the driver is signed and highly trusted, Windows allows it to load into kernel mode without triggering any security alerts, giving attackers a stealthy foothold.
Reverse Engineering the IOCTL
During technical analysis using IDA Pro, the researcher bypassed an obfuscated entry point to examine the driver’s core device-control handler.
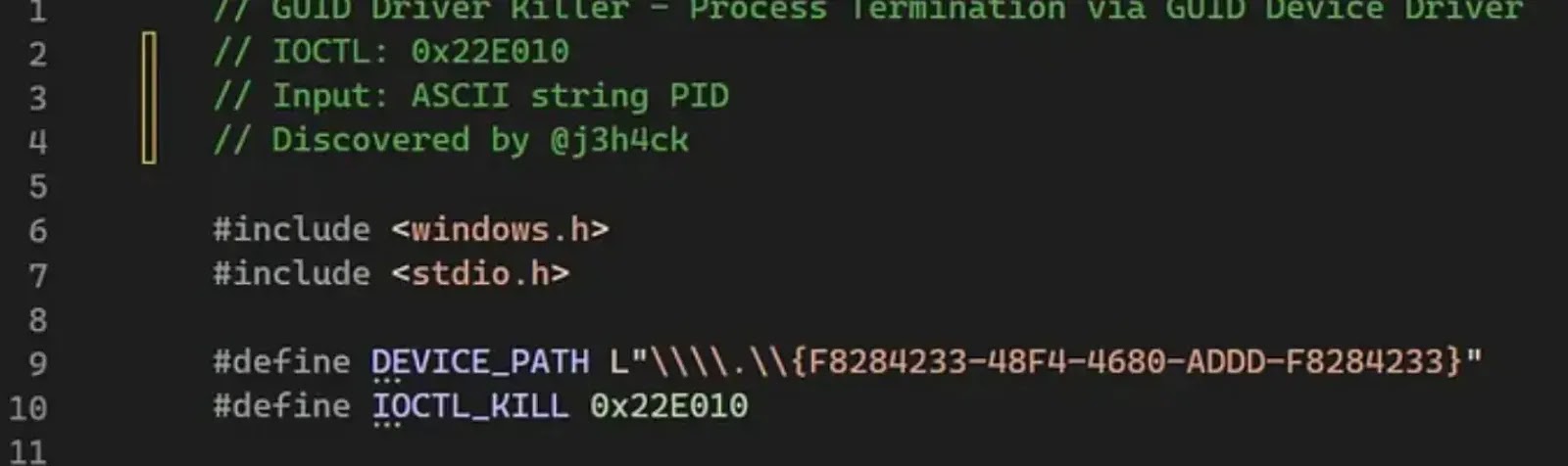
After cleaning up the heavily mangled decompiled code, they discovered a dangerous input/output control (IOCTL) interface. Specifically, the IOCTL code 0x22E010 triggers a dedicated process-killing routine.
The driver accepts a process ID as a string, converts it to an integer using standard C functions, and then executes the termination command. The true danger lies in how the driver terminates security processes from the kernel level.
It uses the ZwOpenProcess and ZwTerminateProcess kernel functions to terminate active applications forcibly.
In standard user mode, attempting to close a Protected Process Light (PPL) service, such as CrowdStrike, results in an immediate access denial.
However, kernel-level commands bypass these user-mode protections entirely, allowing the driver to silently kill critical security agents before attackers deploy ransomware or other secondary payloads.
To validate the vulnerability, the core-jmp researcher dynamically tracked the driver in a test environment to locate its symbolic link, identified as \.{F8284233–48F4–4680-ADDD-F8284233}.
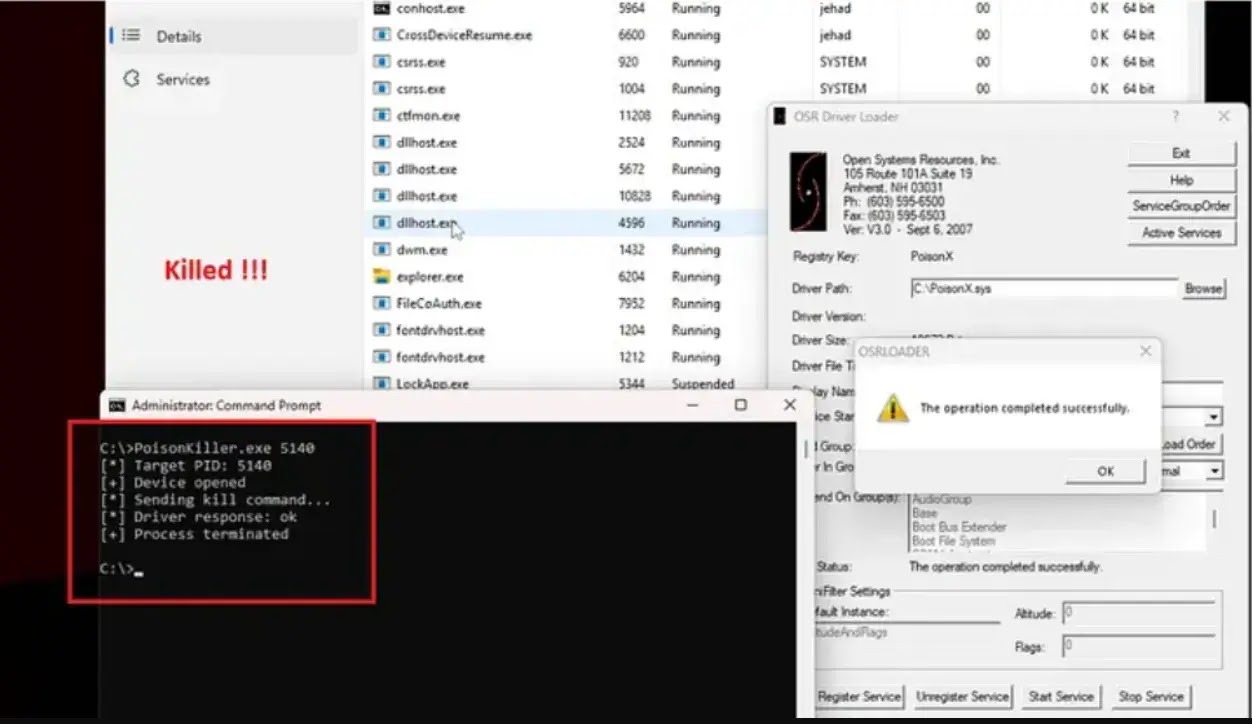
Using this link alongside the discovered IOCTL code, they developed a custom proof-of-concept exploit named PoisonKiller.
When loaded via standard command-line service tools, the exploit successfully targeted and terminated the active CrowdStrike EDR process.
The complete technical analysis and exploit code have been published on GitHub, highlighting a critical blind spot in how modern operating systems handle signed third-party drivers.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.