ErrTraffic Cybercrime Tool Automates ClickFix Attacks
Tool Automates ClickFix Attacks
Listen up, because there’s a new Cybercrime Tool Automates what security experts call ClickFix attacks, where fake error messages push people to manually execute malicious commands.
Unlike older methods that tried to secretly download files, ClickFix works by creating fake problems on websites that seem to require users to fix them by running specific codes.
What makes ErrTraffic particularly concerning is its professional design and low cost, allowing even less skilled criminals to launch effective attacks across multiple platforms including Windows, Android, macOS, and Linux.
The tool was first spotted on Russian-language cybercrime forums in early December 2025, advertised by a threat actor using the name LenAl.
For just $800, criminals can purchase the complete ErrTraffic package, which includes a control panel and script system that creates convincing fake glitches on compromised websites.
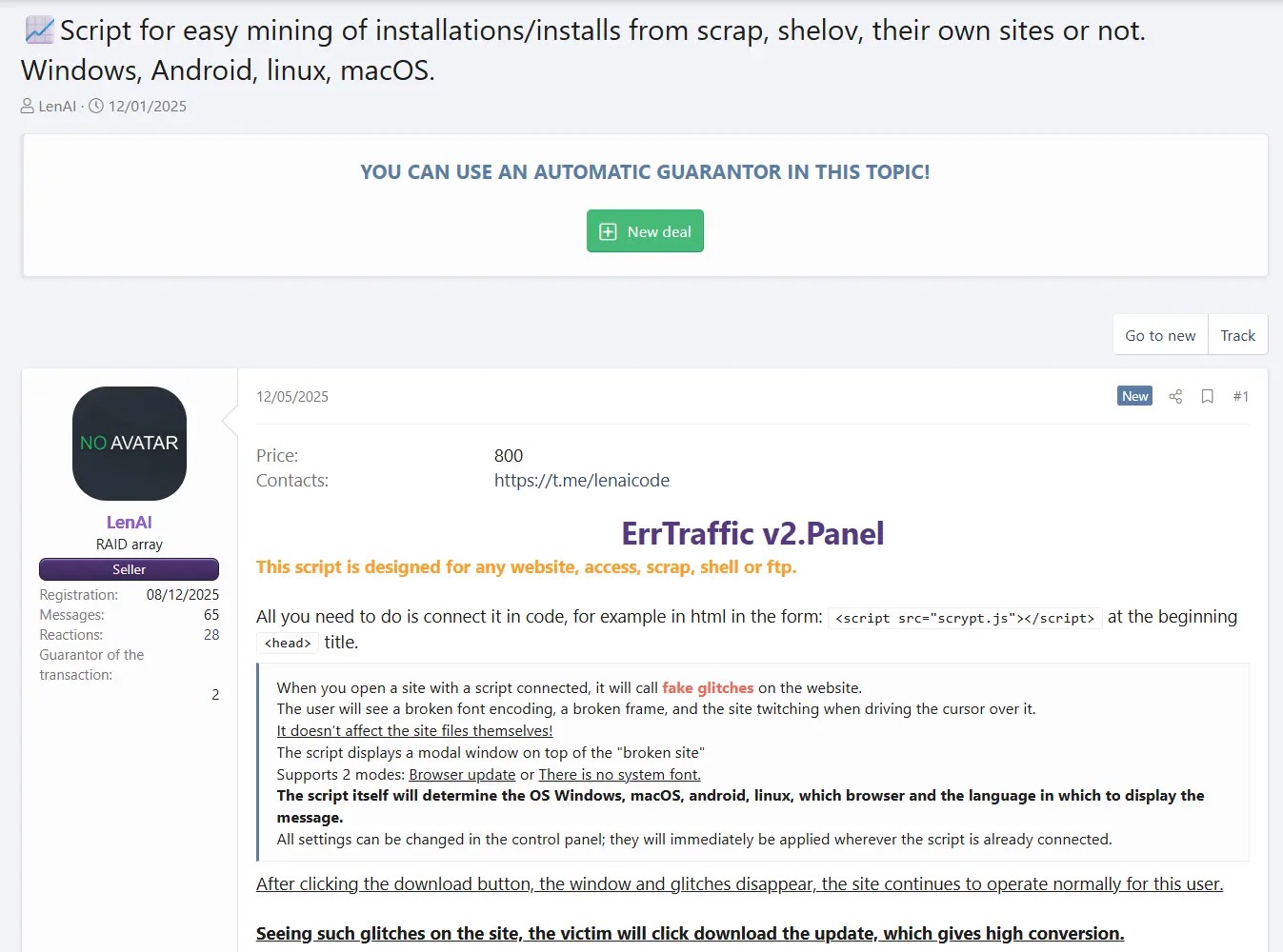
When visitors land on an infected site, they see broken text, scrambled fonts, and visual errors that make the website appear corrupted. A popup window then appears offering to fix the problem through a browser update or missing system font installation.
Hudson Rock Threat Intelligence Team analysts identified the tool after tracking promotional posts and analyzing its technical capabilities.
JavaScript injection
Behind the scenes, ErrTraffic operates through a simple JavaScript injection. Attackers who compromise a website can add one line of code that connects to their control panel.

The script automatically detects what device and browser each visitor uses, then displays a customized fake error message in the appropriate language.
The infection happens when users click the fix button, which copies a PowerShell command to their clipboard and instructs them to paste it into their system.
This technique bypasses traditional security software because browsers see the action as legitimate text copying, and security tools see users opening PowerShell as normal behavior.
Analysis of active ErrTraffic campaigns reveals shocking effectiveness. Dashboard data from real attacks shows conversion rates approaching 60 percent, meaning nearly six out of every ten people who see the fake error message fall for the trick and install malware.
The tool delivers whatever payload the attacker uploads, typically infostealers like Lumma or Vidar for Windows devices, and banking trojans for Android phones.
The control panel even includes geographic filtering, with hardcoded blocks for Russia and neighboring countries to avoid local law enforcement.
Once infected, victim computers can have their login credentials stolen, which criminals then use to compromise more websites and spread the attack further, creating a self-sustaining cycle of infection.









No Comment! Be the first one.