PlugX USB Worm Spreads Globally via DLL Sideload Across Multiple
A newly discovered PlugX worm variant is exploiting USB drives for global propagation, silently crossing borders. It has already been detected across multiple continents, spanning nearly ten time...
A newly discovered PlugX worm variant is exploiting USB drives for global propagation, silently crossing borders. It has already been detected across multiple continents, spanning nearly ten time zones.
First spotted in Papua New Guinea in August 2022, the worm resurfaced in January 2023 in both Papua New Guinea and Ghana — two countries roughly 10,000 miles apart.
Infections were later confirmed in Mongolia, Zimbabwe, and Nigeria, making this one of the more geographically spread malware outbreaks in recent memory.
PlugX itself is not new. It is a well-known remote access Trojan (RAT) of Chinese origin that has been used by threat actors for years.
What makes this particular variant stand out is a fresh payload and its ties to a command-and-control (C2) server that was not previously linked closely to this malware family.
The worm uses DLL sideloading — a technique where a legitimate application is tricked into loading a malicious library instead of the real one — to execute its code without raising immediate suspicion.
Sophos X-Ops researchers, led by analyst Gabor Szappanos, identified this new variant after a CryptoGuard alert was triggered, most likely by a data exfiltration attempt.
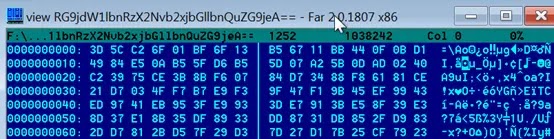
The infection package consists of a legitimate AvastSvc.exe executable that is vulnerable to DLL sideloading, a malicious DLL named wsc.dll, and an encrypted payload file.
All three components work together to quietly run the PlugX backdoor on a compromised machine.
The C2 activity traced back to the IP address 45.142.166[.]112, which was previously mentioned in a 2019 report by Unit 42 as loosely connected to PlugX but not directly tied to any known threat actor at the time.
Sophos researchers now say that all the techniques observed during their investigation align with the known behavior of PKPLUG, also called Mustang Panda — a China-linked advanced persistent threat (APT) group.

This finding strengthens the connection between the IP address and the threat actor behind this campaign.
DLL Sideloading and USB-Based Evasion
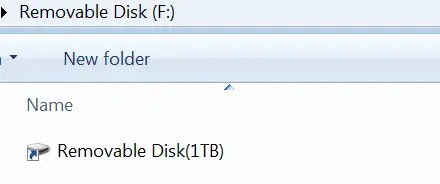
The infection mechanism in this PlugX variant is built around deception. When the worm copies itself onto a USB drive, it uses specific mutex strings — USB_NOTIFY_COP and USB_NOTIFY_INF — to manage the operation.
Once copied, the USB drive appears completely empty to an ordinary Windows Explorer view. What the victim actually sees is a shortcut file designed to look like another removable disk, complete with a matching drive icon.
If a user clicks the shortcut, it quietly runs the CEFHelper executable — which is actually the renamed AvastSvc.exe file. This disguise is deliberate. The worm names it after a legitimate Adobe process to avoid attention.
All other malicious files and directories are given hidden and system attributes, making them invisible by default in standard file listings.
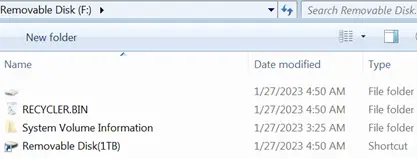
The worm stores all its files inside a directory named RECYCLER.BIN, and it drops a desktop.ini file that makes Windows treat this folder as an actual Recycle Bin.
This means deleted files from the user’s real hard drive appear there, further masking the worm’s presence. Inside RECYCLER.BIN, the malware targets documents including .doc, .docx, .xls, .xlsx, .ppt, .pptx, and .pdf files, encrypts them, and saves them with base64-encoded file names for exfiltration.
Organizations should treat USB drive connections as a serious risk, particularly in environments handling sensitive documents or sensitive data.
Disabling AutoRun and AutoPlay for all removable media is a basic but effective first measure. IT teams should also configure their systems to show hidden and system files by default, which can help spot suspicious directories like RECYCLER.BIN.
Regularly monitoring outbound C2 traffic and deploying endpoint protection capable of catching DLL sideloading activity remain critical steps for any organization facing this type of targeted threat.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.